tracee v0.18.1 releases: Container and system event tracing using eBPF
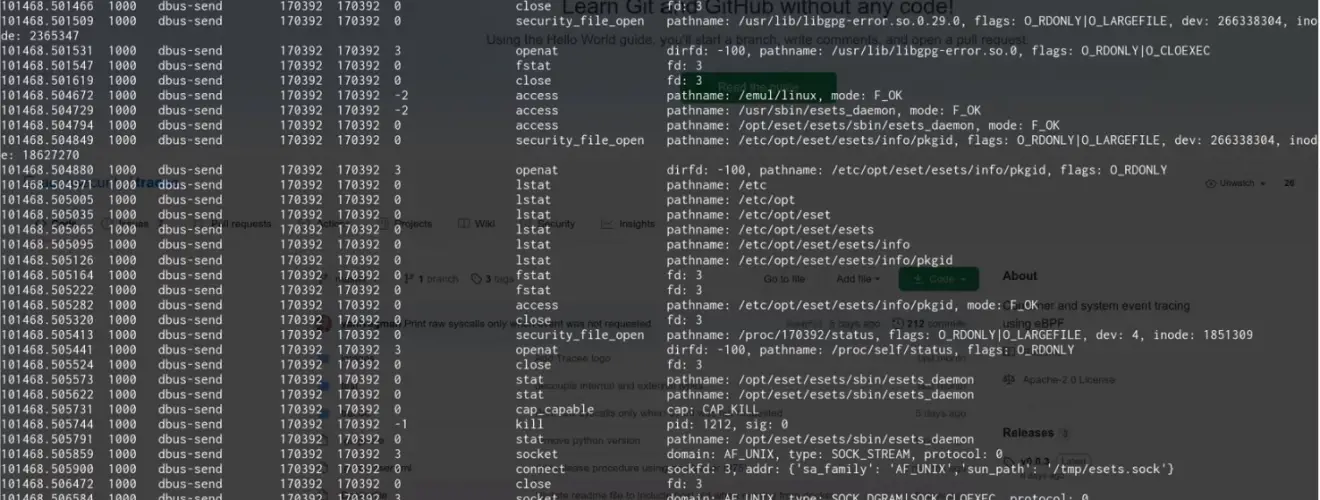
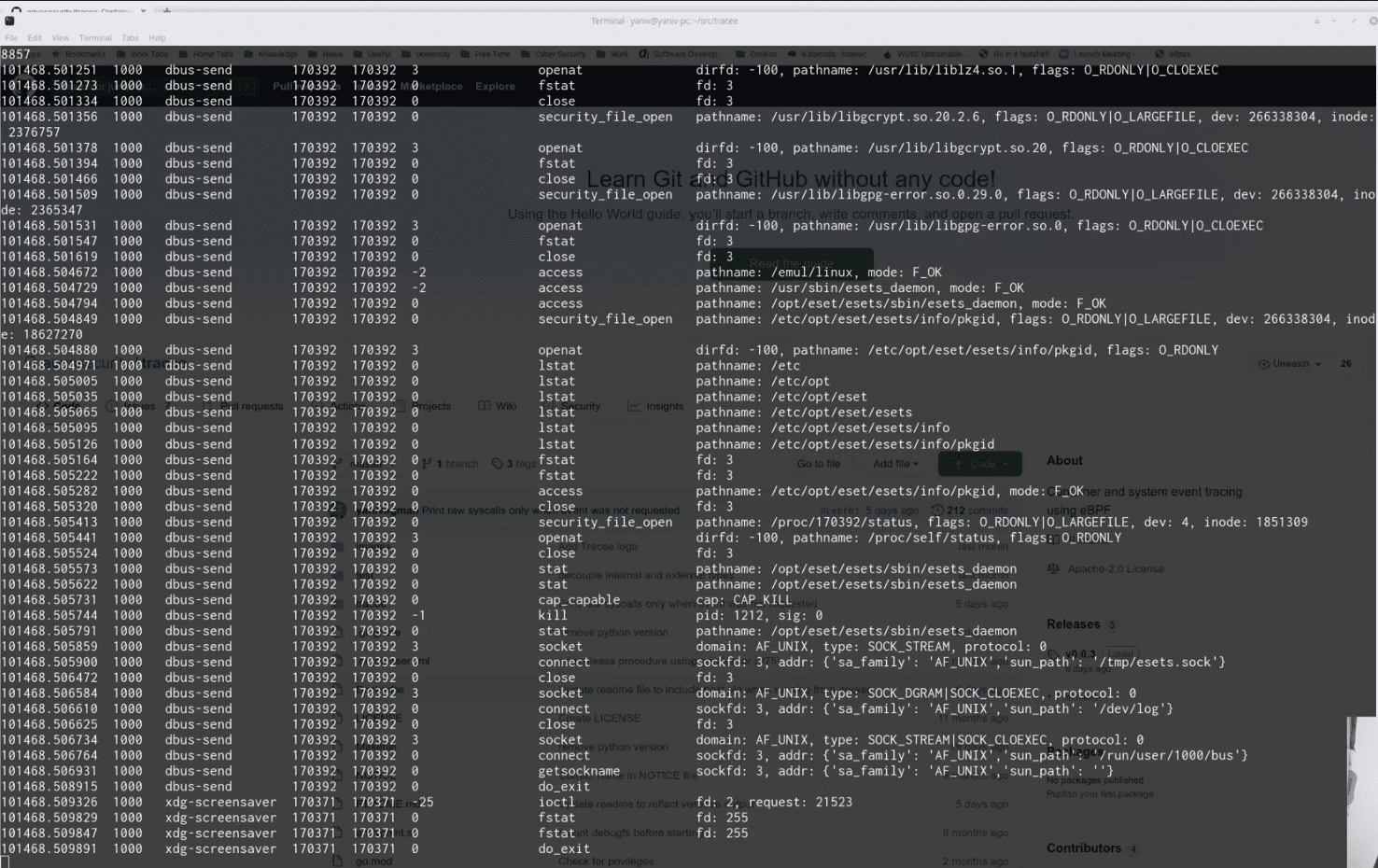
Tracee – Container, and system tracing using eBPF
Tracee is a lightweight and easy-to-use container and system tracing tool. It allows you to observe system calls and other system events in real-time. A unique feature of Tracee is that it will only trace newly created processes and containers (that were started after it has started), in order to help the user focus on relevant events instead of every single thing that happens on the system (which can be overwhelming). Adding new events to Tracee (especially system calls) is straightforward, and will usually require no more than adding few lines of code.
Other than tracing, it is also capable of capturing files written to disk or memory (“fileless”), and extracting binaries that are dynamically loaded to an application’s memory (e.g. when an application uses a packer). With these features, it is possible to quickly gain insights about the running processes that previously required the use of dynamic analysis tools and special knowledge.
Secure tracing
When Tracee reads information from user programs it is subject to a race condition where the user program might be able to change the arguments after it has read them. For example, a program invoked execve(“/bin/ls”, NULL, 0), it picked that up and will report that then the program changed the first argument from /bin/ls to /bin/bash, and this is what the kernel will execute. To mitigate this, it also provides “LSM” (Linux Security Module) based events, for example, the bprm_check event which can be reported by Tracee and cross-referenced with the reported regular syscall event.
Changelog v0.18
- make: set LIBBPFGO_OSRELEASE_FILE default value by @geyslan in #3226
- chore: migrate to golang-lru v2 by @NDStrahilevitz in #3140
- (extensions) probes: create probe group, events: start work by @rafaeldtinoco in #3223
- flags: refactor FilterMap by @yanivagman in #3222
- go.mod: remove types replace by @NDStrahilevitz in #3236
- containers: trim mountpoint from stored paths by @NDStrahilevitz in #3231
- docs: remove old trace subcommand by @geyslan in #3238
- ebpf: pipeline: reduce iteration over policies by @geyslan in #3209
- engine: fix panic on waitgroup by @josedonizetti in #3233
- Update packaging.md for Ubuntu package building by @pimvh in #3243
- ebpf: fix socket_accept event by @NDStrahilevitz in #3240
- fix: fix container edge case in events pipeline by @geyslan in #3253
- tracee: skip golang plugin for static binaries by @josedonizetti in #3244
- Fix typo in Vagrantfile’s comment by @64J0 in #3260
- tracee: signatures-dir accept multiple values by @josedonizetti in #3246
- change hooked_syscalls event so users can specify syscalls to check. by @AsafEitani in #3136
- events: hidden_kernel_module changes by @OriGlassman in #3255
- config: extract config structs to its own pkg by @geyslan in #3228
- eBPF control plane signals by @NDStrahilevitz in #3237
- build: remove signing from snapshot by @josedonizetti in #3271
- release: bump release tag to 0.16.0 by @josedonizetti in #3272
- fix: send init events to pipeline by @geyslan in #3270
- thread-safety issues fix by @rafaeldtinoco in #3265
- fix(pkg/events): fix tailcall dependencies race issues by @rafaeldtinoco in #3274
- build: remove release on tag push by @josedonizetti in #3273
- chore: move syscaller to dist by @geyslan in #3269
- fix(tests): fix input paths in parsecmd test by @rafaeldtinoco in #3275
- tracee: add analyze cmd by @josedonizetti in #3101
- policies: rename list fields to be plural by @josedonizetti in #3242
- fix(pkg/counter): finish making counter atomic by @rafaeldtinoco in #3276
- fix: derived event not triggering if base filtered by @josedonizetti in #3280
- enrich: fixes post control plane by @NDStrahilevitz in #3285
- docs: add analyze documentation by @josedonizetti in #3292
- doc: add tutorial to verify tracee signature by @josedonizetti in #3291
- fix: signature event not triggering if base filtered by @josedonizetti in #3281
- pipeline memory efficiency using pool by @geyslan in #3297
- events: update syscall_pathname for security_file_open by @OriGlassman in #3298
- Events and Scope flags by @geyslan in #3262
- pkg/containers: fix deadlock by @josedonizetti in #3311
- [v0.16.0] chore: bump k8s tag to 0.16.1 by @josedonizetti in #3316
- docs: updating link to tracee docs for search results by @AnaisUrlichs in #3317
- feature: remove policy actions by @josedonizetti in #3314
- fix(server): re-enable prometheus counters. by @rafaeldtinoco in #3304
- fix (cgroups): already dead edge case by @NDStrahilevitz in #3325
- docs: updating policies overview by @AnaisUrlichs in #3318
- chore bump 0.16.2 by @josedonizetti in #3331
- feature(k8s): policy k8s compatible by @josedonizetti in #3330
- chore: bump k8s tag to 0.17.0 by @josedonizetti in #3336
- fix(ebpf): size of mntns/pidns filters key holders by @geyslan in #3337
- fix: validate policy names are rfc 1123 by @josedonizetti in #3335
- remove help command, create flags markdown docs by @geyslan in #3321
- fix: data source registration after NewEngine by @NDStrahilevitz in #3342
- fix(build): btfhub’s bpftool in alpine container by @geyslan in #3349
- chore(build): add LOGFROM flag to check-pr rule by @geyslan in #3348
- chore(build): change check-pr output format by @geyslan in #3351
- refactor(events): new event definitions (mutable vs immutable data) by @rafaeldtinoco in #3340
- fix(filter): remove unneeded workaround by @rafaeldtinoco in #3352
- events: adjust hidden kernel module event to v6.4 by @OriGlassman in #3360
- fix(config): loading config file by @josedonizetti in #3370
- Update the URL as the old one did not lead to the grafana tutorial an… by @AnaisUrlichs in #3371
- chore(docs): add note for quote yaml value by @geyslan in #3367
- chore: bump k8s tags to 0.17.1 by @josedonizetti in #3374
- bugfix(capture): remove CONFIG_KALLSYMS_ALL dependency by @AlonZivony in #3381
- docs: additional resources for the docs by @AnaisUrlichs in #3379
- feat: add tracee rpc service by @josedonizetti in #3389
- feat: add loggers atomic level by @josedonizetti in #3391
- Add grpc server by @josedonizetti in #3390
--helpflag parsing by @geyslan in #3393- feat: add diagnostic rpc by @josedonizetti in #3395
- Add grpc diagnostic by @josedonizetti in #3394
- fix: k8s policies tutorial by @josedonizetti in #3373
- chore(flags): change scope/event flag parsers by @geyslan in #3343
- fix: log level should match zap log priority by @josedonizetti in #3409
- fix: ignore error for cgroups that doesn’t exist by @josedonizetti in #3410
- refactor: getStackAddresses doesn’t return an err by @josedonizetti in #3414
- chore(revive): mitigate redundant warning by @rafaeldtinoco in #3417
- fix: committing typo by @testwill in #3418
- feature(types): add task identifier by @rafaeldtinoco in #3425
- fix(flags): use scope flag parser for policy by @geyslan in #3429
- fix: capture of writev by @roikol in #3413
- fix: fix section name for vfs_readv by @AlonZivony in #3421
- feat: filter file capture by ELF type by @AlonZivony in #3361
- docs: modifying readme by @AnaisUrlichs in #3378
- Fix(capture): fix verifier issue with elf capture by @AlonZivony in #3433
- fix: print_mem_dump fails on missing symbol by @NDStrahilevitz in #3384
- Revert “fix: print_mem_dump fails on missing symbol (#3384)” by @AlonZivony in #3436
- fix(definitions): ksymbols dependencies handled wrongly by @rafaeldtinoco in #3443
- feat: add streams by @josedonizetti in https://github.com/aquasecurity/tracee…
Install
Copyright 2019 Aqua Security Software Ltd.