trackerjacker: Like nmap for mapping wifi networks you’re not connected to
trackerjacker
Like nmap for mapping wifi networks you’re not connected to. Maps and tracks wifi networks and devices through raw 802.11 monitoring.
trackerjacker can help with the following:
- I want to know all the nearby wifi networks and know all the devices connected to each network.
- I want to know who’s hogging all the bandwidth.
- I want to run a command when this MAC address sends more than 100000 bytes in a 30 second window (maybe to determine when an IP camera is uploading a video, which is indicative that it just saw motion).
- I want to deauth anyone who uses more than 100000 bytes in a 10 second window.
- I want to deauth every Dropcam in the area so my Airbnb hosts don’t spy on me.
- I want to be alerted when any MAC address is seen at a power level greater than -40dBm that I’ve never seen before.
- I want to see when this particular person is nearby (based on the MAC of their mobile phone) and run a command to alert me.
- I want to write my own plugin to run some script to do something fun every time a new Apple device shows up nearby.
Install
pip3 install trackerjacker
Supported platforms: Linux (tested on Ubuntu, Kali, and RPi) and macOS (pre-alpha)
Usage
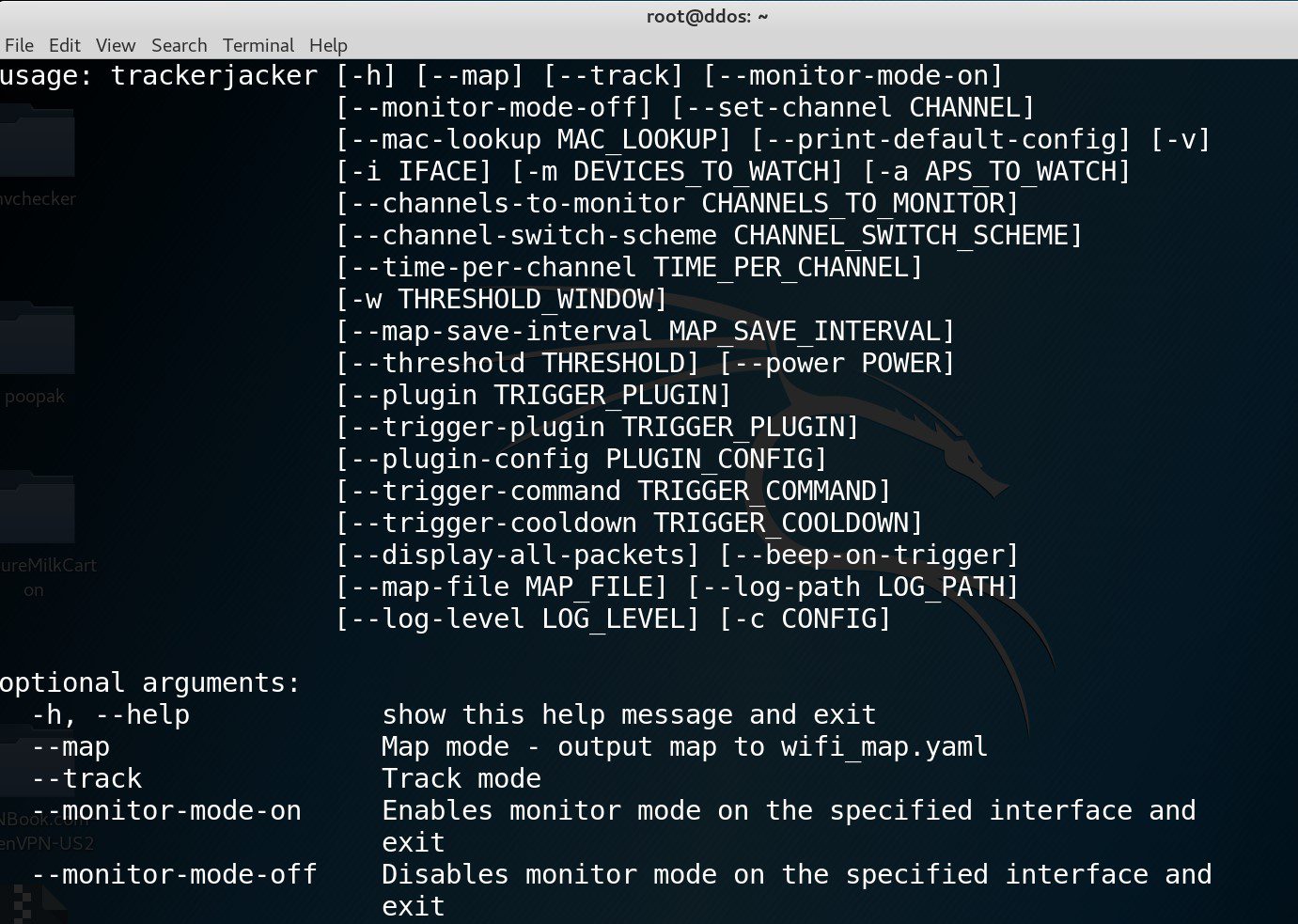
Find detailed usage like this:
trackerjacker -h
There are 2 major usage modes for trackerjacker: map mode and track mode:
Map mode example
Map command:
trackerjacker -i wlan1337 --map
By default, this outputs the wifi_map.yaml YAML file, which is a map of all the nearby WiFi networks and all of their users. Here’s an example wifi_map.yaml file:
Note that, since this is YAML, you can easily use it as an input for other scripts of your own devising. I have an example script to parse this “YAML DB” here: parse_trackerjacker_wifi_map.py.
Copyright (c) 2016 Caleb Madrigal





