trident: automated password spraying tool
trident
The Trident project is an automated password spraying tool developed to meet the following requirements:
- the ability to be deployed on several cloud platforms/execution providers
- the ability to schedule spraying campaigns in accordance with a target’s account lockout policy
- the ability to increase the IP pool that authentication attempts originate from for operational security purposes
- the ability to quickly extend functionality to include newly-encountered authentication platforms
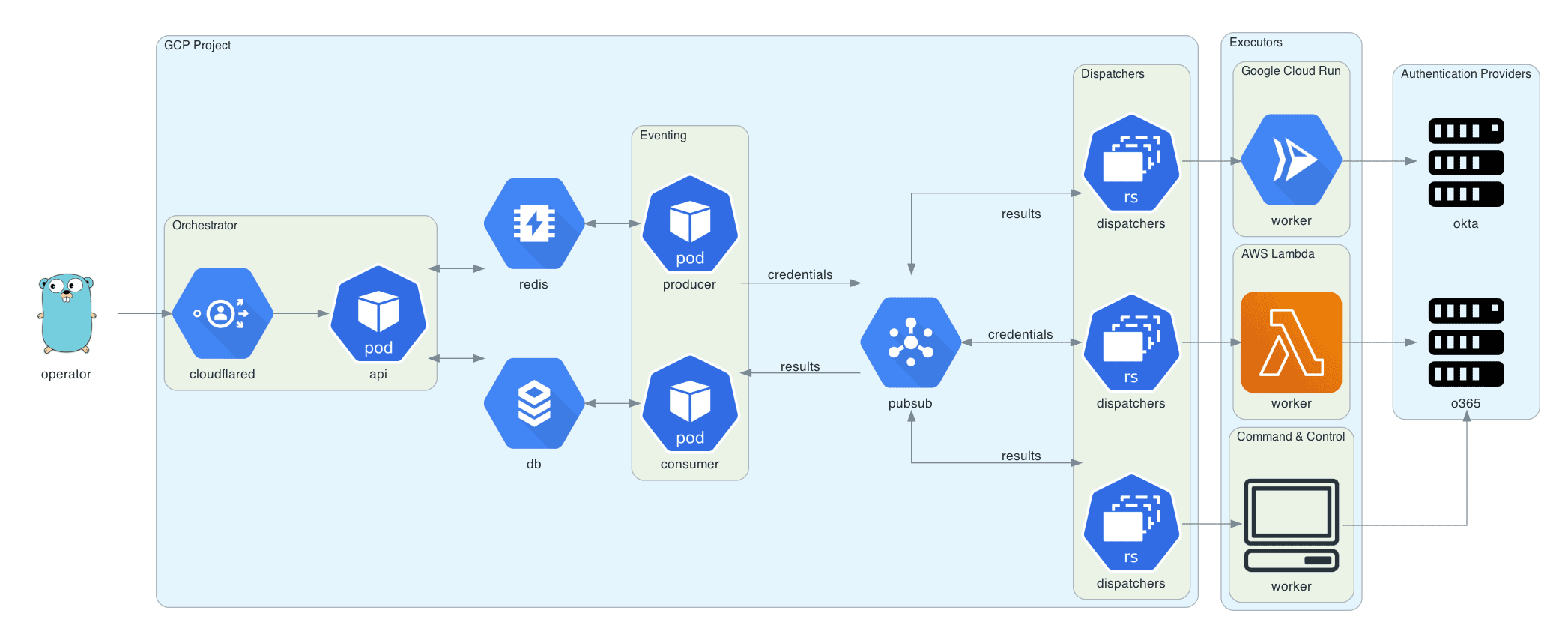
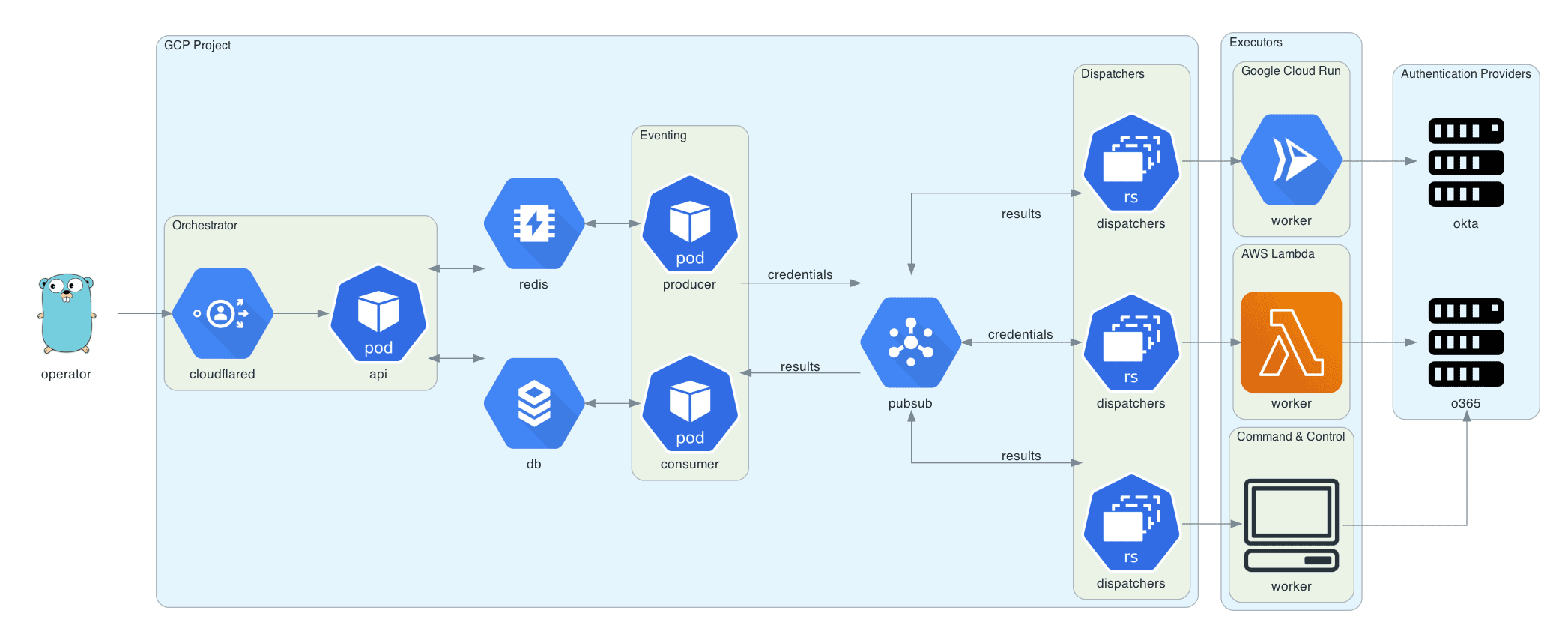
Architecture
Deployment
Deploying trident requires a Google Cloud project, a domain name (for the orchestrator API), and a Cloudflare Access configuration for this domain. Cloudflare Access is used to authenticate requests to the orchestrator API.
brew install cloudflare/cloudflare/cloudflared
brew install terraformcd terraform
cloudflared login
terraform init
terraform plan
terraform apply
Installation
Trident has a command-line interface available on the releases page. Alternatively, you can download and install trident-client via go get:
GO111MODULE=on go get github.com/praetorian-inc/trident/cmd/trident-client
Usage
Config
The trident-client binary sends API requests to the orchestrator. It reads from ~/.trident/config.yaml, which has the following format:
Campaigns
With a valid config.yaml, the trident-client can be used to create password spraying campaigns, as shown below:
trident-client campaign -u usernames.txt -p passwords.txt –interval 5s –window 120s
The –interval option allows the operator to insert delays between credential attempts. The –window option allows the operator to set a hard stop time for the campaign. Additional arguments are documented below:
Results
The results subcommand can be used to query the result table. This subcommand has several options but defaults to showing all valid credentials across all campaigns.
Additional arguments are documented below:
Copyright (C) 2021 praetorian-inc





