UhOh365
UhOh365 is a script that can see if an email address is valid in Office365. This does not perform any login attempts, is unthrottled, and is incredibly useful for social engineering assessments to find which emails exist and which don’t.
Microsoft does not consider “email enumeration” a vulnerability, so this is taking advantage of a “feature”. There are a couple of other public Office365 email validation scripts out there, but they all (that I have seen) require at least 1 login attempt per user account. That is detectable and can be found as a light bruteforce attempt (1 “common” password across multiple accounts).
This script allows for email validation with zero login attempts and only uses Microsoft’s built-in Autodiscover API so it is invisible to the person/company who owns the email address. Furthermore, this API call appears to be completely unthrottled and I was able to validate over 2,000 email addresses within 1 minute in my testing.
Explanation
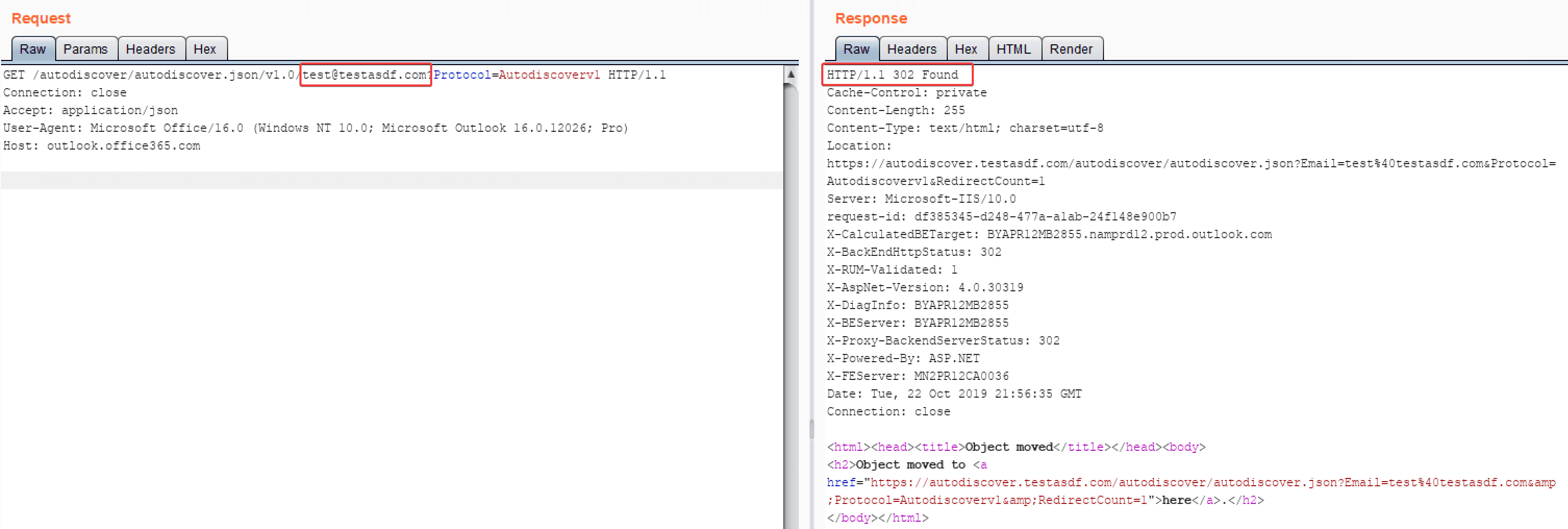
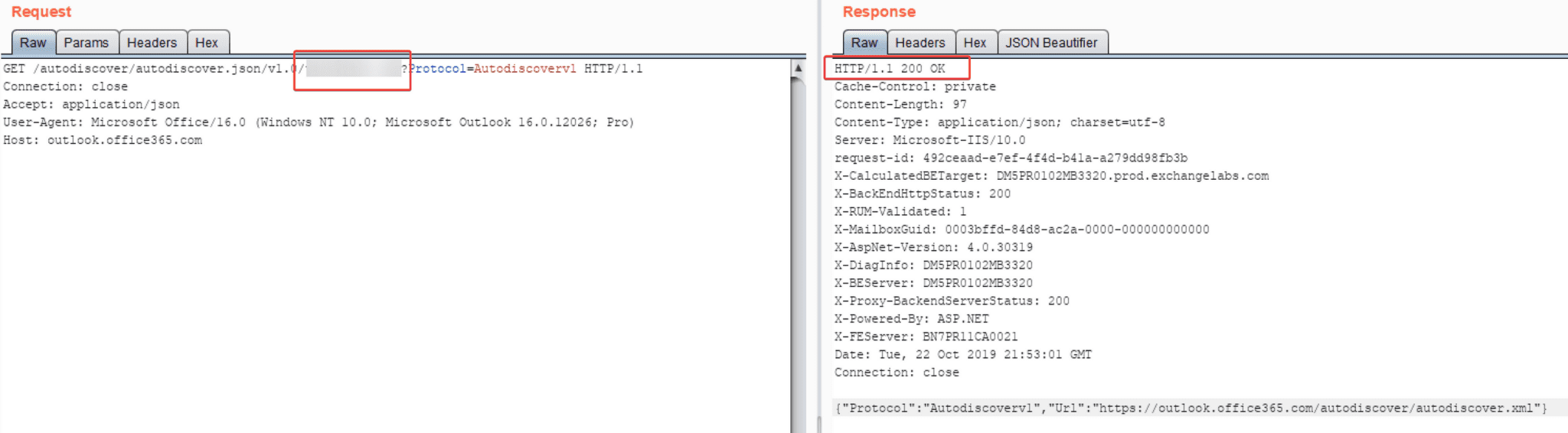
This is actually a very easy thing to do. It turns out the /autodiscover/autodiscover.json/v1.0/{EMAIL}?Protocol=Autodiscoverv1 API endpoint returns different status codes for if an email exists in o365 or not. 200 status code means it exists, a 302 means it doesn’t exist.
Notice this request takes zero authentication or identifying parameters and it does not cause a login attempt on the target account.
Download
git clone https://github.com/Raikia/UhOh365.git
Use
Copyright (C) 2020 Chris King
Source: https://github.com/Raikia/