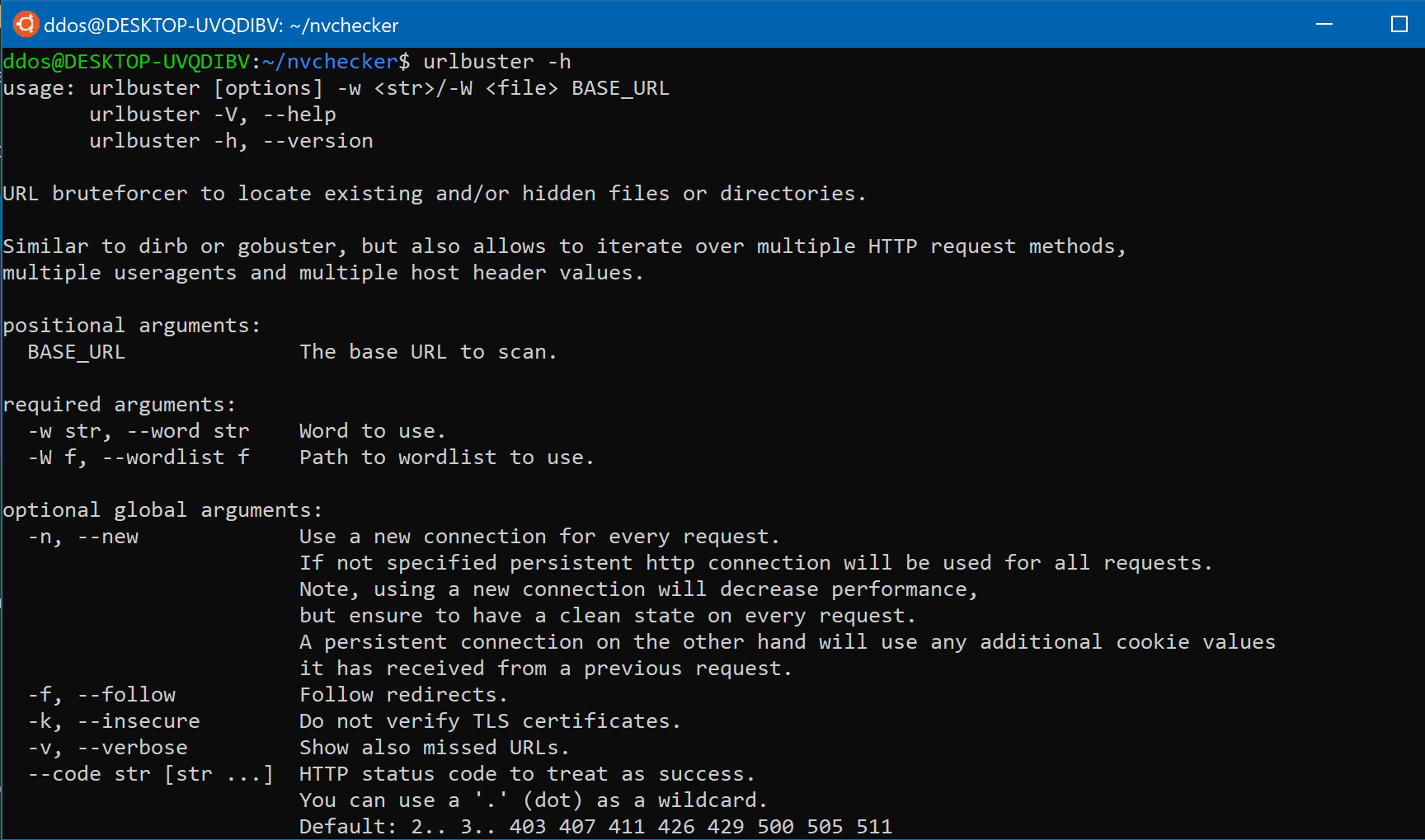
urlbuster
Powerful web directory fuzzer to locate existing and/or hidden files or directories.
Similar to dirb or gobuster, but with a lot of mutation options.
⭐ Features
- Proxy support
- Cookie support
- Basic Auth
- Digest Auth
- Retries (for slow servers)
- Persistent and non-persistent HTTP connection
- Request methods: GET, POST, PUT, DELETE, PATCH, HEAD, OPTIONS
- Custom HTTP header
- Mutate POST, PUT and PATCH payloads
- Mutate with different request methods
- Mutate with different HTTP headers
- Mutate with different file extensions
- Mutate with and without trailing slashes
- Enumerate GET parameter values
Install
pip install urlbuster
Use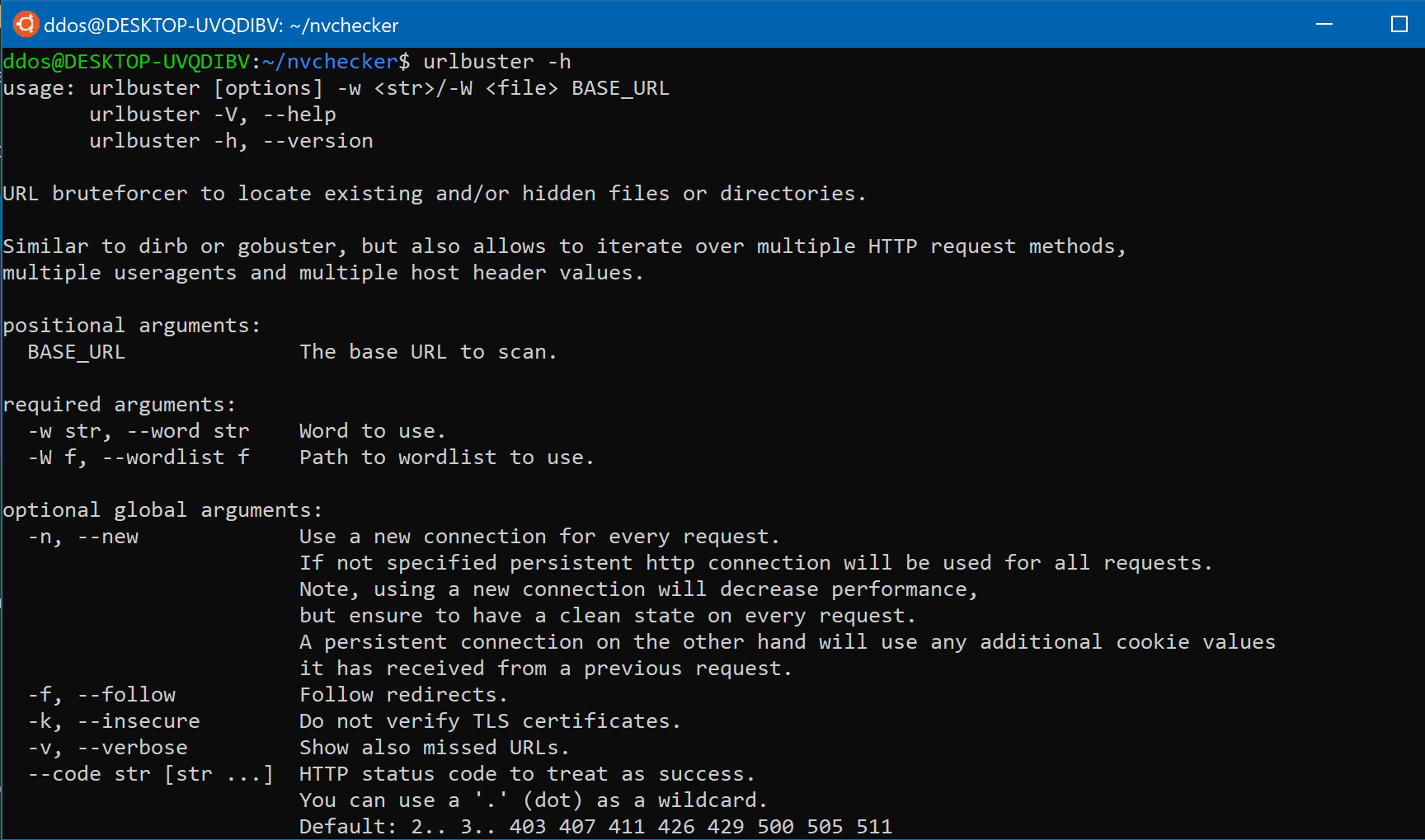
Examples
Default usage
Basic
$ urlbuster \
-W /path/to/wordlist.txt \
http://www.domain.tld/
Proxy through Burpsuite
$ urlbuster \
-W /path/to/wordlist.txt \
--proxy 'http://localhost:8080' \
http://www.domain.tld/
Save results to file
$ urlbuster \
-W /path/to/wordlist.txt \
--output out.txt \
http://www.domain.tld/
Scan behind Basic Auth
$ urlbuster \
-W /path/to/wordlist.txt \
--auth-basic 'user:pass' \
http://www.domain.tld/
Use session cookie
$ urlbuster \
-W /path/to/wordlist.txt \
--cookie 'PHPSESSID=a79b00e7-035a-2bb4-352a-439d855feabf' \
http://www.domain.tld/
Find files
Find files in root directory
$ urlbuster \
-W /path/to/wordlist.txt \
--code 200 301 302 \
--ext .zip .tar .tar.gz .gz .rar \
http://www.domain.tld/
Find files in sub directory
$ urlbuster \
-W /path/to/wordlist.txt \
--code 200 301 302 \
--ext .zip .tar .tar.gz .gz .rar \
http://www.domain.tld/wp-content/
Advanced usage
Bruteforce query parameter
$ urlbuster \
-W /path/to/wordlist.txt \
--method GET \
--code 200 301 302 \
http://www.domain.tld/search?q=
Bruteforce POST requests
$ urlbuster \
-W /path/to/wordlist.txt \
--code 200 301 302 \
--method POST \
--payload \
'user=somename' \
'pass=somepass' \
'mail=some@mail.tld' \
'submit=yes' \
http://www.domain.tld/
Bruteforce mutated POST requests
$ urlbuster \
-w index.php \
--code 200 301 302 \
--method POST \
--mpayload \
'user=somename1' \
'user=somename2' \
'user=somename3' \
'pass=somepass1' \
'pass=somepass2' \
'pass=somepass3' \
'mail=some@mail1.tld' \
'mail=some@mail2.tld' \
'mail=some@mail3.tld' \
'submit=yes' \
http://www.domain.tld/wp-admin/
User-agent SQL injections
$ urlbuster \
-W /path/to/wordlist.txt \
--code 5.. \
--method GET POST \
--mheader \
"User-Agent: ;" \
"User-Agent: ' or \"" \
"User-Agent: -- or #" \
"User-Agent: ' OR '1" \
"User-Agent: ' OR 1 -- -" \
"User-Agent: \" OR 1 = 1 -- -" \
"User-Agent: '='" \
"User-Agent: 'LIKE'" \
"User-Agent: '=0--+" \
"User-Agent: OR 1=1" \
"User-Agent: ' OR 'x'='x" \
"User-Agent: ' AND id IS NULL; --" \
http://www.domain.tld/
Find potential hosts
$ urlbuster \
-w / \
--method GET POST \
--mheader \
"Host: internal1.lan" \
"Host: internal2.lan" \
"Host: internal3.lan" \
"Host: internal4.lan" \
"Host: internal5.lan" \
"Host: internal6.lan" \
http://10.0.0.1
Copyright (c) 2020 cytopia <https://github.com/cytopia>
Source: https://github.com/cytopia/