vucsa v1.1 releases: Vulnerable Client-Server Application

Vulnerable Client-Server Application (VuCSA)
A vulnerable client-server application (VuCSA) is made for learning/presenting how to perform penetration tests of non-http thick clients. It is written in Java (with JavaFX graphical user interface).
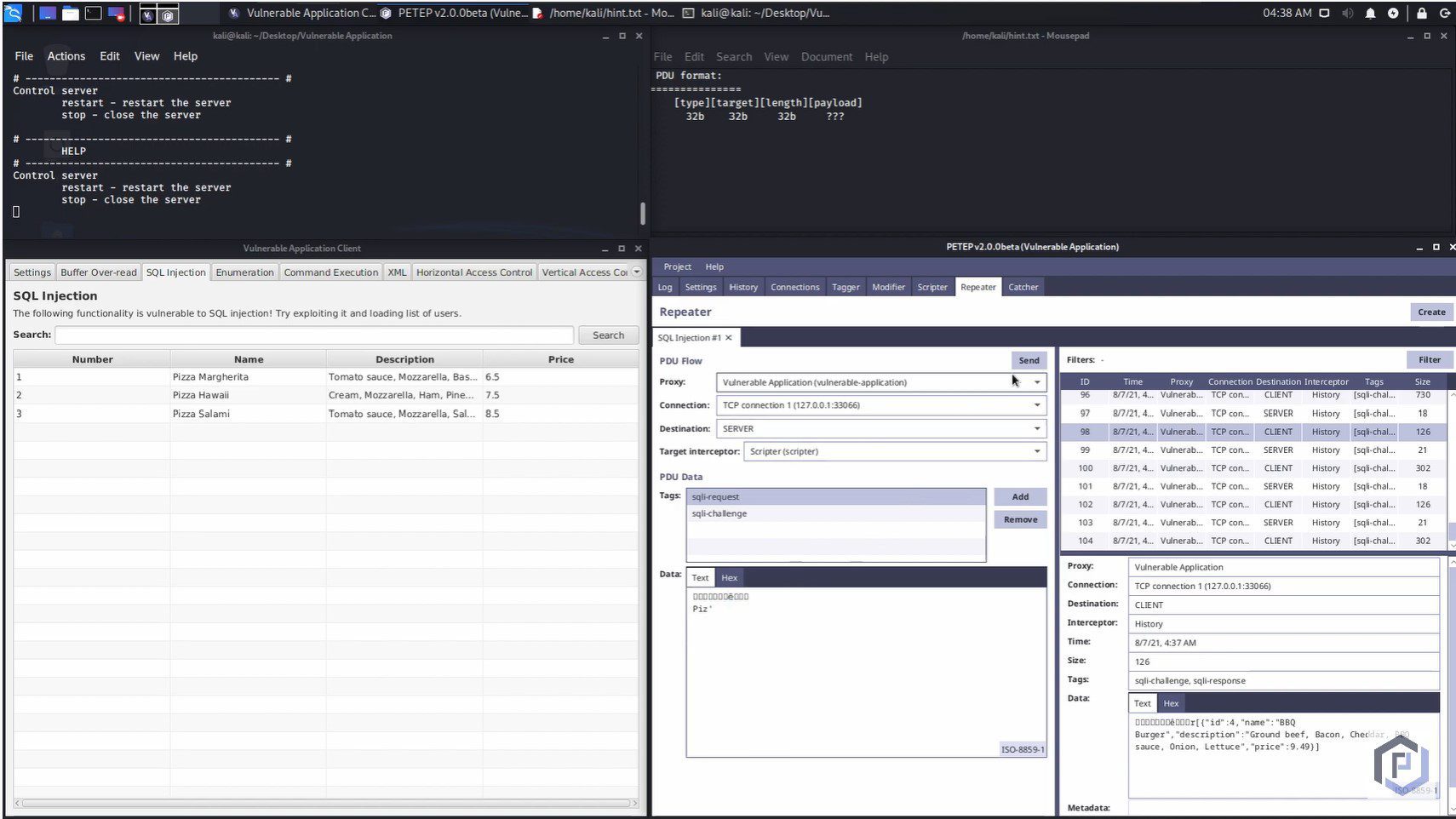
Currently, the vulnerable application contains the following challenges:
- Buffer Over-read (simulated)
- Command Execution
- SQL Injection
- Enumeration
- XML
- Horizontal Access Control
- Vertical Access Control
If you want to know how to solve these challenges, take a look at the PETEP website, which describes how to use the open-source tool PETEP to exploit them.
Tip: Before you start hacking, do not forget to check the data structure of the messages below.
How to Run
In order to run the vulnerable server and client, you can use one of the releases on GitHub or run gradle assemble, which creates distribution packages (for both Windows and Unix). These packages contain sh/bat scripts that will run the server and client using JVM.
Project Structure
The project is divided into three modules:
- vucsa-common – common functionality for both client and server (including protocol processing utilities)
- vucsa-client – vulnerable client with JavaFX GUI
- vucsa-server – vulnerable server for terminal use
Data Structure
Messages transmitted between server and client have the following simple format:
[type][target][length][payload] 32b 32b 32b ???
These four parts have the following meaning:
- type – type of the message (used for serialization/deserialization)
- target – target handler that will receive the message
- length – length of the payload
- payload – data serialized into bytes
Changelog v1.1
Added RCE (Remote Code Execution) challenge with vulnerable Java deserialization, updated fonts.
Note: For Mac with ARM64 architecture, use the special version and use at least Java 17.
Download
Copyright (C) 2022 Warxim






