Wapiti 3.1.8 releases, web-application vulnerability scanner
Wapiti works as a “black-box” vulnerability scanner, that means it won’t study the source code of web applications but will work like a fuzzer, scanning the pages of the deployed web application, extracting links and forms and attacking the scripts, sending payloads and looking for error messages, special strings or abnormal behaviors.
General features
- Generates vulnerability reports in various formats (HTML, XML, JSON, TXT…).
- Can suspend and resume a scan or an attack (session mechanism using sqlite3 databases).
- Can give you colors in the terminal to highlight vulnerabilities.
- Different levels of verbosity.
- Fast and easy way to activate/deactivate attack modules.
- Adding a payload can be as easy as adding a line to a text file.
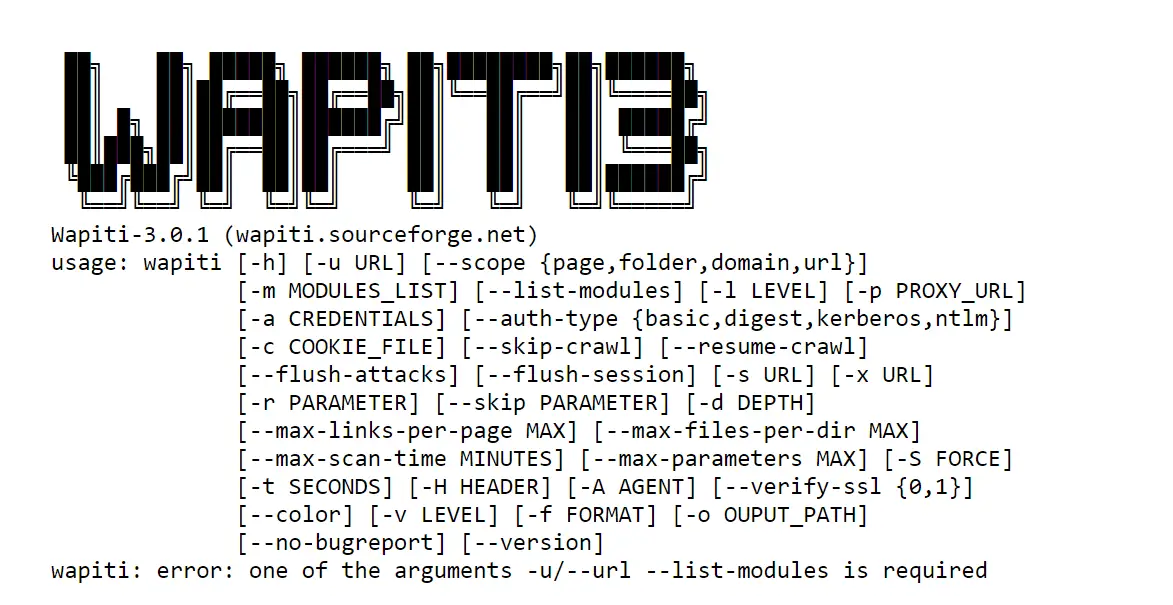
Browsing features
- Support HTTP, HTTPS, and SOCKS5 proxies.
- Authentication on the target via several methods: Basic, Digest, Kerberos or NTLM.
- Ability to restrain the scope of the scan (domain, folder, page, url).
- Automatic removal of one or more parameters in URLs.
- Multiple safeguards against scan endless-loops (for example, limit of values for a parameter).
- Possibility to set the first URLs to explore (even if not in scope).
- Can exclude some URLs of the scan and attacks (eg: logout URL).
- Import of cookies (get them with the wapiti-getcookie tool).
- Can activate / deactivate SSL certificates verification.
- Extract URLs from Flash SWF files.
- Try to extract URLs from javascript (very basic JS interpreter).
- HTML5 aware (understand recent HTML tags).
- Several options to control the crawler behavior and limits.
- Skipping some parameter names during attack.
- Setting a maximum time for the scan process.
- Adding some custom HTTP headers or setting a custom User-Agent.
Supported attacks
- Database Injection (PHP/ASP/JSP SQL Injections and XPath Injections)
- Cross Site Scripting (XSS) reflected and permanent
- File disclosure detection (local and remote include, require, fopen, readfile…)
- Command Execution detection (eval(), system(), passtru()…)
- XXE (Xml eXternal Entity) injection
- CRLF Injection
- Search for potentially dangerous files on the server (thank to the Nikto db)
- Bypass of weak htaccess configurations
- Search for copies (backup) of scripts on the server
- Shellshock
- DirBuster like
Wapiti supports both GET and POST HTTP methods for attacks.
It also supports multipart and can inject payloads in filenames (upload).
Display a warning when an anomaly is found (for example 500 errors and timeouts) Makes the difference between permanent and reflected XSS vulnerabilities.
Module names
The aforementioned attacks are tied to the following module names :
- backup (Search for copies and scripts)
- blindsql (SQL injection vulnerabilities detected with time-based methodology)
- buster (DirBuster like a module)
- crlf (CR-LF injection in HTTP headers)
- delay (Not an attack module, prints the 10 slowest to load web pages of the target)
- exec (Code execution or command injection)
- file (Path traversal, file inclusion, and XXE)
- htaccess (Misconfigured htaccess restrictions)
- nikto (Look for known vulnerabilities by testing URL existence and checking responses)
- permanent XSS (Rescan the whole target after the xss module execution looking for previously tainted payloads)
- shellshock (Test Shellshock attack, see https://en.wikipedia.org/wiki/Shellshock_%28software_bug%29 )
- sql (Error-based SQL injection detection)
- xss (XSS injection module)
Changelog v3.1.8
- mod_spring4shell: New Module to detect the Spring4Shell vulnerability
mod_upload: New module to detect unrestricted file uploads (attempt to upload PHP code)
mod_https_redirect: New module to detect lack of redirect-to-https behavior
mod_crlf: Fix double-encoding errors
mod_methods: In-depth check of methods allowed by a web server
mod_permanentxss: Fix several bugs
mod_xss: Detect if HTML injection is allowed when XSS injection failed
mod_wapp: several improvements like CPE versions added to output
mod_log4shell: Add Ubiquiti UniFi to targets
mod_buster: Discovered assets are added to the generated report
Core: make module errors more verbose
Core: add a Dockerfile to quickly set up your own PHP endpoint
CLI: renamed some authentication options
Copyright 2006-2018 © Nicolas Surribas (@devl00p)






