arachni v1.6.1.3 releases: Web application security scanner framework

I would like to talk about arachni, an open-source framework among many Web Vulnerability Scanners (WVS). I tested it briefly, and it seems to be usable. Also, you should learn how to secure coding plan.
Arachni is a feature-full, modular, high-performance Ruby framework aimed at helping penetration testers and administrators evaluate the security of modern web applications. It is free, with its source code public, and available for review.
It is multi-platform, supporting all major operating systems (MS Windows, Mac OS X, and Linux) and distributed via portable packages which allow for instant deployment.
It is versatile enough to cover a lot of use cases, ranging from a simple command-line scanner utility to a global high-performance grid of scanners, to a Ruby library allowing for scripted audits, to a multi-user multi-scan web collaboration platform. In addition, its simple REST API makes integration a cinch.
Finally, due to its integrated browser environment, it can support highly complicated web applications which make heavy use of technologies such as JavaScript, HTML5, DOM manipulation, and AJAX.
Arachni includes command-line and Web GUI versions.
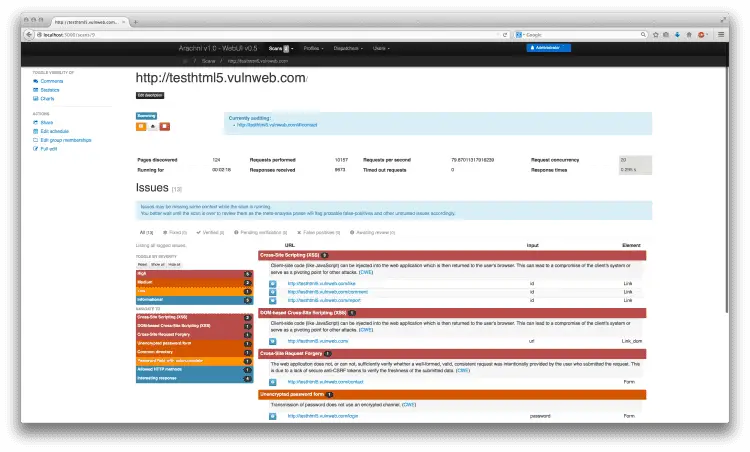
WEB USER INTERFACE
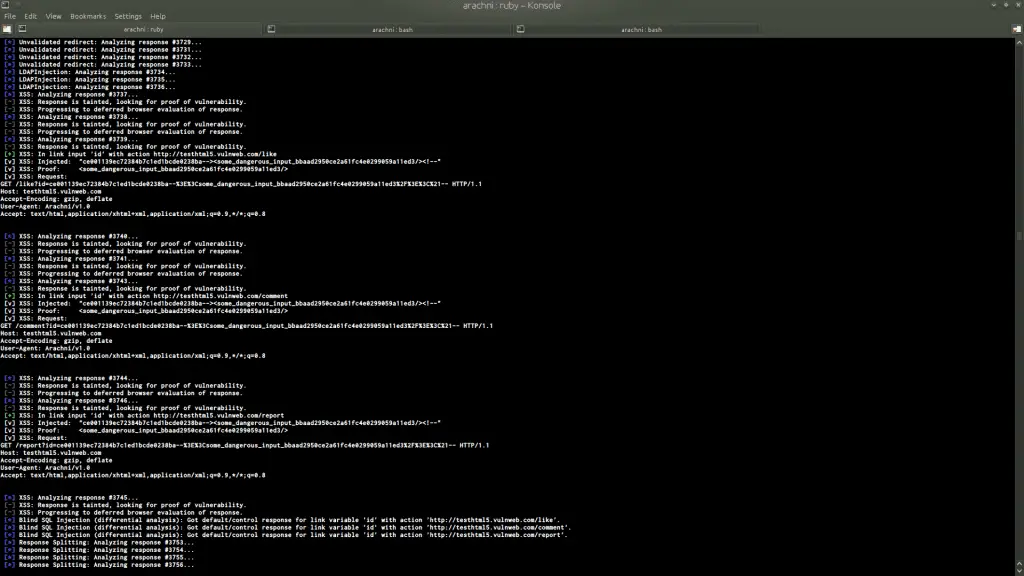
COMMAND-LINE INTERFACE
Vulnerability detection
Vulnerability detection scores represent the ability of a scanner to detect different types and permutations of vulnerabilities, as well as the accuracy of those results when dealing with pitfalls that commonly cause false positives.
Vulnerability detection and accuracy scores can be found at: http://sectoolmarket.com/price-and-feature-comparison-of-web-application-scanners-unified-list.html
Arachni scores:
- SQL injection: 100% (0% false positives)
- Reflected XSS: 90.91% (0% false positives) — Misses cases which require support for the now obsolete VBScript language.
- Local file inclusion: 100% (0% false positives)
- Remote file inclusion: 100% (0% false positives)
- Unvalidated redirect: 100% (0% false positives)
- Backup files: 100% (0% false positives)
Changelog v1.6.1.3
- Updated Rack version.
Download
Copyright 2010-2022 Ecsypno.






