wsh: Web shell generator and command line interface
wsh
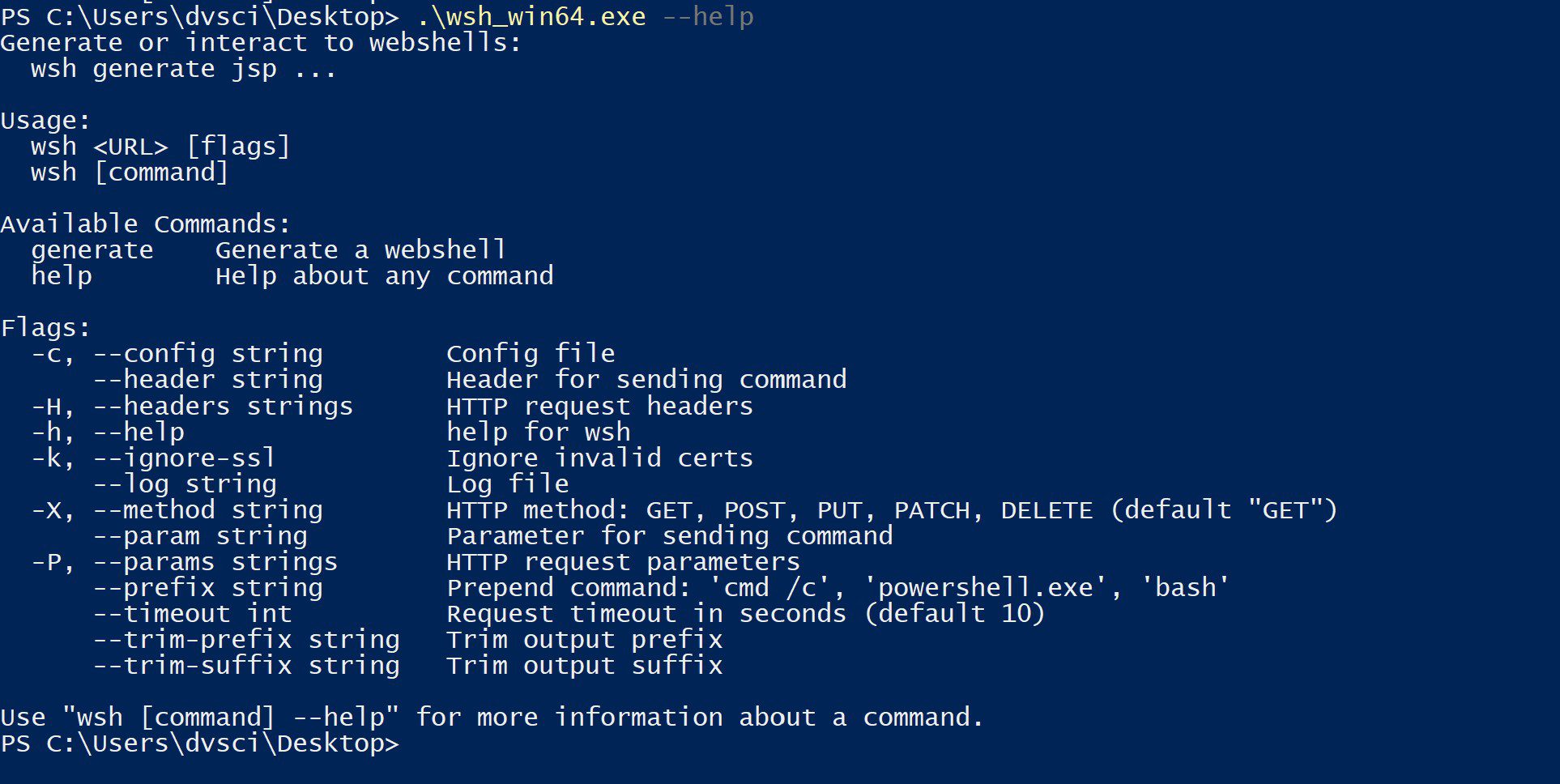
wsh (pronounced woosh) is a web shell generator and command-line interface. This started off as just an http client since interacting with webshells is a pain. There’s a form, to send a command you have to type in an input box and press a button. I wanted something that fits into my workflow better and ran in the terminal. Thus wsh was born.
The client features command history, logging, and can be configured to interact with a previously deployed standard webshell with a form/button. The generator creates webshells in php, asp, and jsp. They are generated with random variables, so each will have a unique hash. They can be configured with a whitelist, passwords, and allow commands to be sent over custom headers and parameters. The generator and client can be configured through command-line flags or configuration files to allow for saving a setup that works for you without doing what I call the “–help” dance. Once configured, the client and generator use the same config file.
Features
- Interact with deployed web shells via the command line
- Logging
- Generate webshells in PHP, JSP, and ASP
- IP whitelisting
- Password protection
- Send commands over custom headers/parameters
- File upload / download
- Base64 encoded shells for asp and php
- XOR encrypted shells for asp and php
Usage
Connect
Generate
Client usage / File IO
I wanted the client to be language-agnostic, so all webshells needed to implement the same upload/download logic. Unfortunately, it is a pain to do multipart form uploads natively in jsp and classic asp, so files are uploaded as base64 in a parameter. This is not ideal as the max file upload size is limited to the maximum parameter size. In the future, I may try and implement multipart form uploads, or do multiple requests to transfer larger files.
Templates
Using the go template library adds alot of flexibility to the generator. Occasionally a webshell will get caught by AV however, I have found that adding in a bunch of random code in the template file will often make the shell look benign enough to allow it to persist on the disk. I have included an example in the templates/covert-php.tml file.
Additionally, you can modify these templates to include your name/contact information for attribution in the use case of a penetration test.
Client Functionality
Prefix
A prefix can be specified to prepend a string to each command sent to the shell. This can be used to turn a normal cmd shell into a powershell shell.
Logging
Logs are timestamped and include the host being interacted with. Log files are appended, so feel free to use the same log file for multiple sessions/hosts.
Trim prefix/suffix
The client can be configured to trim extraneous html content from a request, this is useful when interacting with standard html interface webshells, or maybe if a generated shell is sneakily embedded in a wordpress installation.
Download & Tutorial
Copyright (C) 2020 EatonChips