wstunnel v8.0 releases: Tunneling over websocket protocol
wstunnel
Most of the time when you are using a public network, you are behind some kind of firewall or proxy. One of their purposes is to constrain you to only use certain kinds of protocols. Nowadays, the most widespread protocol is http and is de facto allowed by third-party equipment.
This tool understands this fact and uses the websocket protocol which is compatible with http in order to bypass firewalls and proxies. Wstunnel allows you to tunnel whatever traffic you want.
My inspiration came from this project but as I don’t want to install npm and nodejs to use this tool, I remade it in Haskell and improved it.
What to expect:
- Good error messages and debug information
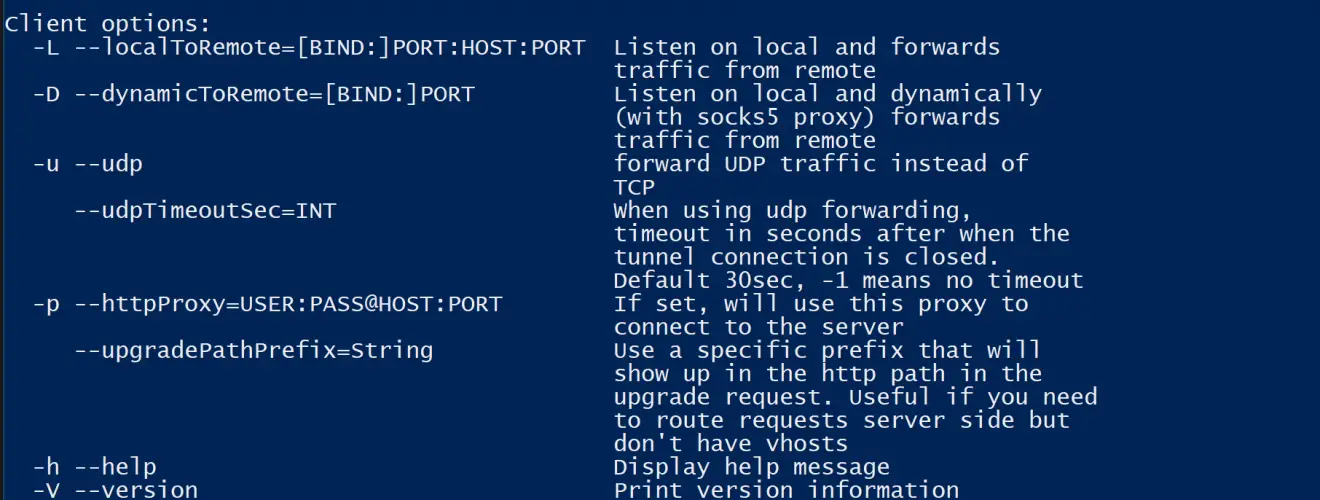
- Static tunneling (TCP and UDP)
- Dynamic tunneling (socks5 proxy)
- Support for http proxy (when behind one)
- Support for tls/https server (with an embedded self-signed certificate, see comment in the example section)
- Standalone binary for Linux x86_64 (so just cp it where you want)
- Standalone archive for windows
Changelog v8.0
Use
Examples
Simplest one
On your remote host, start the wstunnel’s server by typing this command in your terminal
wstunnel --server ws://0.0.0.0:8080
This will create a websocket server listening on any interface on port 8080. On the client-side use this command to forward traffic through the websocket tunnel
wstunnel -D 8888 ws://myRemoteHost:8080
This command will create a sock5 server listening on port 8888 of a loopback interface and will forward traffic.
Ex: With firefox, you can set up a proxy using this tunnel, by setting in networking preferences 127.0.0.1:8888 and selecting socks5 proxy
As proxy command for SSH
You can specify stdio as source port on the client-side if you wish to use wstunnel as part of a proxy command for ssh
ssh -o ProxyCommand="wstunnel -L stdio:%h:%p ws://localhost:8080" my-server
When behind a corporate proxy
Another useful example is when you want to bypass an http proxy (a corporate proxy for example) The most reliable way to do it is to use wstunnel as described below
Start your wstunnel server with tls activated
wstunnel --server wss://0.0.0.0:443 -r 127.0.0.1:22
The server will listen on any interface using port 443 (https) and restrict traffic to be forwarded only to the ssh daemon.
Be aware that the server will use a self-signed certificate with weak cryptographic algorithm. It was made in order to add the least possible overhead while still being compliant with tls.
Do not rely on wstunnel to protect your privacy, as it only forwards traffic that is already secure by design (ex: https)
Now on the client side start the client with
wstunnel -L 9999:127.0.0.1:22 -p mycorporateproxy:8080 wss://myRemoteHost:443
It will start a tcp server on port 9999 that will contact the corporate proxy, negotiate a tls connection with the remote host and forward traffic to the ssh daemon on the remote host.
You may now access your server from your local machine on ssh by using
ssh -p 9999 login@127.0.0.1
Download
Copyright erebe (c) 2016







