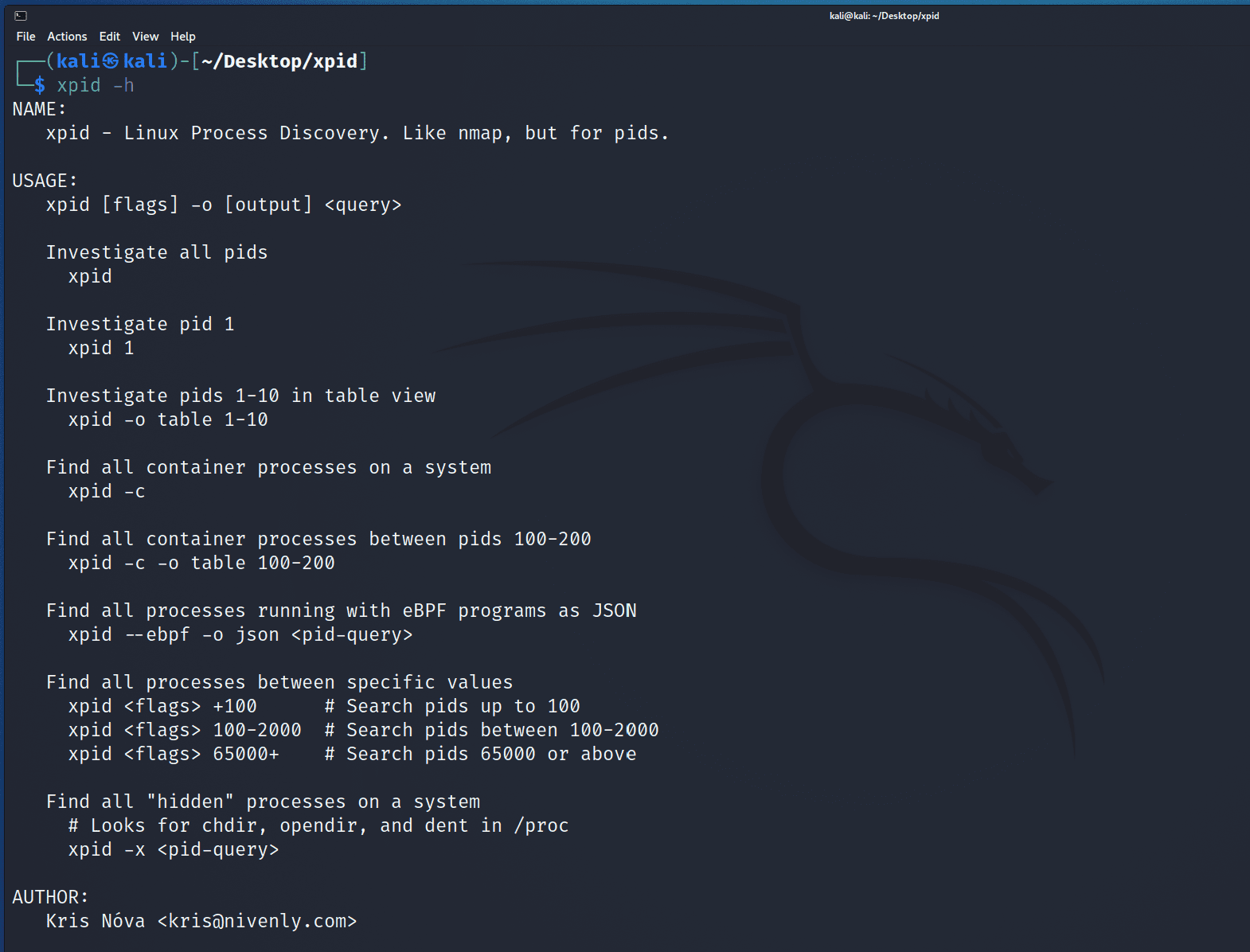
xpid
It’s nmap but for pids.
xpid gives a user the ability to “investigate” for process details on a Linux system.
For example, a sleeping thread will have a directory /proc/[pid] that can be navigated to, but not listed.
xpid will check many different places in the kernel for details about a pid. By searching subsets of possible pids xpid will be able to check for pid details in many places in the kernel.
Changelog v1.3.2
- Adding better support for -o json
- The API now has json tags 🙂
Install
Install libxpid first (below), and then compile the Go runtime.
Xpid C library (libxpid)
libxpid is written in C, as it will leverage ptrace(2) and eBPF code directly. This means that the xpid executable is NOT entirely statically linked. You must first have libxpid installed on your system before the xpid Go program will run.
git clone https://github.com/kris-nova/xpid.git
cd xpid/libxpid
./configure
cd build
make
sudo make install
git clone https://github.com/kris-nova/xpid.git
cd xpid
make
sudo make install
Use
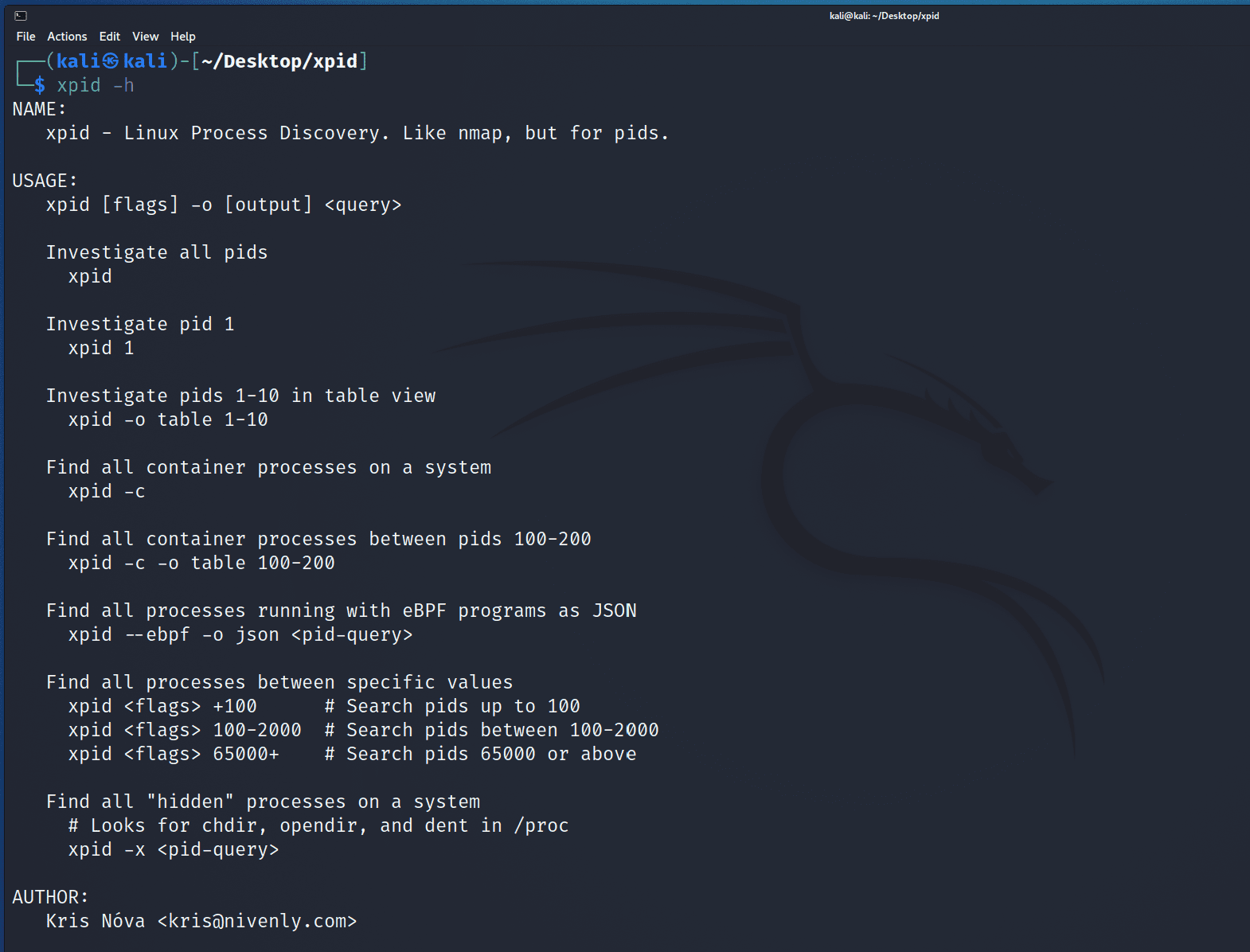
Container pids (xpid -c) 📦
xpid will look up container processes at runtime. 🎉
This works by reading the link in /proc/[pid]/ns/@cgroup and correlating it back to the value in /proc/1/[pid]/ns/@cgroup.
Regardless of the pid namespace context, if there is a “container” that is unique from the current pid 1, xpid will find it.
eBPF pids (xpid -b) 🐝
xpid will find pids that have eBPF programs loaded at runtime.
This works by correlating the file descriptor info from /proc/[pid]/fdinfo/* back to /sys/fs/bpf/progs.debug. If a pid has an eBPF program loaded, xpid will find it.
Hidden pids (xpid -x) 🙈
Because of the flexibility with kernel modules and eBPF in the kernel, it can be possible to prevent the proc(5) filesystem from listing pid details in traditional ways.
xpid uses a variety of tactics to search for pids in the same way nmap will use different tactics to port scan a target.
Copyright (c) 2022 Kris Nóva <kris@nivenly.com>
Source: https://github.com/kris-nova/