xsser v1.8.3 releases: automatic -framework- to detect, exploit and report XSS vulnerabilities

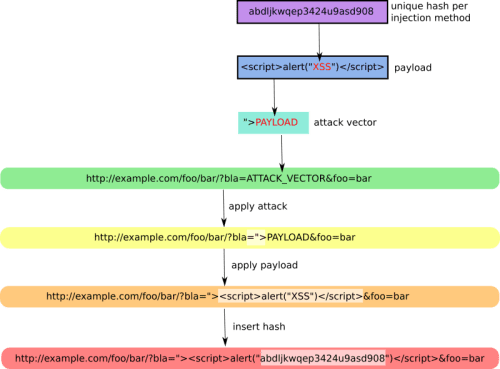
Cross-Site “Scripter” (aka XSSer) is an automatic -framework- to detect, exploit and report XSS vulnerabilities.
It provides several options to try to bypass certain filters and various special techniques for code injection.
XSSer has pre-installed [ > 1300 XSS ] attacking vectors and can bypass-exploit code on several browsers/WAFs:
[PHPIDS]: PHP-IDS
[Imperva]: Imperva Incapsula WAF
[WebKnight]: WebKnight WAF
[F5]: F5 Big IP WAF
[Barracuda]: Barracuda WAF
[ModSec]: Mod-Security
[QuickDF]: QuickDefense
[Sucuri]: SucuriWAF
[Chrome]: Google Chrome
[IE]: Internet Explorer
[FF]: Mozilla’s Gecko rendering engine, used by Firefox/Iceweasel
[NS-IE]: Netscape in IE rendering engine mode
[NS-G]: Netscape in the Gecko rendering engine mode
[Opera]: Opera Browser
Changelog v1.8.3
- Modified/Updated: anti false positives checkers
- Added: internal ‘headless’ browser: gecko/firefox engine
- Modified/Updated: –reverse-check (GET/POST) (local/remote)
- Removed: –reverse-open
- Modified/Updated: DOM attack (added vectors: 13)
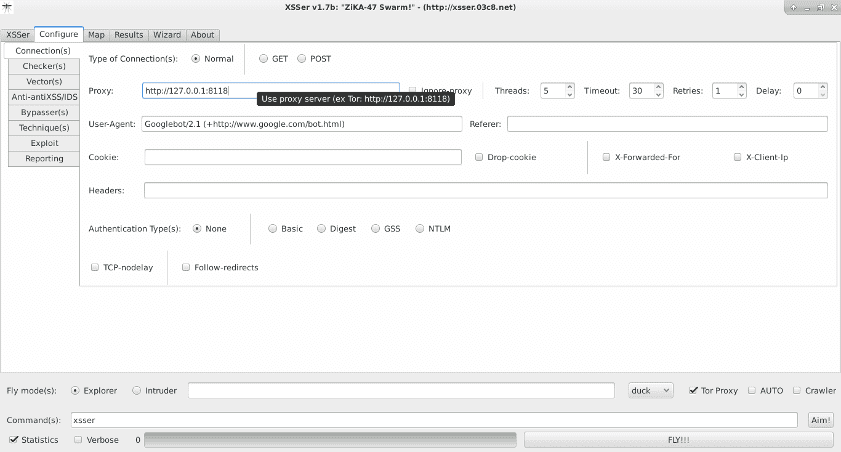
- Modified/Updated: GTK+
- Added: Requirements
- Updated: Documentation
- Updated: Website
Installing:
XSSer runs on many platforms. It requires Python and the following libraries:
Requirement:
Ubuntu:
sudo apt-get install python3-pycurl python3-bs4 python3-geoip python3-geoip2 python3-gi python3-cairocffiKali, Ubuntu, ArchLinux, ParrotSec, Fedora
sudo pip3 install pycurl bs4 geoip2 gobject cairocffiDownload
git clone https://github.com/epsylon/xsser.git
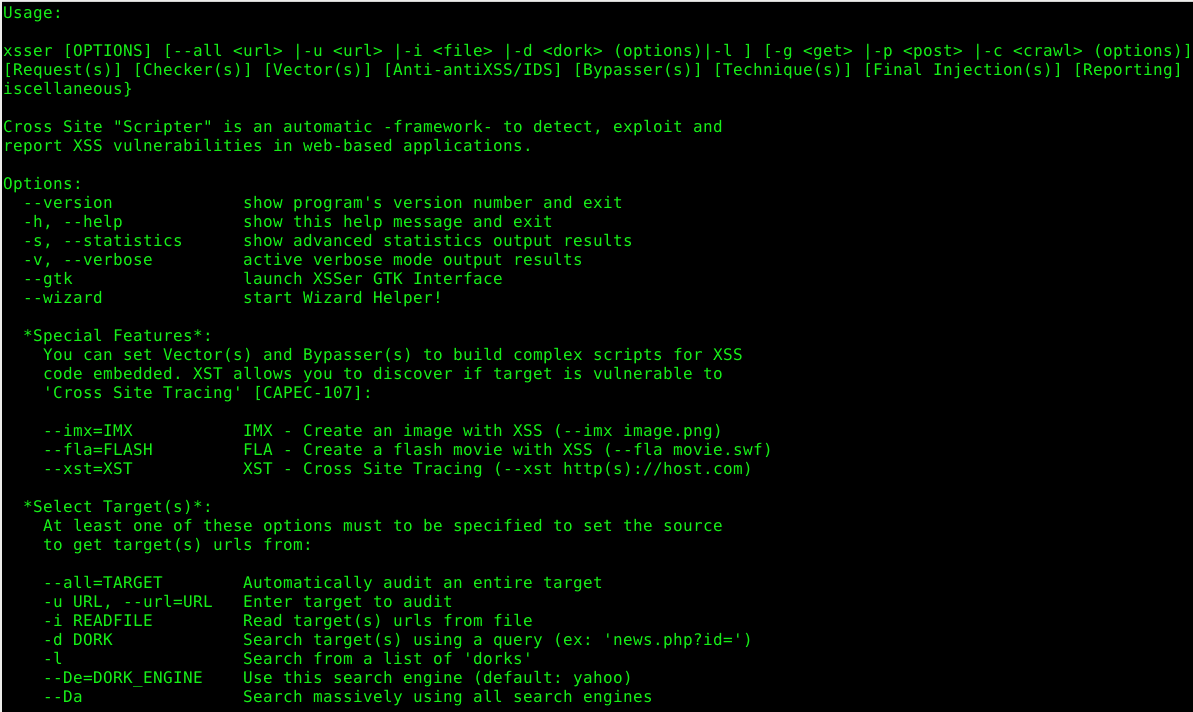
Usage
Copyright (C) 2019 psy (epsylon)
Source: https://github.com/epsylon/