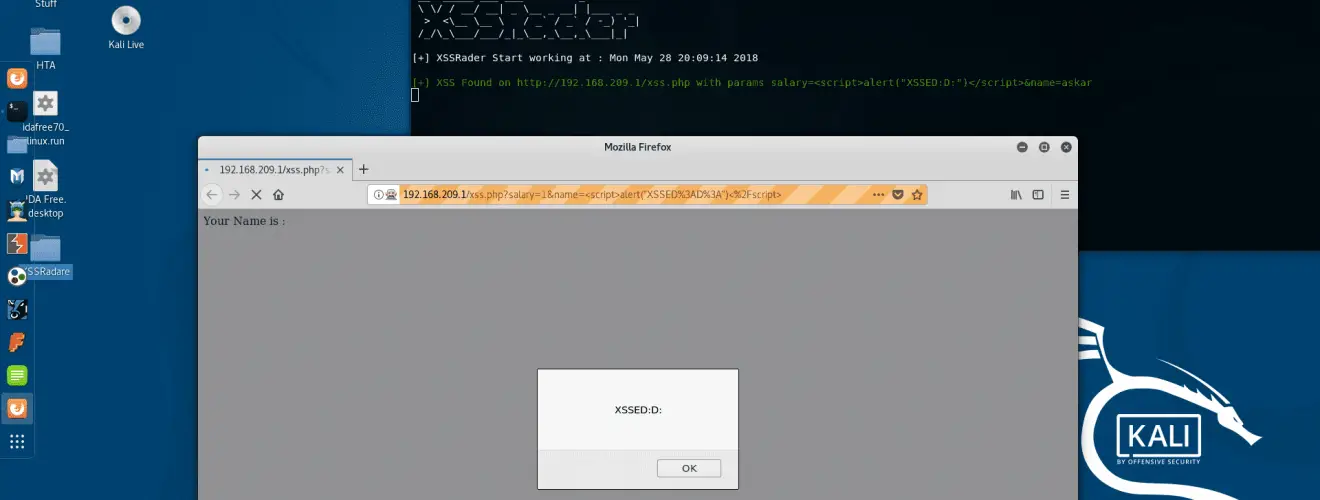
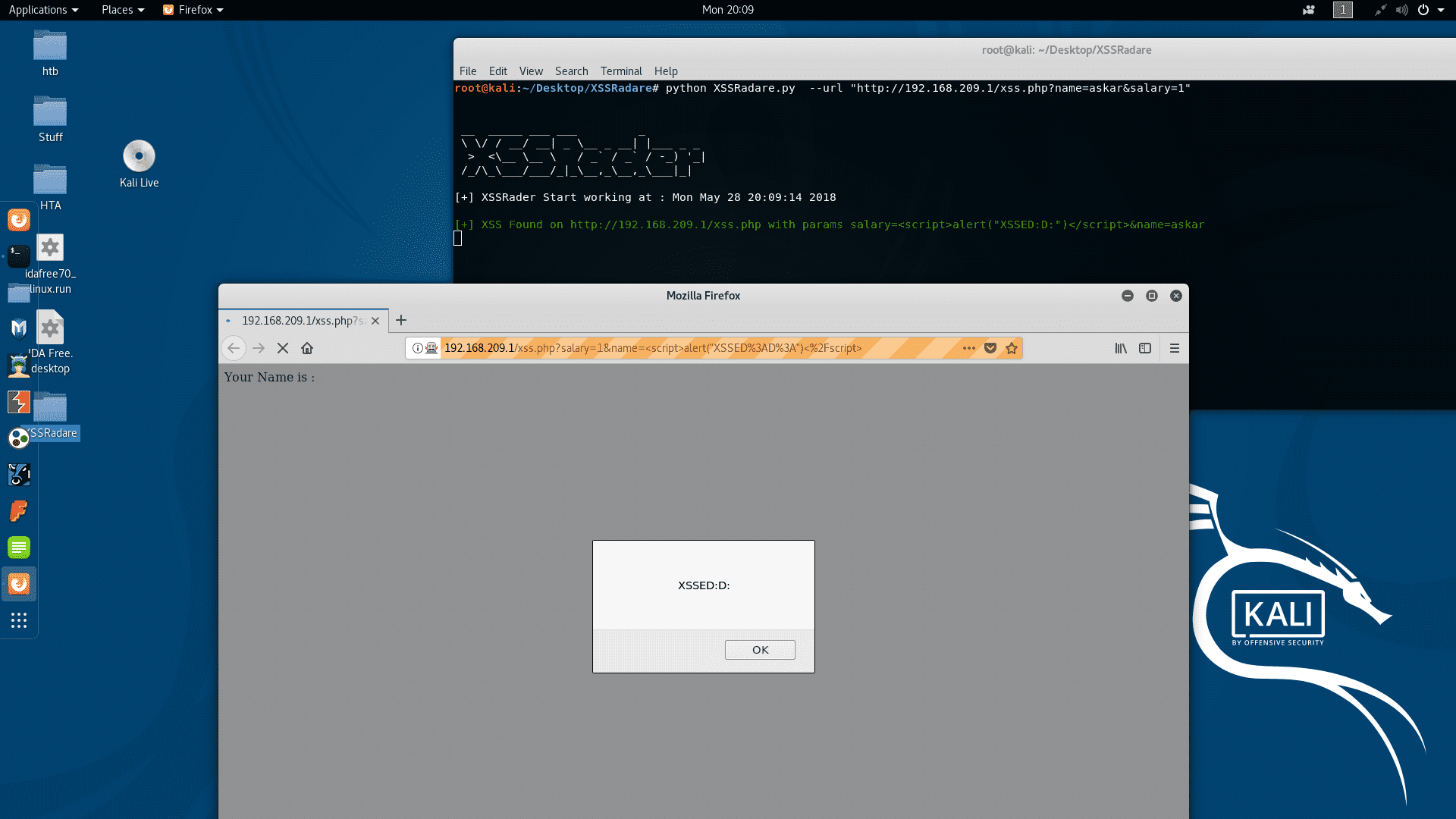
XSSRadare: Cross Site Scripting scanner using selenium webdriver
XSSRadare
Cross Site Scripting (XSS) scanner based on selenium webdriver
using XSSRadare you can scan a single URL or multiple URLs from XSS by using selenium web driver as a fuzzing interface, XSSRadare will help you to identify any XSS vulnerability in your web application.
XSSRadare will use some hardcoded payloads to test for XSS, for now, we prefer to write payload that contains alert javascript function because we already implemented the fuzzer to test for any alert triggered in the scanned page.
Installation
git clone https://github.com/mhaskar/XSSRadare.git
Requirement
You can install all the dependencies for XSSRadare using the following commands :
sudo ./system_requirments.sh
And make sure to add this line to your .bashrc file manually :
export PATH=$PATH:/opt/geckodriver
This line will make sure to link the geckodriver path to your current PATH so the XSSRadare can recognize it.
Note : sometimes you need to check your firefox compatibility with geckodriver in order to run the script correctly (currently we are using the latest one “geckodriver-v0.20.1 x64” version) please note the current version of Firefox on Kali Linux is (Firefox 52) which is not supported by the geckodriver version that we are using, so make sure to upgrade your firefox version if you are using Kali Linux, we are working on building a script to automate the whole process for you.
Usage

You can start a simple XSS scan for an url using the following command:
Source: https://github.com/mhaskar/






