AIL framework v5.3 released: Analysis Information Leak framework
AIL framework
AIL framework – Framework for Analysis of Information Leaks
AIL is a modular framework to analyze potential information leaks from unstructured data sources like pastes from Pastebin or similar services or unstructured data streams. AIL framework is flexible and can be extended to support other functionalities to mine sensitive information.
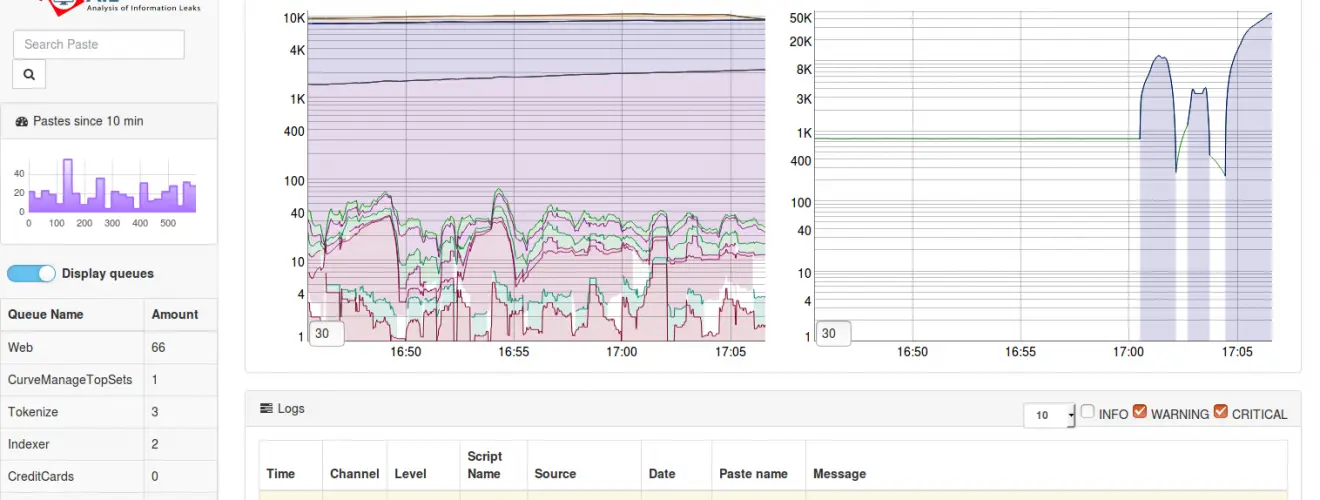
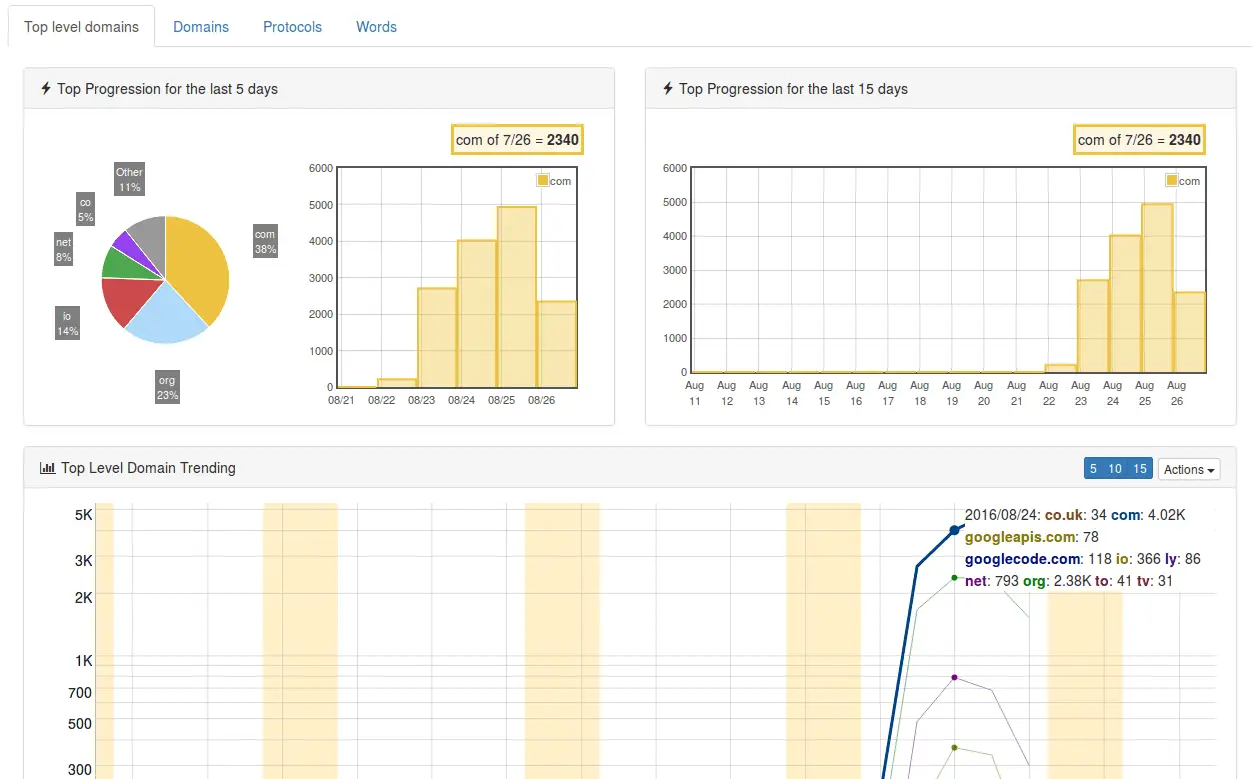
Trending charts
Features
- Modular architecture to handle streams of unstructured or structured information
- Default support for external ZMQ feeds, such as provided by CIRCL or other providers
- Multiple feed support
- Each module can process and reprocess the information already processed by AIL
- Detecting and extracting URLs including their geographical location (e.g. IP address location)
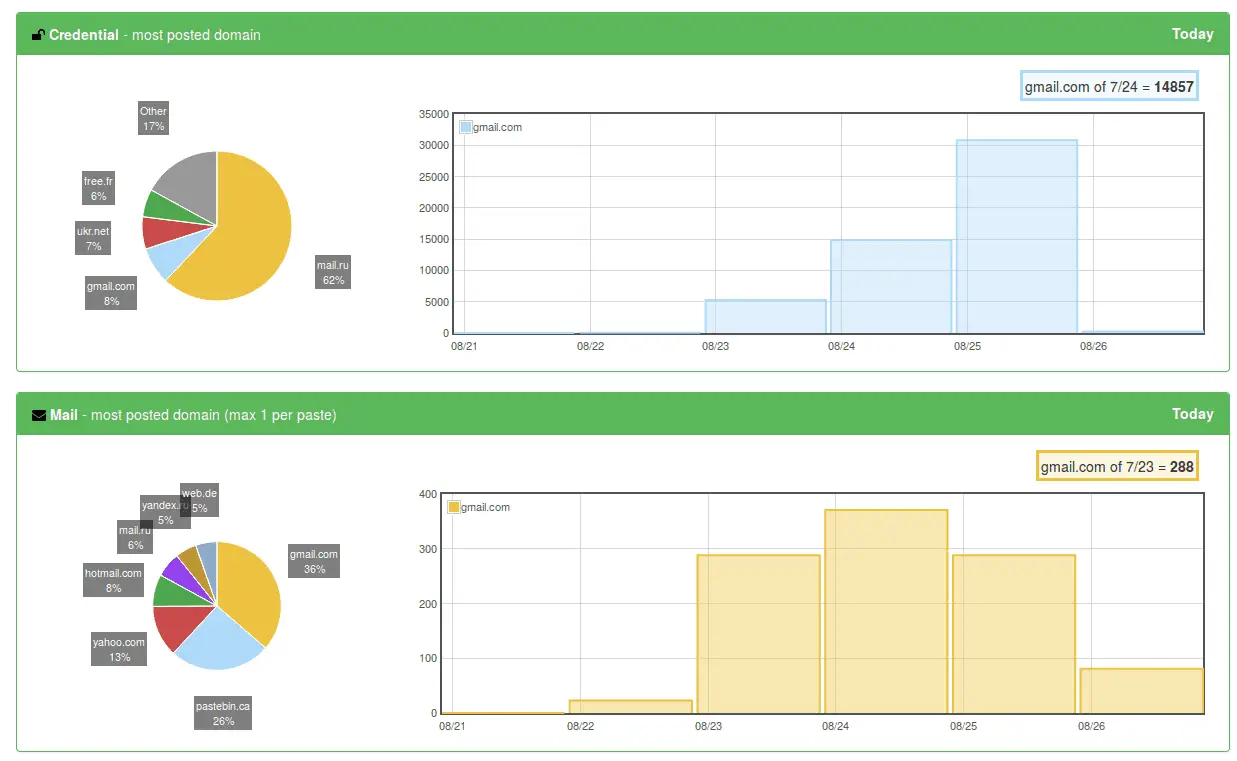
- Extracting and validating potential leak of credit cards numbers, credentials, …
- Extracting and validating email addresses leaked including DNS MX validation
- Module for extracting Tor .onion addresses (to be further processed for analysis)
- Keep tracks of duplicates (and diffing between each duplicate found)
- Extracting and validating potential hostnames (e.g. to feed Passive DNS systems)
- A full-text indexer module to index unstructured information
- Statistics on modules and web
- Real-time modules manager in terminal
- Global sentiment analysis for each providers based on nltk vader module
- Terms, Set of terms and Regex tracking and occurrence
- Many more modules for extracting phone numbers, credentials and others
- Alerting to MISP to share found leaks within a threat intelligence platform using MISP standard
- Detect and decode Base64 and store files
- Detect Amazon AWS and Google API keys
- Detect Bitcoin address and Bitcoin private keys
- Detect private keys and certificate
- Tagging system with MISP Galaxy and MISP Taxonomies tags
- UI paste submission
- Create events on MISP and cases on The Hive
- Automatic paste export at detection on MISP (events) and The Hive (alerts) on selected tags
Install & Use
Copyright (C) 2014 Jules Debra
Copyright (C) 2014-2018 CIRCL – Computer Incident Response Center Luxembourg (c/o smile, security made in Lëtzebuerg, Groupement d’Intérêt Economique)
Copyright (c) 2014-2018 Raphaël Vinot
Copyright (c) 2014-2018 Alexandre Dulaunoy
Copyright (c) 2016-2018 Sami Mokaddem
Copyright (c) 2018 Thirion Aurélien
Source: https://github.com/CIRCL/






