Attack Surface Analyzer v2.3.303 releases: analyze your operating system’s security configuration
Attack Surface Analyzer
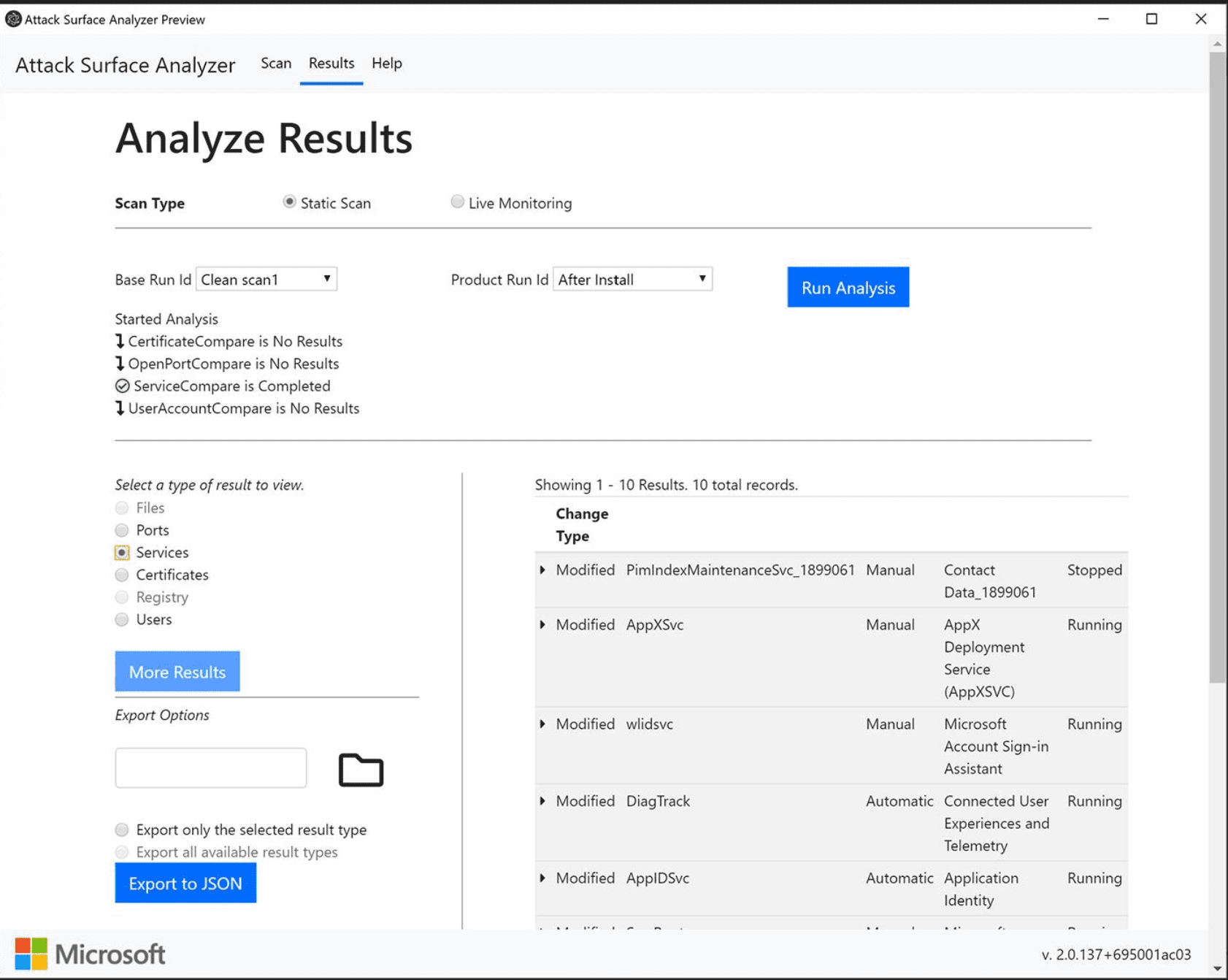
Attack Surface Analyzer (ASA) is a Microsoft-developed open source security tool that analyzes the attack surface of a target system and reports on potential security vulnerabilities introduced during the installation of software or system misconfiguration.
Why Attack Surface Analyzer
ASA is a Microsoft-developed Security tool that analyzes the attack surface of a Windows 10, Linux or MacOS system and reports on system changes that may have potential security implications that are introduced by the installation of software or by system misconfiguration.
ASA 1.0 classic from Microsoft was released in 2012 and while still available it is no longer supported. Attack Surface Analyzer 1,.0 has been valuable to software developers and IT security personnel for years in helping detect key system changes that may occur from software installation.
ASA 2.0 is a rewrite from the ground up on Microsoft .NET Core and Electron and is deployed as Open Source for contribution and customization. Note: the official or master branch of the code is still managed by Microsoft.
Scenarios
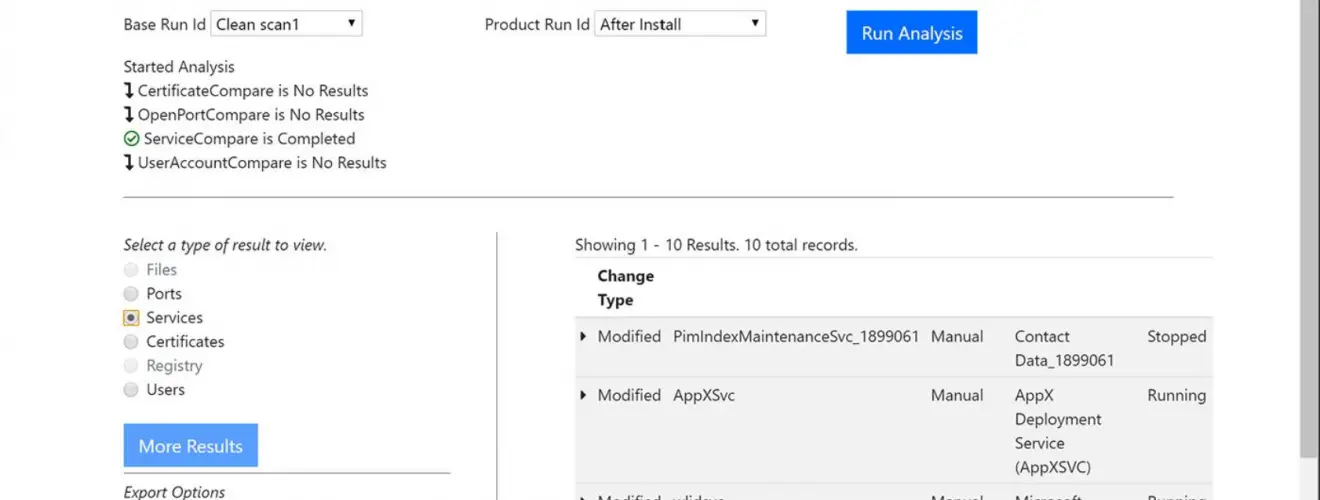
- Attack Surface Analyzer can help identify potential security risks exposed through changes to services, user accounts, files, network ports, certificate stores, and the system registry. It also includes some support for “live” monitoring of certain system changes (i.e. file system and registry).
- Another key use for the tool is in ensuring your software development process and products are following best practices for least privilege and reducing the attack surface for your customers by providing evidence, to your security and release teams, that your code does only what it claims. Maintaining customer trust is one reason why it is recommended from the Microsoft SDL Practices.
Potential users of ASA include:
- DevOps Engineers – View changes to the system attack surface introduced when your software is installed.
- IT Security Auditors – Evaluate risk presented by when third-party software is installed.
Core Features
The core feature of Attack Surface Analyzer is the ability to “diff” an operating system’s security configuration, before and after a software component is installed. This is important because most installation processes require elevated privileges, and once granted, can lead to unintended system configuration changes.
Attack Surface Analyzer currently reports on changes to the following operating system components:
- File system (static snapshot and live monitoring available)
- User accounts
- Services
- Network Ports
- Certificates
- Registry (Windows only)
All data collected is stored in a local SQLite database called asa.sqlite.
Changelog v2.3.303
Download && Use
Copyright (c) Microsoft Corporation. All rights reserved.