Attack Surface Mapper: automate the reconnaissance process
Attack Surface Mapper
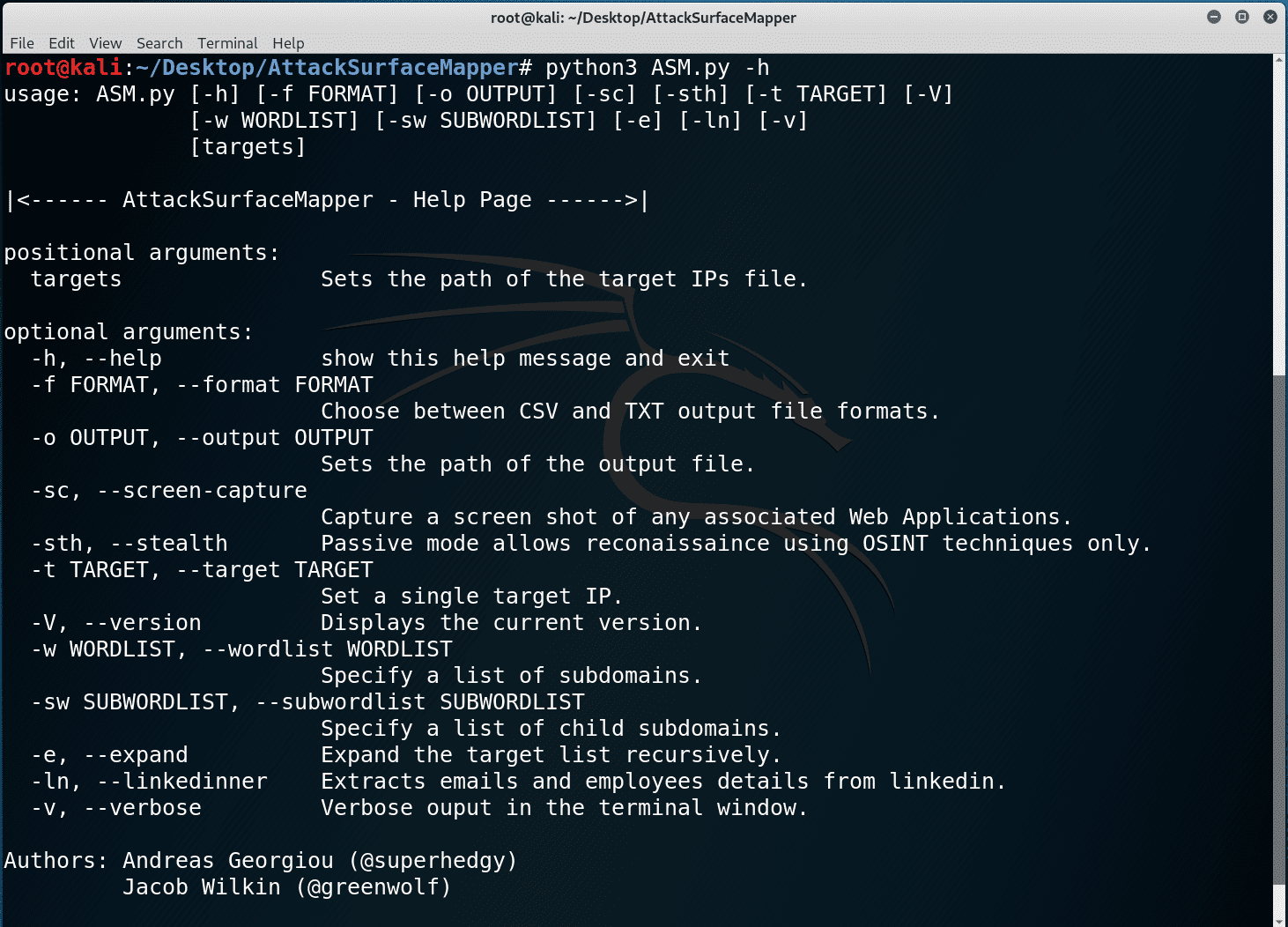
Attack Surface Mapper is a reconnaissance tool that uses a mixture of open-source intelligence and active techniques to expand the attack surface of your target. You feed in a mixture of one or more domains, subdomains, and IP addresses and it uses numerous techniques to find more targets. It enumerates subdomains with bruteforcing and passive lookups, Other IPs of the same network block owner, IPs that have multiple domain names pointing to them and so on.
Once the target list is fully expanded it performs passive reconnaissance on them, taking screenshots of websites, generating visual maps, looking up credentials in public breaches, passive port scanning with Shodan and scraping employees from LinkedIn.
What this means is you’re left with hard actionable data gathered from these processes, targets to scan, websites to attack, email addresses to phish and credentials to bruteforce and spray.
Install
$ git clone https://github.com/superhedgy/AttackSurfaceMapper
$ cd AttackSurfaceMapper
$ python3 -m pip install –no-cache-dir -r requirements.txt
Provide Attack Surface Mapper with optional API keys to enable more data gathering
Open keylist.asm and enter the API Keys.
Use
Demo
Copyright (C) 2019 superhedgy
Source: https://github.com/superhedgy/





