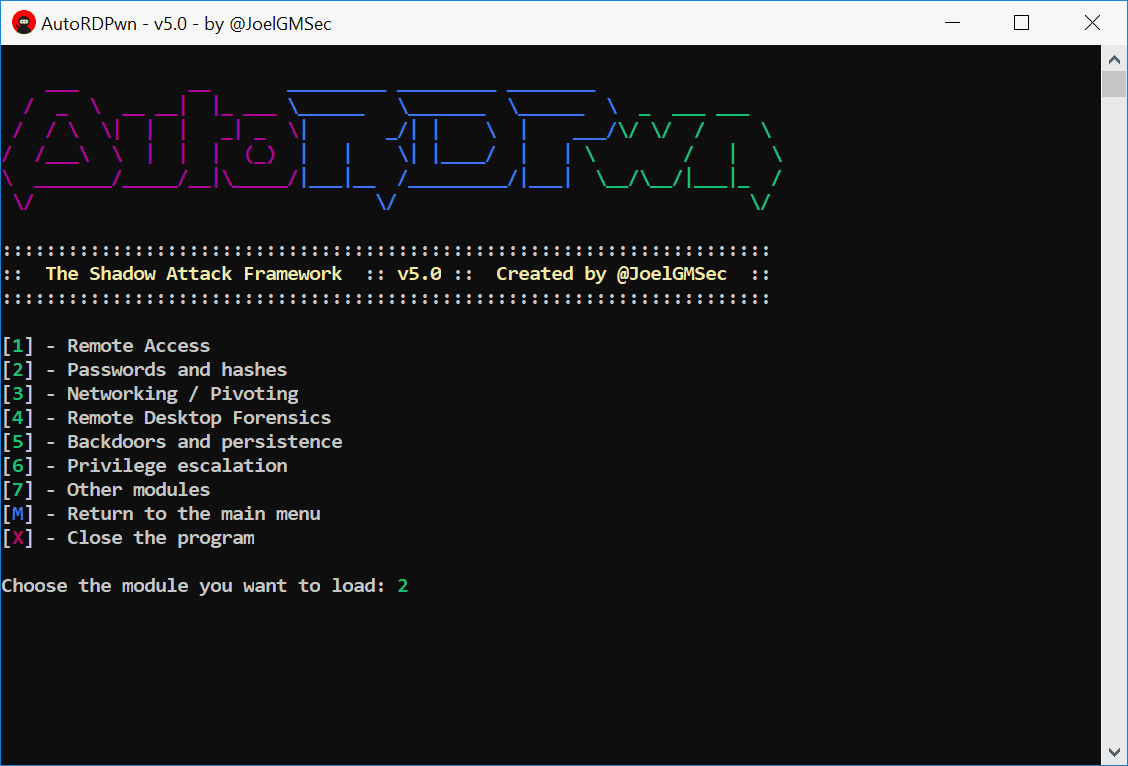
AutoRDPwn v5.1 releases: The Shadow Attack Framework

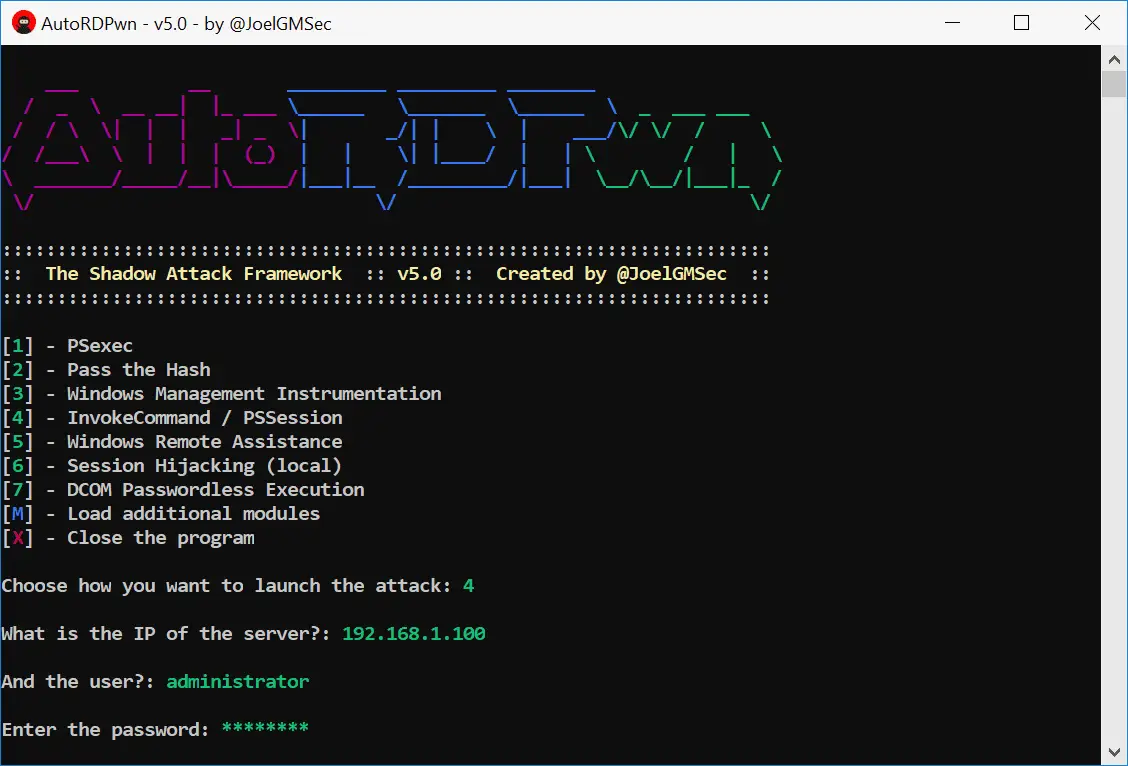
AutoRDPwn is a script created in Powershell and designed to automate the Shadow attack on Microsoft Windows computers. This vulnerability allows a remote attacker to view his victim’s desktop without his consent, and even control it on request. For its correct operation, it is necessary to comply with the requirements described in the user guide.
Download
Requirement
Powershell 5.0 or higher
git clone https://github.com/JoelGMSec/AutoRDPwn.git
Version 5.1
Many bugs fixed
• Aesthetic improvements and improved waiting times
• Proxy-Aware connection through system settings
• It is now possible to use the offline tool by downloading the .zip file
• Language auto-detection by pressing the enter key
• Invoke-DCOM has been replaced by SharpRDP
• PowerUp has been replaced by Invoke-PrivescCheck
• Creation of the automatic cleaning subroutine in the victim
• New module available: SMB Shell encrypted with AES
• New module available: Change user with RunAs
* The rest of the changes can be consulted in the CHANGELOG file
Use
This application can be used locally, remotely or to pivot between computers. Thanks to the additional modules, it is possible to dump hashes and passwords or even recover the history of RDP connections.
One line execution:
powershell -ep bypass “cd $env:temp ; iwr https://darkbyte.net/autordpwn.php -outfile AutoRDPwn.ps1 ; .\AutoRDPwn.ps1”
The detailed guide of use can be found at this link.
Copyright (C) 2018 JoelGMSec
Source: https://github.com/JoelGMSec/