AutoSploit v4.0 releases: Automated Mass Exploiter
AutoSploit
As the name might suggest AutoSploit attempts to automate the exploitation of remote hosts. Targets are collected automatically as well by employing the Shodan.io API. The program allows the user to enter their platform-specific search query such as; Apache, IIS, etc, upon which a list of candidates will be retrieved.
After this operation has been completed the ‘Exploit’ component of the program will go about the business of attempting to exploit these targets by running a series of Metasploit modules against them. Which Metasploit modules will be employed in this manner is determined by programmatically comparing the name of the module to the initial search query. However, I have added functionality to run all available modules against the targets in a ‘Hail Mary’ type of attack as well.
The available Metasploit modules have been selected to facilitate Remote Code Execution and to attempt to gain Reverse TCP Shells and/or Meterpreter sessions. Workspace, localhost and local port for MSF facilitated back connections are configured through the dialog that comes up before the ‘Exploit’ component is started.
Operational Security Consideration
Receiving back connections on your local machine might not be the best idea from an OPSEC standpoint. Instead consider running this tool from a VPS that has all the dependencies required, available.
Changelog v4.0
Fixes:
Implements the ability to use nmap from within the terminal function as a “local” system. Meaning that instead of having multiple tabs open to nmap and attack you can now nmap from within the shell and make your choice on what to target
Usage
Clone the repo. Or deploy via Docker. Details for which can be found here Special thanks to Khast3x for their contribution in this regard.
git clone https://github.com/NullArray/AutoSploit.git
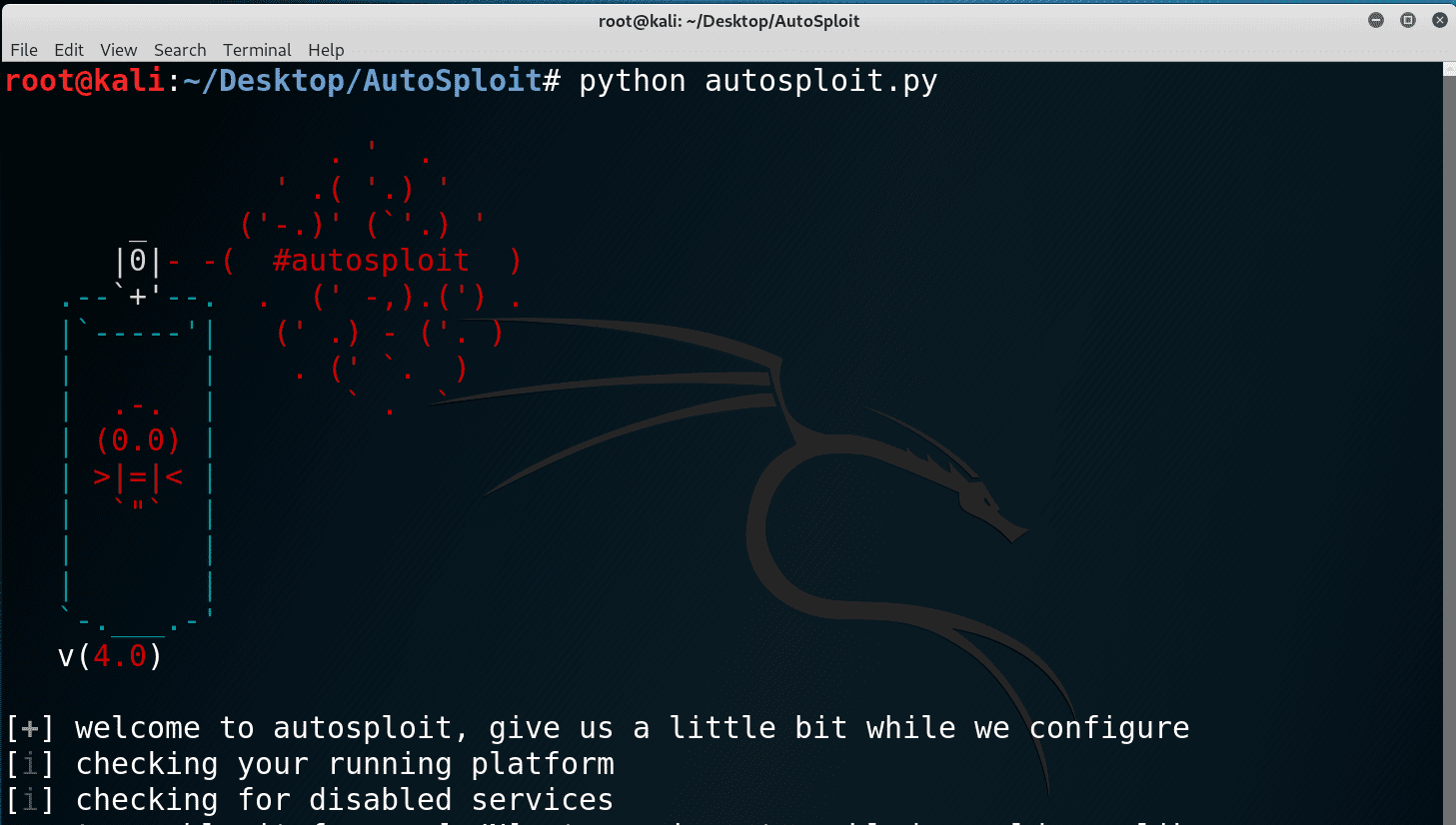
After which it can be started from the terminal with python autosploit.py.
As of version 2.0, AutoSploit can be started with a number of command-line arguments/flags as well. Type python autosploit.py -h to display all the options available to you.
Copyright (C) 2018 NullArray
Source: https://github.com/NullArray/