bluing
Bluing (formerly bluescan) is a Bluetooth Intelligence Gathering tool written primarily in Python. It can help us snoop on the internal structure of Bluetooth which is a complex protocol or hack Bluetooth devices. Here are the main features of the tool:
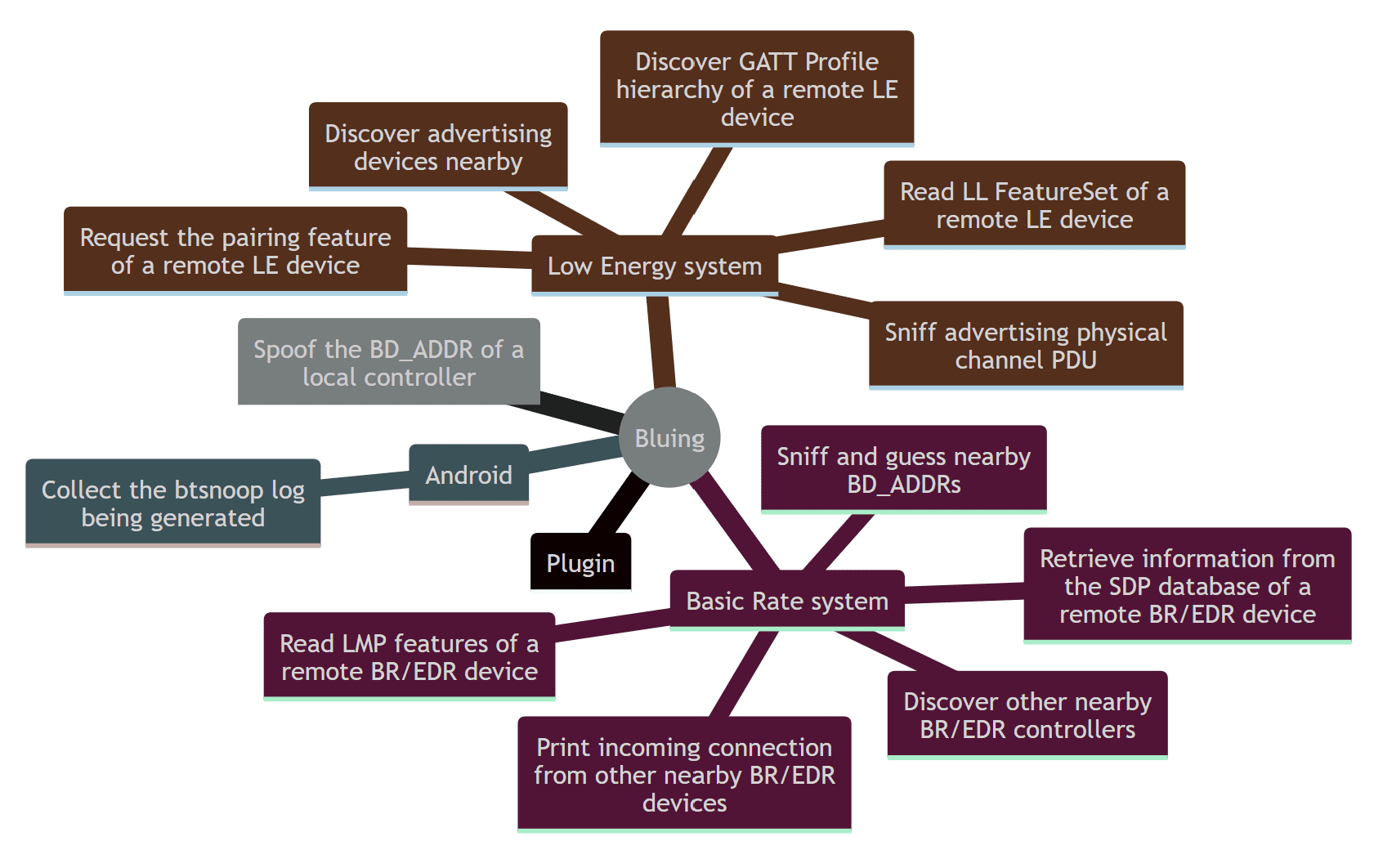
When hacking new Bluetooth targets, the scanner can help us to collect intelligence, such as:
- BR devices
- LE devices
- LMP features
- GATT services
- SDP services
- Vulnerabilities (demo)
Changelog v0.12
- Added
spoofsubcommand - Added 3 spoofing features for falsifying the Class of Device, host name, and controller alias
- Other little improvements
Requirements
This tool is based on BlueZ, the official Linux Bluetooth stack. The following packages need to be installed:
sudo apt install libglib2.0-dev libbluetooth-dev
When you play this tool in a Linux virtual machine, connecting a USB Bluetooth adapter using a Broadcom or CSR chip is recommended, like the Ostran Bluetooth USB Adapter OST-105 CSR 8150 v4.0. And if you want to try the vulnerability scanning, see README.md of ojasookert/CVE-2017-0785.
Install
Bluing partially depend on BlueZ, the official Linux Bluetooth protocol stack. So it only supports running on Linux. The following command is used to install dependencies:
The latest bluescan will be uploaded to PyPI, so the following command can install bluescan:
sudo pip3.10 install bluing
Usage
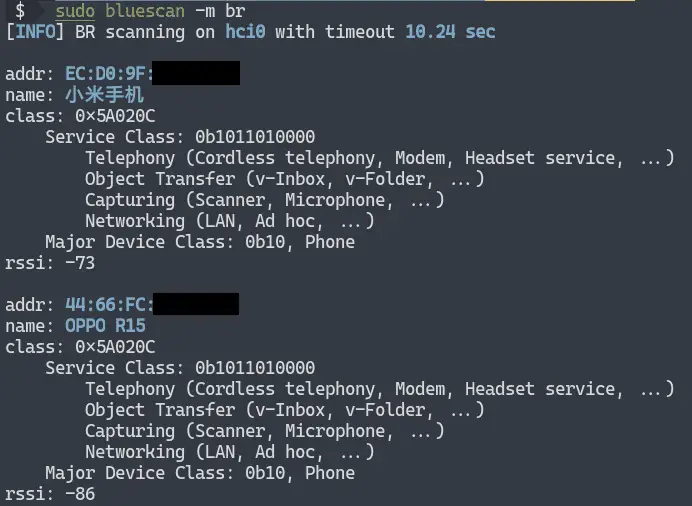
Scan BR devices -m br
Classic Bluetooth devices may use three technologies: BR (Basic Rate), EDR (Enhanced Data Rate), and AMP (Alternate MAC/PHY). Since they all belong to the Basic Rate system, so when scanning these devices we call them BR device scanning:
As shown above, through BR device scanning, we can get the address, name, device type, and RSSI of the surrounding classic Bluetooth devices.
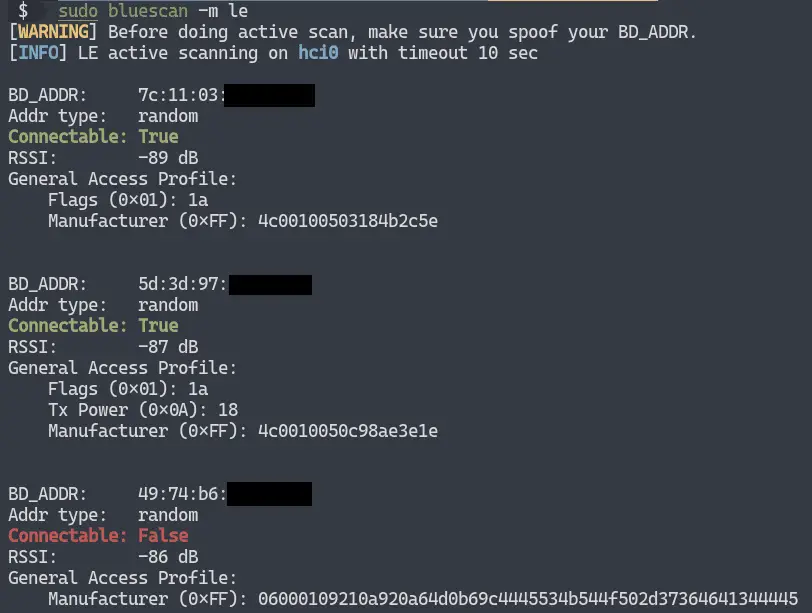
Scan LE devices -m le
Bluetooth technology, in addition to the Basic Rate system, is Low Energy (LE) system. When scanning Bluetooth low energy devices, it is called LE device scanning:
As shown above, through LE device scanning, we can get the address, address type, connection status, RSSI, and GAP data of the surrounding LE devices.
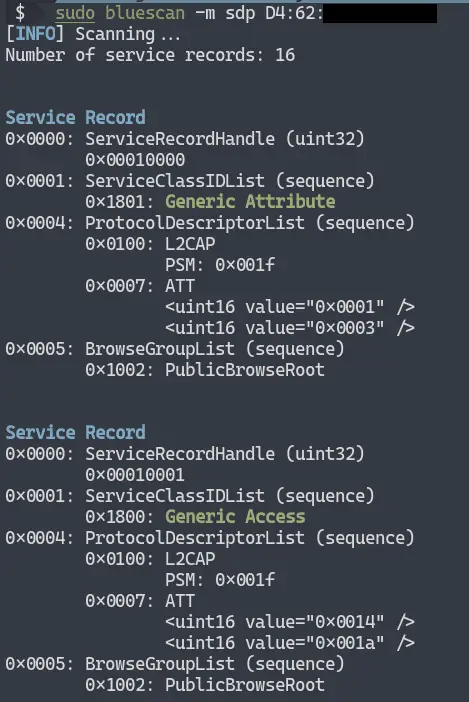
Scan SDP services
Classic Bluetooth devices tell the outside world about their open services through SDP. After SDP scanning, we can get service records of the specified classic Bluetooth device:
You can try to connect to these services for further hacking.
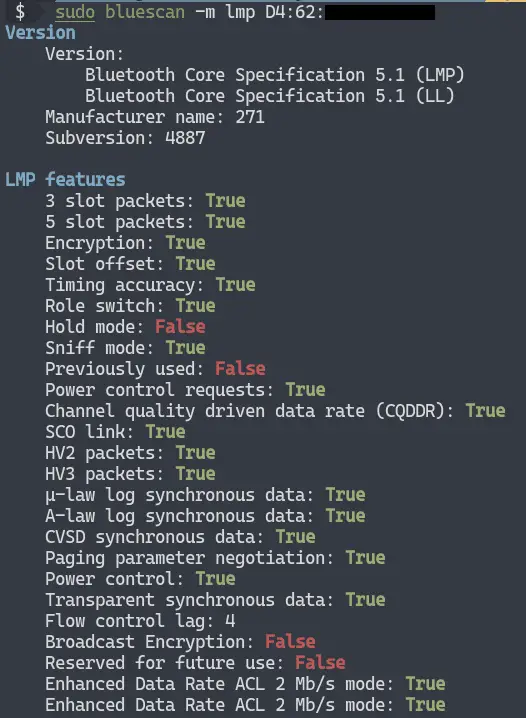
Scan LMP features
Detecting the LMP features of classic Bluetooth devices allows us to judge the underlying security features of the classic Bluetooth device:
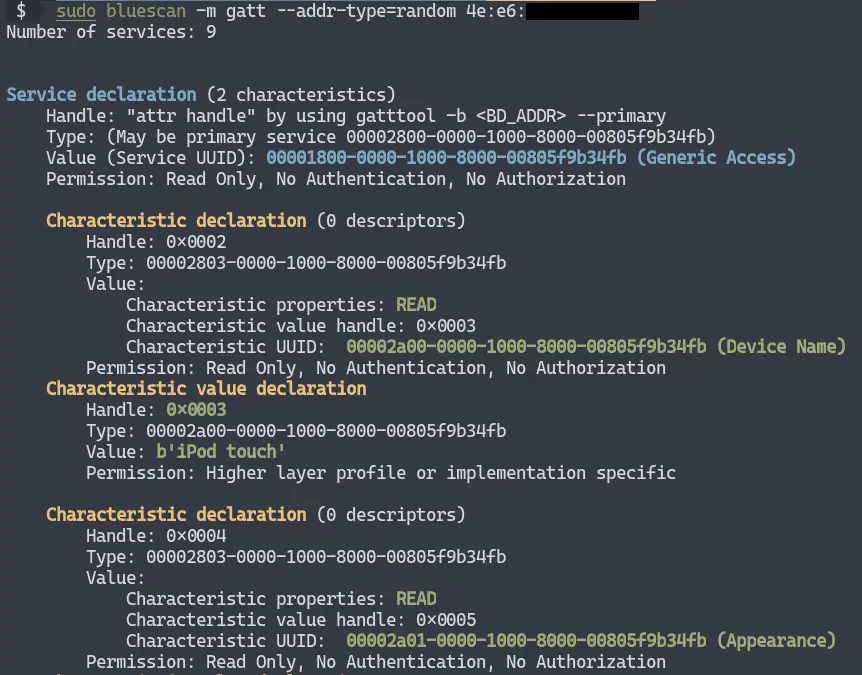
Scan GATT services
LE devices tell the outside world about their open services through GATT. After GATT scanning, we can get the GATT service of the specified LE device. You can try to read and write these GATT data for further hacking:
Vulnerabilities scanning (demo)
Vulnerability scanning is still in the demo stage, and currently only supports CVE-2017-0785:
Copyright (C) 2020 fO-000
Source: https://github.com/fO-000/