Bolt
A dumb CSRF scanner
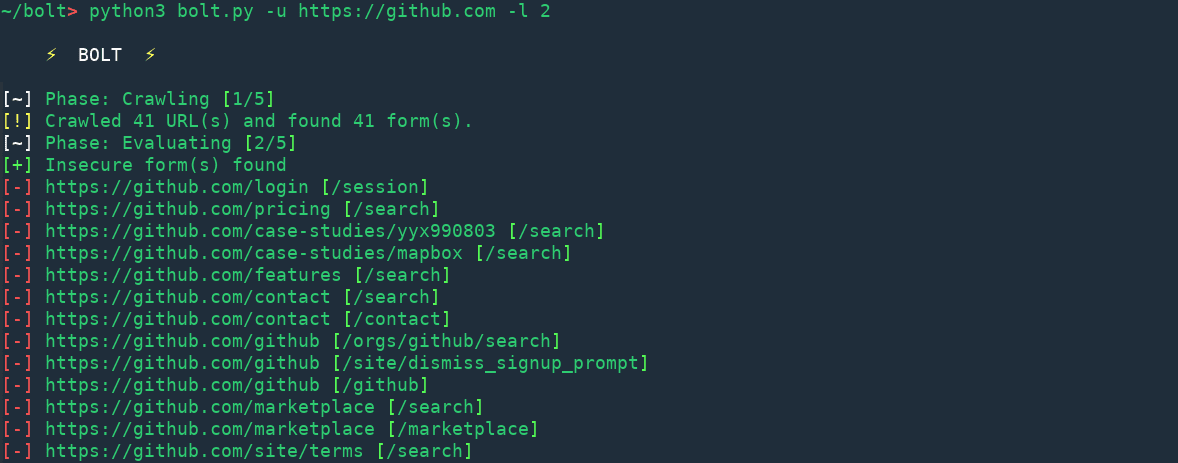
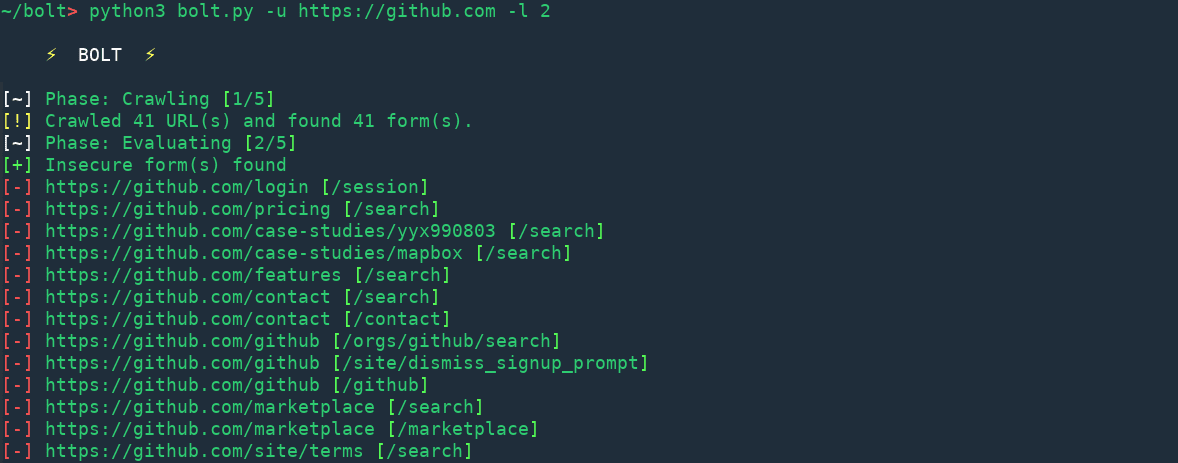
Workflow
Crawling
Bolt crawls the target website to the specified depth and stores all the HTML forms found in a database for further processing.
Evaluating
In this phase, Bolt finds out the tokens which aren’t strong enough and the forms which aren’t protected.
Comparing
This phase focuses on detection on replay attack scenarios and hence checks if a token has been issued more than one time. It also calculates the average levenshtein distance between all the tokens to see if they are similar.
Tokens are also compared against a database of 250+ hash patterns.
Observing
In this phase, 100 simultaneous requests are made to a single webpage to see if same tokens are generated for the requests.
Testing
This phase is dedicated to active testing of the CSRF protection mechanism. It includes but not limited to checking if protection exsists for moblie browsers, submitting requests with self-generated token and testing if token is being checked to a certain length.
Analysing
Various statistical checks are performed in this phase to see if the token is really random. Following tests are performed during this phase
- Monobit frequency test
- Block frequency test
- Runs test
- Spectral test
- Non-overlapping template matching test
- Overlapping template matching test
- Serial test
- Cumultative sums test
- Aproximate entropy test
- Random excursions variant test
- Linear complexity test
- Longest runs test
- Maurers universal statistic test
- Random excursions test
Changelog v0.2.1
- Several bug fixes
- Added common substring test
- Added 14 statistical tests
- Monobit frequency test
- Block frequency test
- Runs test
- Spectral test
- Non-overlapping template matching test
- Overlapping template matching test
- Serial test
- Cumulative sums test
- Approximate entropy test
- Random excursions variant test
- Linear complexity test
- Longest runs test
- Maurers universal statistic test
- Random excursions test
Download
git clone https://github.com/s0md3v/Bolt.git
Usage
Scanning a website for CSRF using Bolt is as easy as doing
python3 bolt.py -u https://github.com -l 2
Where -u is used to supplying the URL and -l is used to specify the depth of crawling.
Other options and switches:
- -t number of threads
- –delay delay between requests
- –timeout http request timeout
- –headers supply http headers
Copyright (C) 2018 s0md3v
Source: https://github.com/s0md3v/