Category: Smartphone PenTest
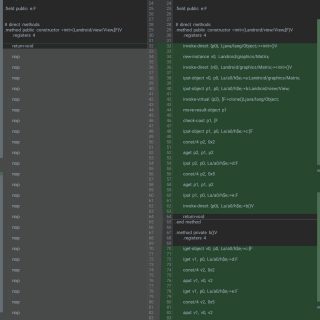
Android Disassembler Analyze malicious app on your phone Android Disassembler is an application that is able to analyze several types of files such as APK files, dex files, shared libraries (aka .so files) (NDK,...
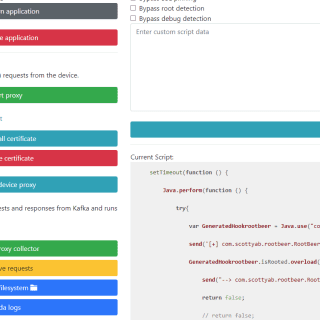
Aparoid Aparoid is a framework designed for Android application analysis. It offers an automated set of tools to discover vulnerabilities and other risks in mobile applications. It is built using the Flask framework and...
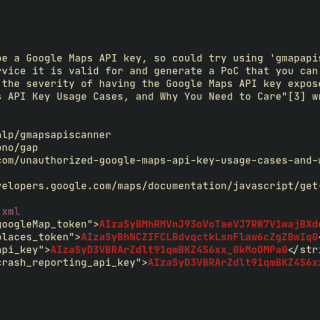
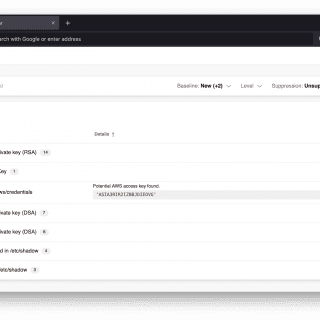
dora Find exposed API keys based on RegEx and get exploitation methods for some of the keys that are found. Features Blazing fast as we are using ripgrep in the backend Exploit/PoC steps for...
Mariana Trench Mariana Trench is a security-focused static analysis platform targeting Android. The tool provides an extensible global taint analysis similar to pre-existing tools like Pysa for Python. The tool leverages existing static analysis infrastructure (e.g, SPARTA)...
Static Token And Credential Scanner STACS is a YARA-powered static credential scanner that supports binary file formats, analysis of nested archives, composable rulesets and ignores lists, and SARIF reporting. What does STACS support? Currently,...
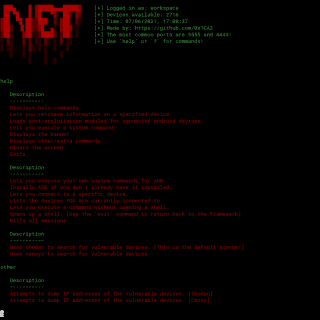
AdbNet A Framework that allows you to search for vulnerable android devices across the world and exploit them. Features: – Post-Exploitation modules to control and tinker with the device you are connected to. –...
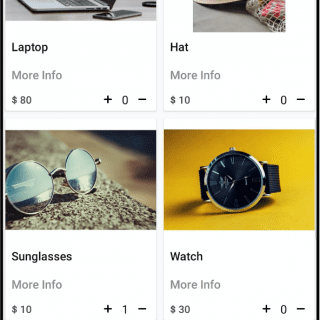
InsecureShop InsecureShop is an Android application that is designed to be intentionally vulnerable. The aim of creating this app is to teach developers and security professionals about the vulnerabilities that are present in modern...
Solitude Solitude is a privacy analysis tool that enables anyone to conduct their own privacy investigations. Whether a curious novice or a more advanced researcher, Solitude makes the process of evaluating user privacy within...
BlackDex BlackDex is an Android unpack tool, it supports Android 5.0~12 and need not rely to any environment. BlackDex can run on any Android mobile phone or emulator, you can unpack APK File in...
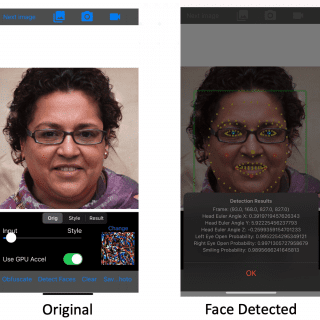
Ruse Mobile camera-based application that attempts to alter photos to preserve their utility to humans while making them unusable for facial recognition systems. Usage example The app is developed as a camera-based app, allowing...
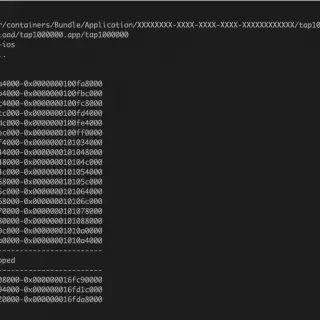
ipa-medit Ipa-medit is a memory search and patch tool for resigned ipa without jailbreak. It was created for mobile game security testing. Motivation Memory modification is the easiest way to cheat in games, it...
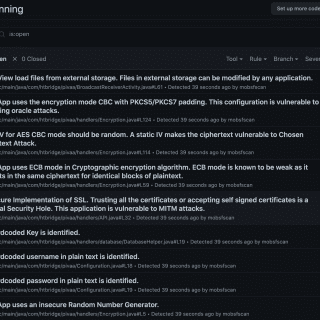
mobsfscan mobsfscan is a static analysis tool that can find insecure code patterns in your Android and iOS source code. Supports Java, Kotlin, Swift, and Objective C Code. mobsfscan uses MobSF static analysis rules and is powered...
iPwn A Framework meant for the exploitation of iOS devices. iPwn is a framework meant for exploiting and gaining access to iOS devices. It also has an extension that is a mini-framework called ‘iSteal’...
Allsafe Allsafe is an intentionally vulnerable application that contains various vulnerabilities. Unlike other vulnerable Android apps, this one is less like a CTF and more like a real-life application that uses modern libraries and...
Damn Vulnerable Bank Damn Vulnerable Bank Android Application aims to provide an interface for everyone to get a detailed understanding of the internal and security aspects of android applications. Features Sign up Login My...