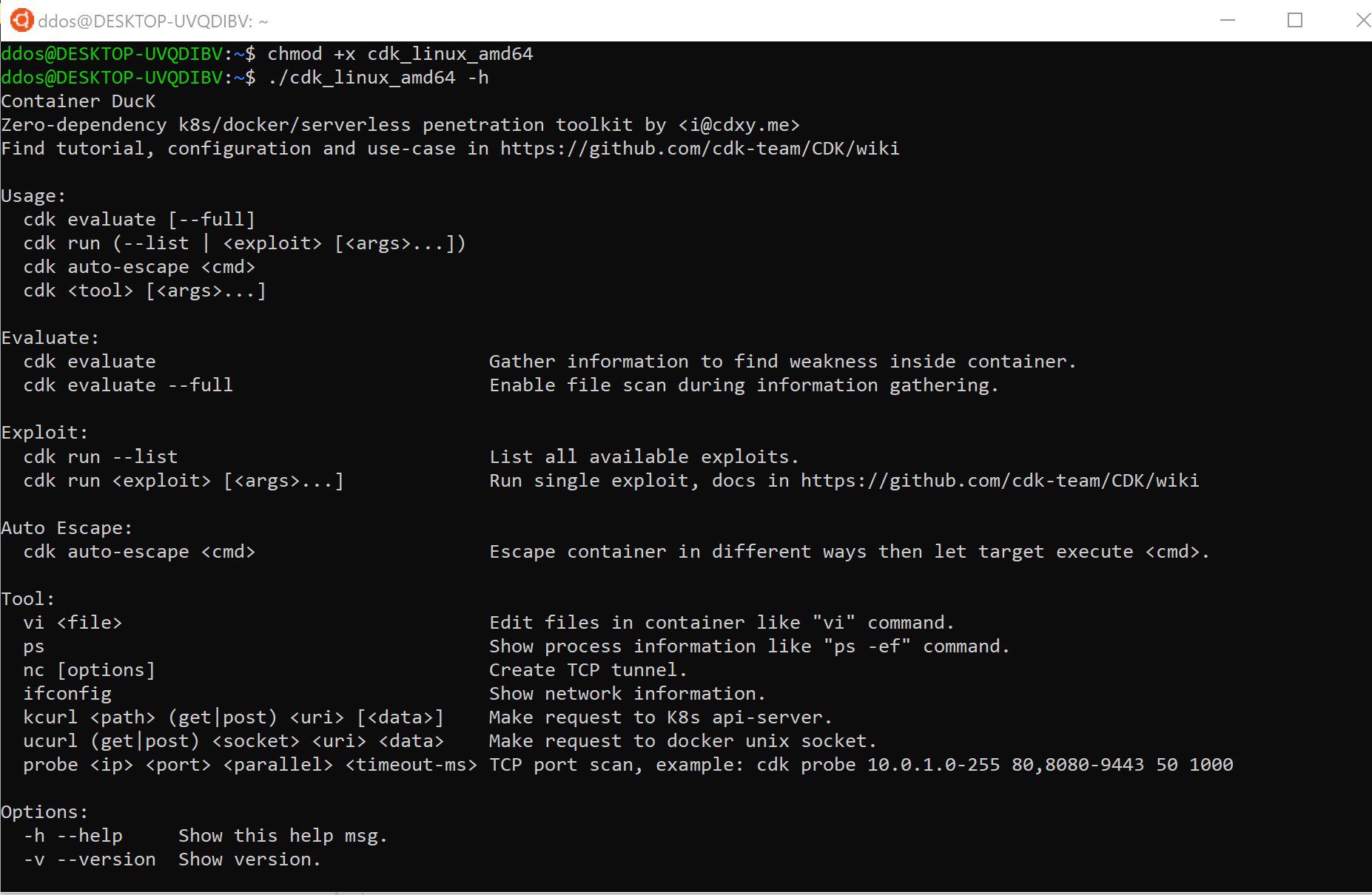
CDK – Zero Dependency Container Penetration Toolkit
CDK is an open-sourced container penetration toolkit, designed for offering stable exploitation in different slimmed containers without any OS dependency. It comes with useful net-tools and many powerful PoCs/EXPs and helps you to escape the container and take over the K8s cluster easily.
Features
CDK has three modules:
- Evaluate: gather information inside the container to find the potential weaknesses.
- Exploit: for container escaping, persistence, and lateral movement
- Tool: network-tools and APIs for TCP/HTTP requests, tunnels, and K8s cluster management.
Evaluate Module
Usage
cdk evaluate [--full]
This command will run the scripts below without local file scanning, using –full to enable all.
| Tactics | Script | Supported | Usage/Example |
|---|---|---|---|
| Information Gathering | OS Basic Info | ✔ | link |
| Information Gathering | Available Capabilities | ✔ | link |
| Information Gathering | Available Linux Commands | ✔ | link |
| Information Gathering | Mounts | ✔ | link |
| Information Gathering | Net Namespace | ✔ | link |
| Information Gathering | Sensitive ENV | ✔ | link |
| Information Gathering | Sensitive Process | ✔ | link |
| Information Gathering | Sensitive Local Files | ✔ | link |
| Information Gathering | Kube-proxy Route Localnet(CVE-2020-8558) | ✔ | link |
| Discovery | K8s Api-server Info | ✔ | link |
| Discovery | K8s Service-account Info | ✔ | link |
| Discovery | Cloud Provider Metadata API | ✔ | link |
Exploit Module
List all available exploits:
cdk run --list
Run targeted exploit:
cdk run <script-name> [options]
| Tactic | Technique | CDK Exploit Name | Supported | In Thin | Doc |
|---|---|---|---|---|---|
| Escaping | docker-runc CVE-2019-5736 | runc-pwn | ✔ | ✔ | |
| Escaping | containerd-shim CVE-2020-15257 | shim-pwn | ✔ | link | |
| Escaping | docker.sock PoC (DIND attack) | docker-sock-check | ✔ | ✔ | link |
| Escaping | docker.sock RCE | docker-sock-pwn | ✔ | ✔ | link |
| Escaping | Docker API(2375) RCE | docker-api-pwn | ✔ | ✔ | link |
| Escaping | Device Mount Escaping | mount-disk | ✔ | ✔ | link |
| Escaping | LXCFS Escaping | lxcfs-rw | ✔ | ✔ | link |
| Escaping | Cgroups Escaping | mount-cgroup | ✔ | ✔ | link |
| Escaping | Procfs Escaping | mount-procfs | ✔ | ✔ | link |
| Escaping | Ptrace Escaping PoC | check-ptrace | ✔ | ✔ | link |
| Escaping | Rewrite Cgroup(devices.allow) | rewrite-cgroup-devices | ✔ | ✔ | link |
| Escaping | Read arbitrary file from host system (CAP_DAC_READ_SEARCH) | cap-dac-read-search | ✔ | ✔ | link |
| Discovery | K8s Component Probe | service-probe | ✔ | ✔ | link |
| Discovery | Dump Istio Sidecar Meta | istio-check | ✔ | ✔ | link |
| Discovery | Dump K8s Pod Security Policies | k8s-psp-dump | ✔ | link | |
| Remote Control | Reverse Shell | reverse-shell | ✔ | ✔ | link |
| Credential Access | Access Key Scanning | ak-leakage | ✔ | ✔ | link |
| Credential Access | Dump K8s Secrets | k8s-secret-dump | ✔ | ✔ | link |
| Credential Access | Dump K8s Config | k8s-configmap-dump | ✔ | ✔ | link |
| Privilege Escalation | K8s RBAC Bypass | k8s-get-sa-token | ✔ | ✔ | link |
| Persistence | Deploy WebShell | webshell-deploy | ✔ | ✔ | link |
| Persistence | Deploy Backdoor Pod | k8s-backdoor-daemonset | ✔ | ✔ | link |
| Persistence | Deploy Shadow K8s api-server | k8s-shadow-apiserver | ✔ | link | |
| Persistence | K8s MITM Attack (CVE-2020-8554) | k8s-mitm-clusterip | ✔ | ✔ | link |
| Persistence | Deploy K8s CronJob | k8s-cronjob | ✔ | ✔ | link |
Note about Thin: The thin release is prepared for short-life container shells such as serverless functions. We add build tags in the source code and cut a few exploits to get the binary lighter. The 2MB file contains 90% of CDK functions, also you can pick up useful exploits in CDK source code to build your own lightweight binary.
Tool Module
Running commands like in Linux, little different in input-args, see the usage link.
cdk nc [options] cdk ps
| Command | Description | Supported | Usage/Example |
|---|---|---|---|
| nc | TCP Tunnel | ✔ | link |
| ps | Process Information | ✔ | link |
| ifconfig | Network Information | ✔ | link |
| vi | Edit Files | ✔ | link |
| kcurl | Request to K8s api-server | ✔ | link |
| dcurl | Request to Docker HTTP API | ✔ | link |
| ucurl | Request to Docker Unix Socket | ✔ | link |
| rcurl | Request to Docker Registry API | ||
| probe | IP/Port Scanning | ✔ | link |
Changelog v1.5.2
💣 Exploits
- Fix 78(exp): support containerd and other linux path
🧰 Tools
- Fix #77(exp shadow-apiserver): anonymous-auth is not valid, support v1.23.1
✨ Others
- Fix 78(exp): support containerd and other linux path
- Chore(exp): add alert message about flag auto-escape is deprecated
Download & Use
Copyright (C) 2021 cdk-team