chisel
Chisel is a fast TCP tunnel, transported over HTTP, secured via SSH. Single executable including both client and server. Written in Go (golang). It is mainly useful for passing through firewalls, though it can also be used to provide a secure endpoint into your network. Chisel is very similar to crowbar though achieves much higher performance.
Features
- Easy to use
- Performant*
- Encrypted connections using the SSH protocol (via
crypto/ssh)
- Authenticated connections; authenticated client connections with a users config file, authenticated server connections with fingerprint matching.
- Client auto-reconnects with exponential backoff
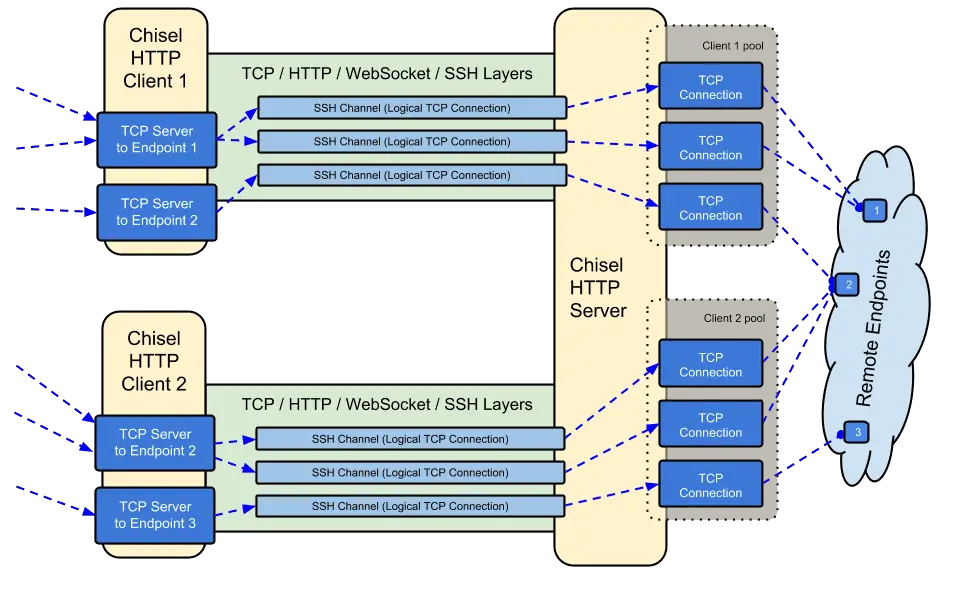
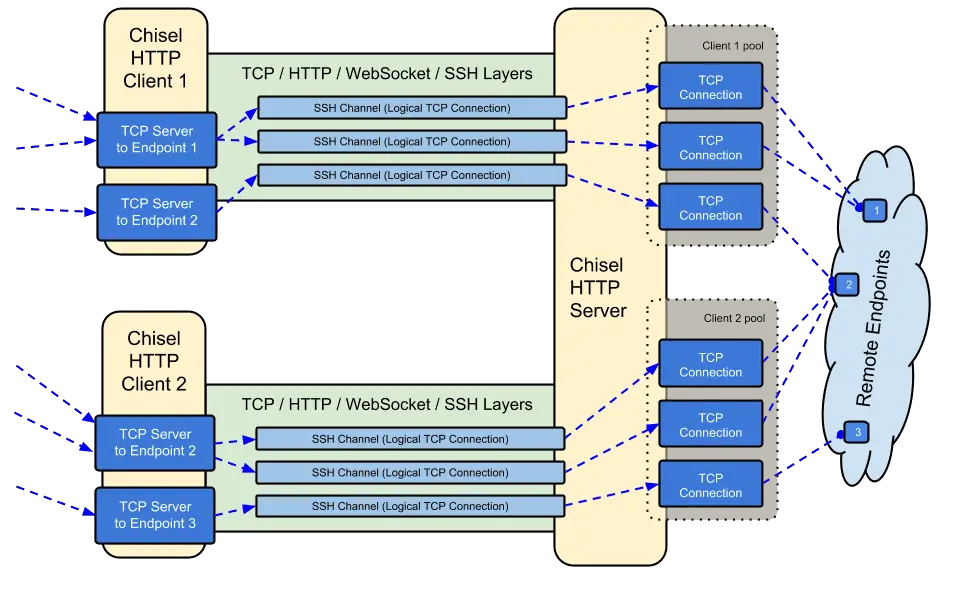
- Client can create multiple tunnel endpoints over one TCP connection
- Client can optionally pass through HTTP CONNECT proxies
- Server optionally doubles as a reverse proxy
- Server optionally allows SOCKS5 connections (See guide below)
- Reverse port forwarding (Connections go through the server and out the client)
Changelog v1.9
- 69093be
- Bump to Go 1.21 (#440) and all dependancies
- Deprecate
--key
- Introduce
--keygen and --keyfile to create and use ECDSA P256 keys
- Many thanks to @cmenginnz
Download
Use
$ chisel server --help
Usage: chisel server [options]
Options:
--host, Defines the HTTP listening host – the network interface
(defaults the environment variable HOST and falls back to 0.0.0.0).
--port, -p, Defines the HTTP listening port (defaults to the environment
variable PORT and fallsback to port 8080).
--key, An optional string to seed the generation of a ECDSA public
and private key pair. All commications will be secured using this
key pair. Share the subsequent fingerprint with clients to enable detection
of man-in-the-middle attacks (defaults to the CHISEL_KEY environment
variable, otherwise a new key is generate each run).
--authfile, An optional path to a users.json file. This file should
be an object with users defined like:
{
"<user:pass>": ["<addr-regex>","<addr-regex>"]
}
when <user> connects, their <pass> will be verified and then
each of the remote addresses will be compared against the list
of address regular expressions for a match. Addresses will
always come in the form "<host/ip>:<port>".
--auth, An optional string representing a single user with full
access, in the form of <user:pass>. This is equivalent to creating an
authfile with {"<user:pass>": [""]}.
--proxy, Specifies another HTTP server to proxy requests to when
chisel receives a normal HTTP request. Useful for hiding chisel in
plain sight.
--socks5, Allows client to access the internal SOCKS5 proxy. See
chisel client --help for more information.
--pid Generate pid file in current directory
-v, Enable verbose logging
--help, This help text
Version:
X.Y.Z
Read more:
https://github.com/jpillora/chisel
$ chisel client --help
Usage: chisel client [options] <server> <remote> [remote] [remote] ...
<server> is the URL to the chisel server.
<remote>s are remote connections tunnelled through the server, each of
which come in the form:
<local-host>:<local-port>:<remote-host>:<remote-port>
■ local-host defaults to 0.0.0.0 (all interfaces).
■ local-port defaults to remote-port.
■ remote-port is required*.
■ remote-host defaults to 0.0.0.0 (server localhost).
example remotes
3000
example.com:3000
3000:google.com:80
192.168.0.5:3000:google.com:80
socks
5000:socks
*When the chisel server has --socks5 enabled, remotes can
specify "socks" in place of remote-host and remote-port.
The default local host and port for a "socks" remote is
127.0.0.1:1080. Connections to this remote will terminate
at the server's internal SOCKS5 proxy.
Options:
--fingerprint, A *strongly recommended* fingerprint string
to perform host-key validation against the server's public key.
You may provide just a prefix of the key or the entire string.
Fingerprint mismatches will close the connection.
--auth, An optional username and password (client authentication)
in the form: "<user>:<pass>". These credentials are compared to
the credentials inside the server's --authfile. defaults to the
AUTH environment variable.
--keepalive, An optional keepalive interval. Since the underlying
transport is HTTP, in many instances we'll be traversing through
proxies, often these proxies will close idle connections. You must
specify a time with a unit, for example '30s' or '2m'. Defaults
to '0s' (disabled).
--proxy, An optional HTTP CONNECT proxy which will be used reach
the chisel server. Authentication can be specified inside the URL.
For example, http://admin:password@my-server.com:8081
--pid Generate pid file in current directory
-v, Enable verbose logging
--help, This help text
Version:
X.Y.Z
Read more:
https://github.com/jpillora/chisel
More…
Copyright © 2017 Jaime Pillora <dev@jpillora.com>
Source: https://github.com/jpillora/