Codecepticon
Codecepticon is a .NET application that allows you to obfuscate C#, VBA/VB6 (macros), and PowerShell source code, and is developed for offensive security engagements such as Red/Purple Teams. What separates Codecepticon from other obfuscators is that it targets the source code rather than the compiled executables, and was developed specifically for AV/EDR evasion.
Codecepticon allows you to obfuscate and rewrite code, but also provides features such as rewriting the command line as well.
Using Codecepticon
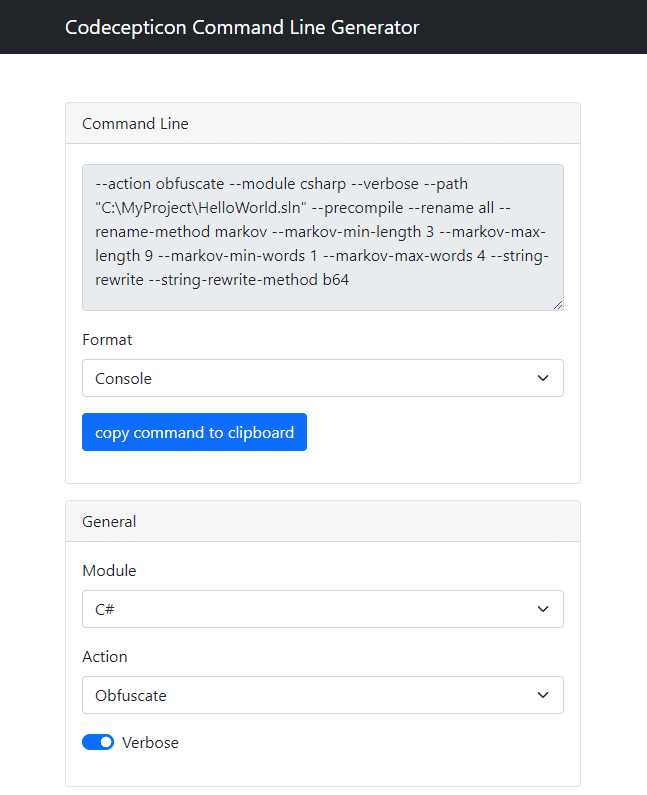
There are two ways to use Codecepticon, either by putting all arguments in the command line or by passing a single XML configuration file. Due to the high level of supported customisations, It’s not recommended manually go through –help output to try and figure out which parameters to use and how. Use CommandLineGenerator.html and generate your command quickly:
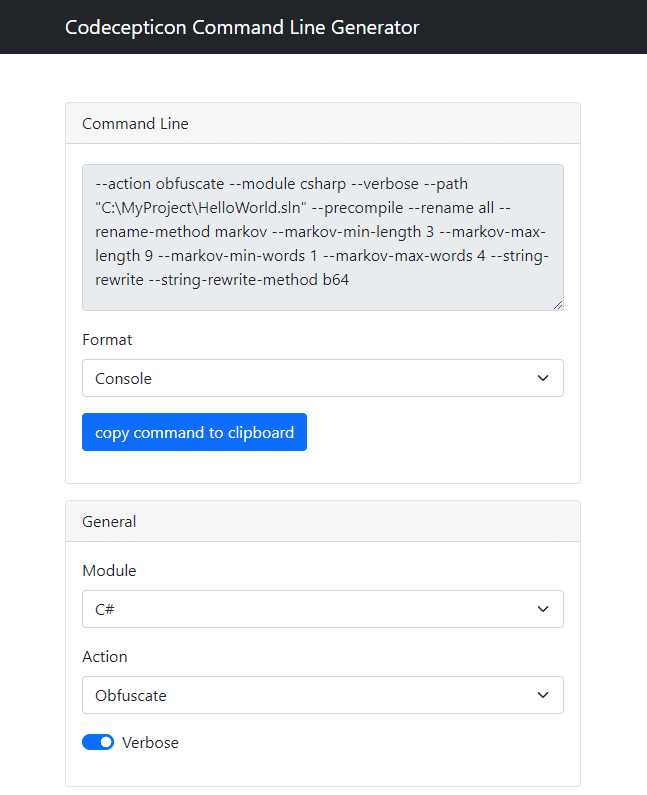
The command generator’s output format can be either Console or XML, depending on what you prefer. Console commands can be executed as:
Codecepticon.exe –action obfuscate –module csharp –verbose …etc
While when using an XML config file, as:
Codecepticon.exe –config C:\Your\Path\To\The\File.xml
If you want to deep dive into Codecepticon’s functionality, check out this document.
For tips you can use, check out this document.
C#
Obfuscating a C# project is simple, simply select the solution you wish to target. Note that a backup of the solution itself will not be taken, and the current one will be the one that will be obfuscated. Make sure that you can independently compile the target project before trying to run Codecepticon against it.
VBA/VB6
The VBA obfuscation works against the source code itself rather than a Microsoft Office document. This means that you cannot pass a doc(x) or xls(x) file to Codecepticon. It will have to be the source code of the module itself (press Alt-F11 and copy the code from there).
PowerShell
Due to the complexity of PowerShell scripts, along with the freedom it provides in how to write scripts it is challenging to cover all edge cases and ensure that the obfuscated result will be fully functional. Although it’s expected for Codecepticon to work fine against simple scripts/functionality, running it against complex ones such as PowerView will not work – this is a work in progress.
Obfuscating Command Line Arguments
After obfuscating an application or a script, it is very likely that the command line arguments have also been renamed. The solution to this is to use the HTML mapping file to find what the new names are. For example, let’s convert the following command line:
SharpHound.exe –CollectionMethods DCOnly –OutputDirectory C:\temp\
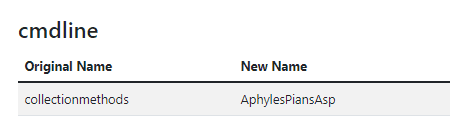
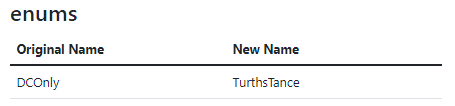
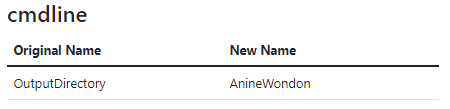
By searching through the HTML mapping file for each argument, we get:
And by replacing all strings the result is:
ObfuscatedSharpHound.exe –AphylesPiansAsp TurthsTance –AnineWondon C:\temp\
However, some values may exist in more than one category:
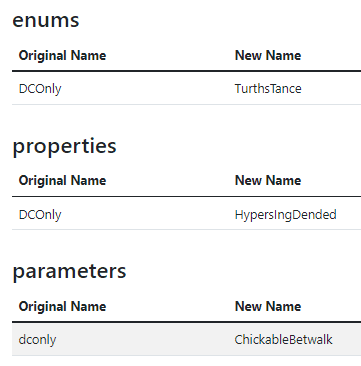
Therefore it is critical to always test your result in a local environment first.
Changelog v1.2.2
[Update]RemovedBouncyCastledependency, now certificates are generated using native .NET functionality.
Install
Copyright (c) 2022 Accenture Security