crackle: Crack and decrypt BLE encryption
crackle cracks BLE Encryption (AKA Bluetooth Smart)

It exploits a flaw in the BLE pairing process that allows an attacker to guess or very quickly brute force the TK (Temporary Key). With the TK and other data collected from the pairing process, the STK (Short Term Key) and later the LTK (Long Term Key) can be collected.
With the STK and LTK, all communications between the master and the slave can be decrypted.
Modes of Operation
crackle has two major modes of operation: Crack TK and Decrypt with LTK.
Crack TK
This is the default mode used when providing crackle with an input file using -i.
In Crack TK mode, crackle brute forces the TK used during a BLE pairing event. crackle exploits the fact that the TK in Just Works(tm) and a 6-digit PIN is a value in the range [0,999999] padded to 128 bits.
crackle employs several methods to perform this brute force: a very fast method if all pairing packets are present in the input file, and a slow method if a minimum set of packets is present.
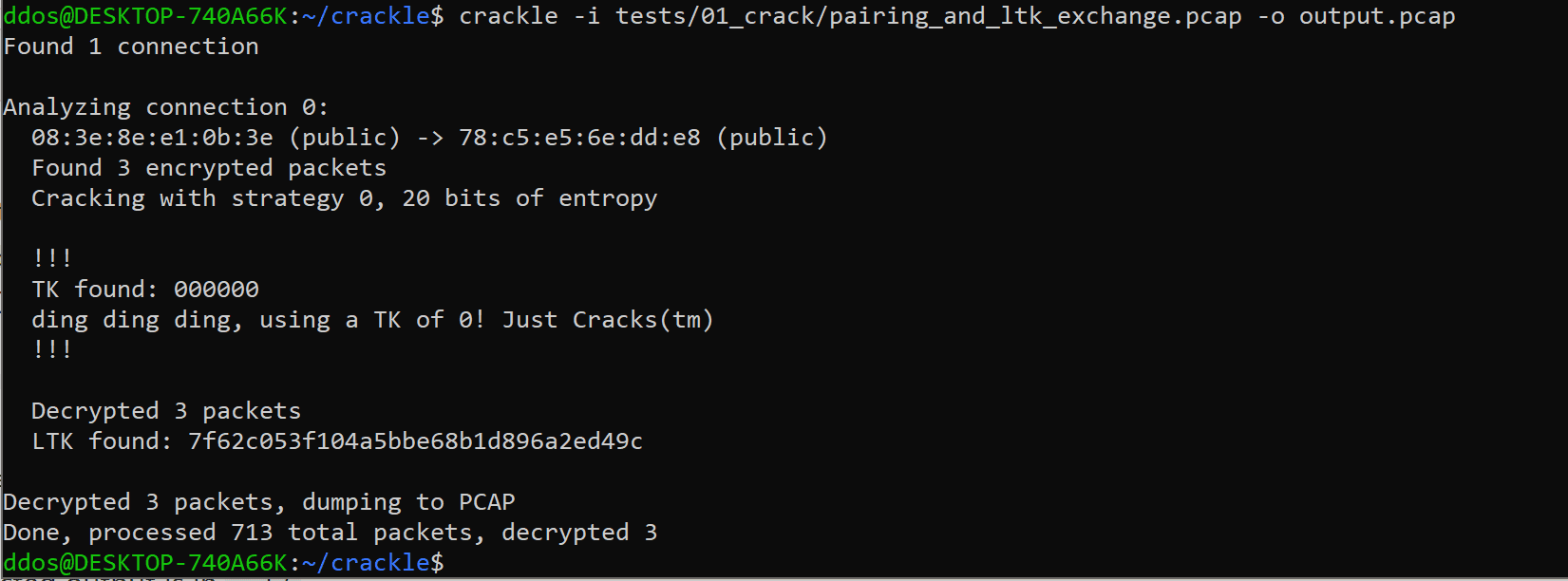
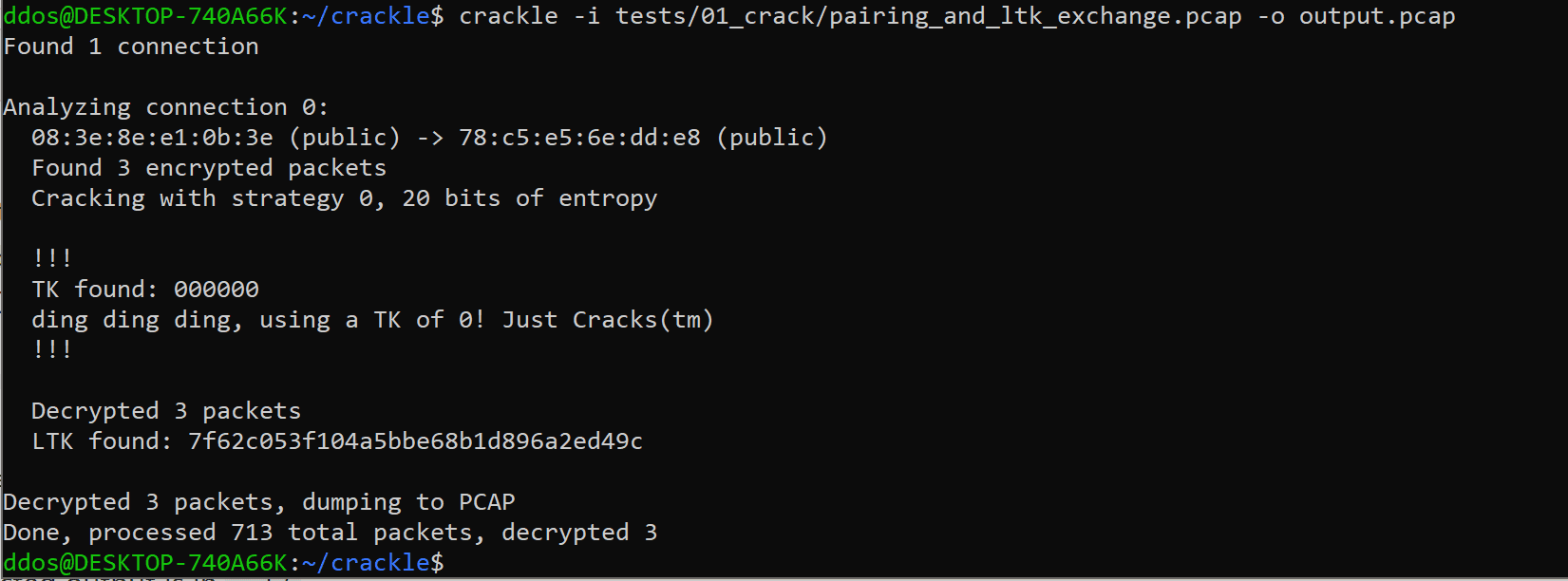
To use this mode, launch crackle with an input PCAP or PcapNG file containing one or more connections with a BLE pairing conversation. crackle will analyze all connections, determine whether it is possible to crack a given connection, and automatically choose the best strategy to crack each one.
If the TK successfully cracks, crackle will derive the remaining keys used to encrypt the rest of the connection and will decrypt any encrypted packets that follow. If the LTK is exchanged (typically the first thing done after encryption is established) crackle will output this value to stdout. The LTK can be used to decrypt any future communications between the two endpoints.
Provide crackle with an output file using -o to create a new PCAP file containing the decrypted data (in addition to the already unencrypted data).
Example usage:
$ crackle -i input.pcap -o decrypted.pcap
Decrypt with LTK
In Decrypt with LTK mode, crackle uses a user-supplied LTK to decrypt communications between a master and slave. This mode is identical to the decryption portion of Crack TK mode.
Example usage:
$ crackle -i encrypted.pcap -o decrypted.pcap -l 81b06facd90fe7a6e9bbd9cee59736a7
Download && Tutorial
Copyright (c) 2013-2018, Mike Ryan
All rights reserved.





