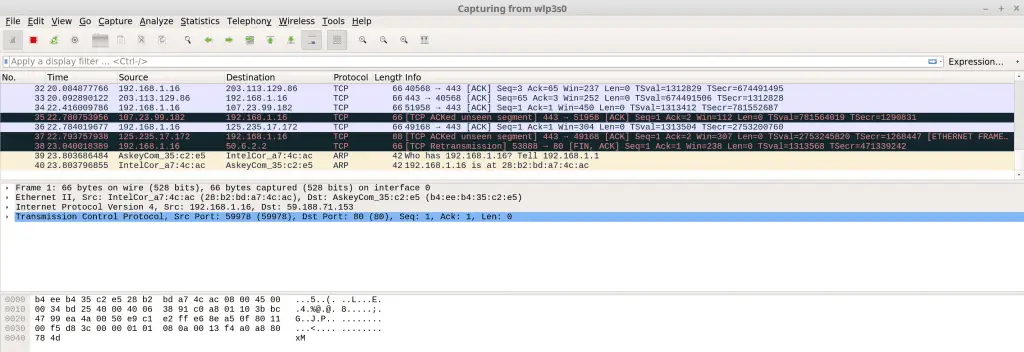
Wireshark Analyzer v4.2.2 released: open-source network protocol analyzer
Wireshark Analyzer is a fantastic multi-platform open-source network protocol analyzer. It can be used to check the analysis of data from the network host to survive, but also look to capture files from the disk. You can interactively browse the capture data, just capture details of the package, you need to analyze. Wireshark has some powerful features, including the ability to rich display filter language and view the reconstructed stream of a TCP session. It also supports hundreds of protocols and media types. It includes a similar tcpdump named tshark the console version. Note that Wireshark emergence of a few dozens of remotely exploitable vulnerabilities, and thus needs to be updated to the latest version, and do not run in an insecure network environment.
Changelog
Bug Fixes
This release fixes a software update issue on Windows which causes Wireshark to hang if you are upgrading from version 4.2.0 or 4.2.1. If you are experiencing this issue you will need to download and install Wireshark 4.2.2 or later.
The following bugs have been fixed:
- sharkd is not installed by the Windows installer. Issue 19556.
- Fuzz job crash output: fuzz-2024-01-01-7740.pcap. Issue 19558.
- Can’t open a snoop file from the Open dialog box unless I select \”All files\” as the file type. Issue 19565.
- Add s4607 dissector to \”decode as\” Issue 19566.
- Updater for 4.2.1 hangs. Issue 19568.
Updated Protocol Support
RSVP, RTPS, and STANAG 4607






