dcept: deploying & detecting use of Active Directory honeytokens
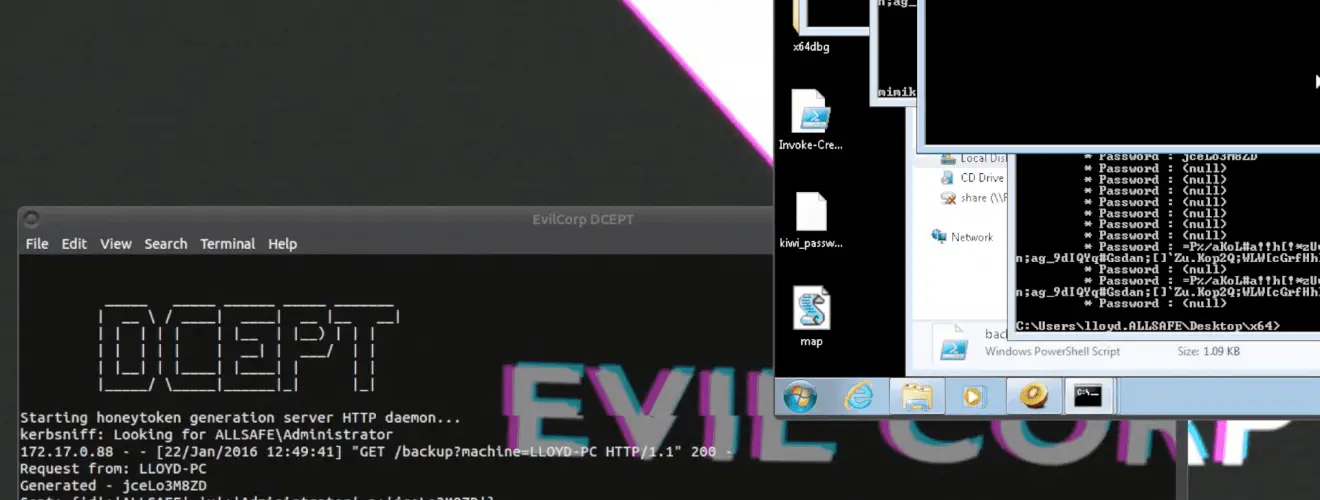
DCEPT (Domain Controller Enticing Password Tripwire) is a honeytoken-based tripwire for Microsoft’s Active Directory. Honeytokens are pieces of information intentionally littered with the system so they can be discovered by an intruder. In the case of DCEPT, the honeytokens are credentials that would only be known by a someone extracting them from memory. A login attempt using these faux credentials would mean someone was on the network and is attempting privilege escalation to the domain administrator.
This proof of concept is being released as open source to benefit Windows system administrators. The goal of this project was to provide a free, simple, honeytoken deployment tool as well as educate administrators about the nature of these attacks. We encourage contributors to build on what we have done and welcome feedback. Has DCEPT helped your organization spot an intrusion before it was too late? We would like to hear from you.
Overview
There are three components to DCEPT. The first is an agent written in C# that caches honeytokens in memory on the endpoints. The tokens themselves are invalid credentials and pose no risk of compromise. Honeytokens are requested at regular intervals and are uniquely associated with a workstation for a particular window of time; therefore providing a forensic timeline. In the event a honeytoken is used on a different workstation at a later date, its point of origin is still known, potentially narrowing the scope of an investigation.
The second is a server component that generates and issues honeytokens to requesting endpoints. Generated tokens are stored in a database along with the timestamp and endpoint that requested it.
A third component acts as a monitor that passively listens for logon attempts. In order to capture the necessary packets, the DCEPT interface needs to be on the same network as the domain controller.
DCEPT Agent
The agent puts honeytoken credentials into memory by calling the CreateProcessWithLogonW Windows API to launch a suspended subprocess with the LOGON_NETCREDENTIALS_ONLY flag. It refreshes this process with a default time period of one day, obtaining new honeytoken credentials from the DCEPT generation server each time.
DCEPT Generation Server
This component generates a randomized honeytoken password for each agent per time period. It logs the credentials, timestamp, and computer name to a database for later retrieval.
DCEPT Sniffer
The sniffer process runs alongside the generation server and looks for Kerberos pre-authentication packets destined for the AD domain controller that match the honeytoken username. Upon receiving one of these packets, DCEPT attempts to brute-force decrypt the contents using all of the honeytoken credentials stored in the database. If a packet is successfully decrypted, then a generated alert reveals the name of the compromised computer the honeytoken password was stolen from and the time period when it happened.






