hackebds
In the process of penetration and vulnerability mining of embedded devices, many problems have been encountered. One is that some devices do not have telnetd or ssh services to obtain an interactive shell. Some devices are protected by a firewall and cannot be connected to it in the forward direction Reverse_shell is required, and the other is that memory corruption vulnerabilities such as stack overflow are usually Null bytes are truncated, so it is more troublesome to construct reverse_shellcode, so this tool was developed to exploit the vulnerability. This tool is developed based on the PWN module and currently uses the python2 language, Has been updated to python3
Function
This tool is embedded in the security test of the device. There are two main functions:
-
Generate backdoor programs of various architectures. The backdoor program is packaged in shellless pure shellcode and is a small, Pure static backdoor. Armv5, Armv7, Armv8, mipsel, mips, mips64, mipsel64, powerpc, powerpc64,sparc, sparc64 are now supported, and they are still being updated
-
Generate reverse_shell shellcode of various architectures during the exploit process, and no null bytes, which facilitates the exploitation of memory corruption vulnerabilities on embedded devices. Armv5, Armv7, Armv8, mipsel, mips, mips64, mipsel64, powerpc, powerpc64, and sparc are now supported, and they are still being updated
-
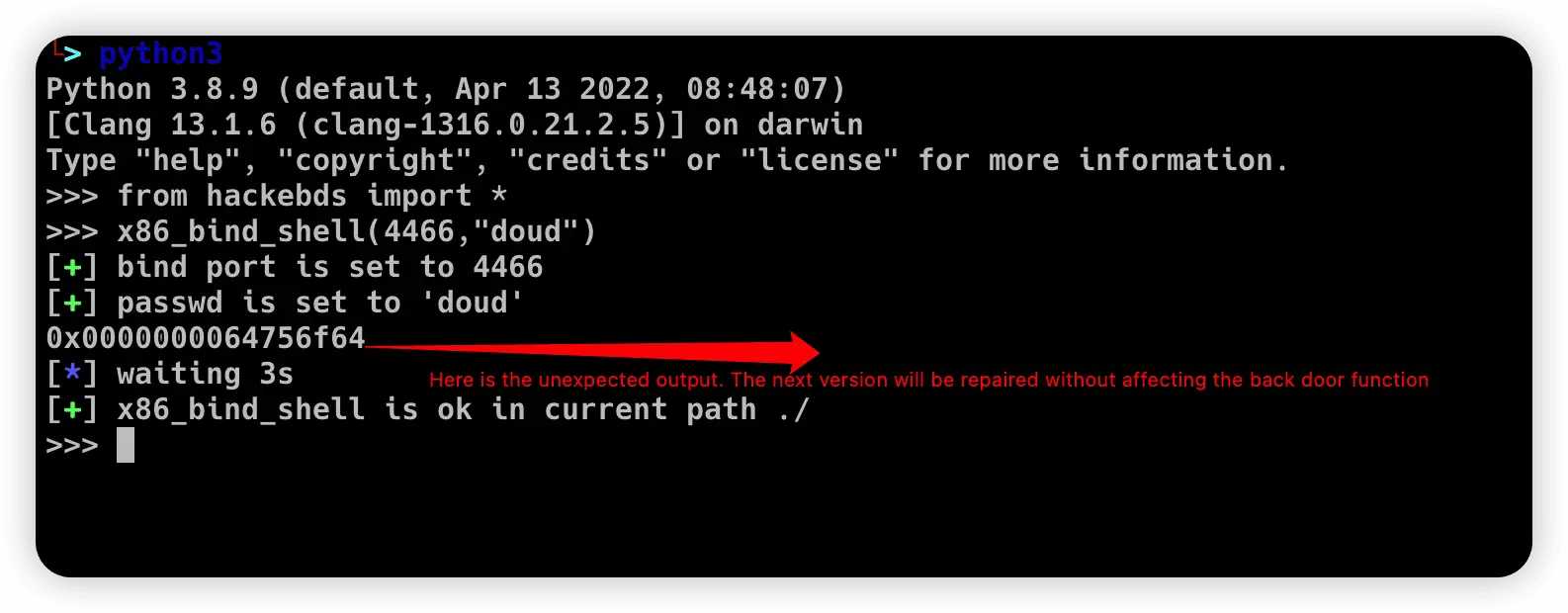
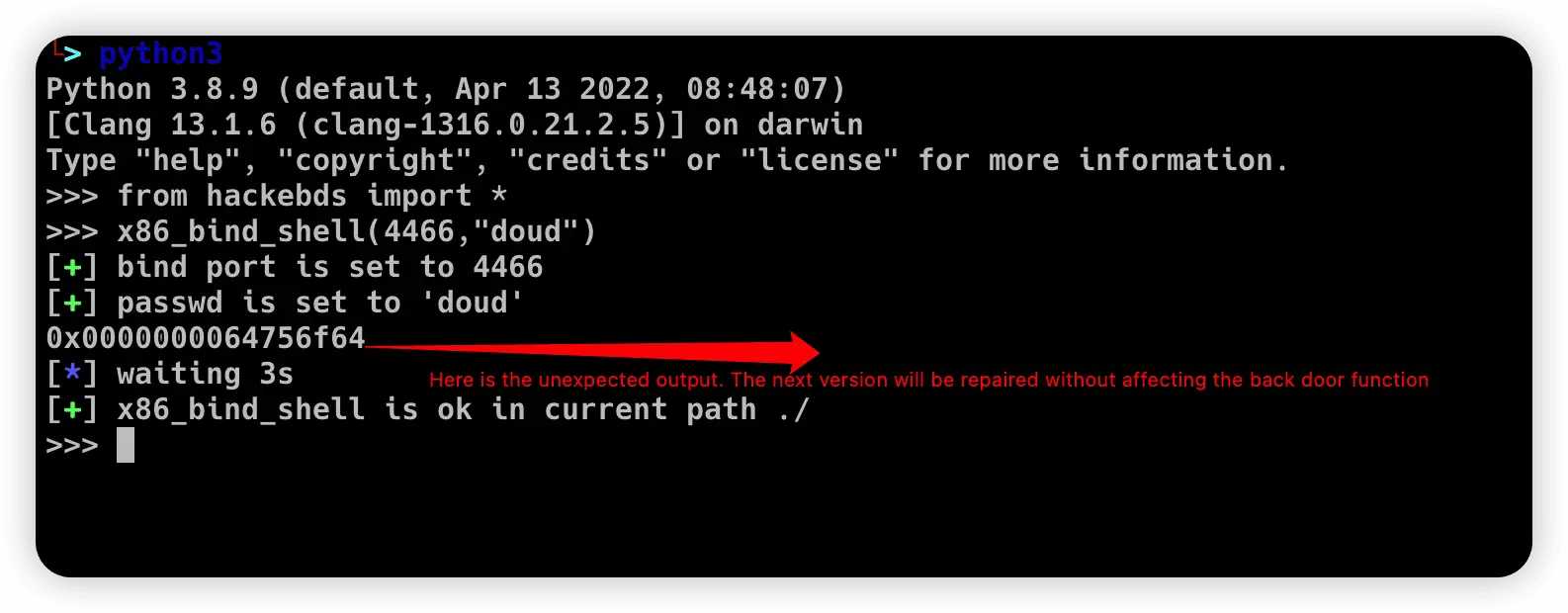
Fixed some bugs that the reverse_shellcode and reverse_backdoor ports were selected too big, and added the function of generating bindshell with specified ports and passwords under x86 and x64, and beautified the generation process**(This feature will be updated to various architectures)** Add support armvelv7_bind_shell(2022.10.27),
-
Removed the generation sleep time of shellcode, and added mips_ bind_ Shell, the reverse of x86 and x64 small end_ shell_ Backdoor, the mips that are expected to be interrupted by mips_ bind_ Shell, which solves the error of password logic processing in the bindshell in mips, Joined aarch64_ bind_ shell
-
Support command line generation backdoor and shell code, Strong anti-hunting ability, characterized by light, small, efficient and fast
-
The learning function of the device model is added. After establishing the relationship between the model and the arch, the target content is generated again. You only need to specify the model
-
CVE retrieval function is added and CVE retrieval is backed up
-
Improved x86, x64, armebv5, reverse_ shellcode and reverse_ shell_ file
-
Improved the file generation process, directory designation, and file replacement
-
Improved support for MacOS systems