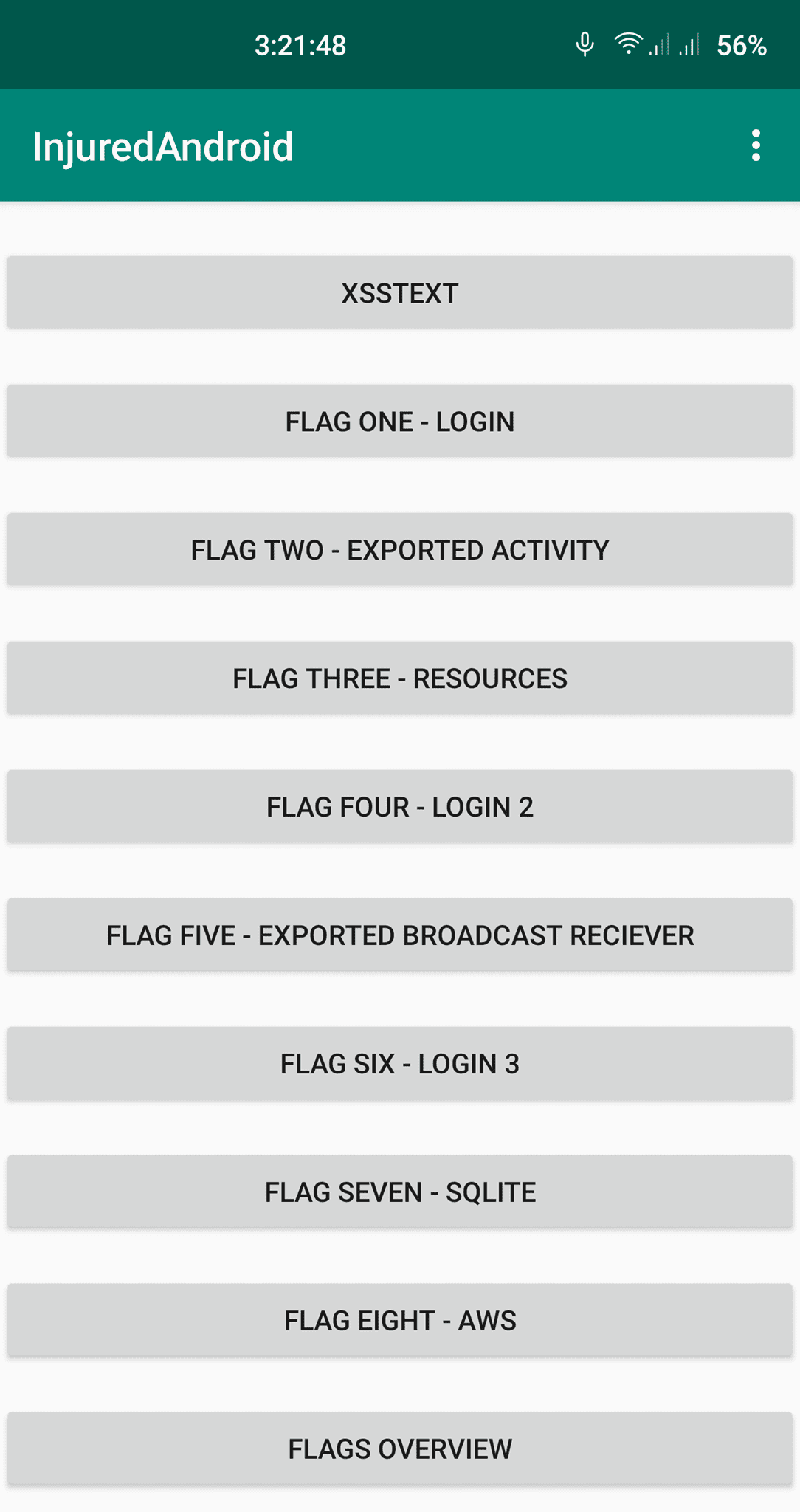
InjuredAndroid – CTF
A vulnerable Android application with ctf examples based on bug bounty findings, exploitation concepts, and pure creativity.
Changelog v1.0.12
- This release includes the missing x86_64 library for the Flutter module.
Setup for a physical device
- Download injuredandroid.apk from Github
- Enable USB debugging on your Android test phone.
- Connect your phone and your pc with a usb cable.
- Install via adb. adb install InjuredAndroid.apk. Note: You need to use the absolute path to the .apk file or be in the same directory.
Setup for an Android Emulator using Android Studio
- Download the apk file.
- Start the emulator from Android Studio (I recommend downloading an emulator with Google APIs so root adb can be enabled).
- Drag and drop the .apk file on the emulator and InjuredAndroid.apk will install.
Tips and CTF Overview
Decompiling the Android app is highly recommended.
- XSSTEST is just for fun and to raise awareness on how WebViews can be made vulnerable to XSS.
- The login flags just need the flag submitted.
- The flags without a submit that demonstrate concepts will automatically register in the “Flags Overview” Activity.
- The last two flags don’t register because there currently isn’t a remote verification method (I plan to change this in a future update). This was done to prevent using previous flag methods to skip the exploitation techniques.
- There is one flag with a Pentesterlab 1 month gift key. The key is stored in a self-destructing note after It’s read, do not close the browser tab before copying the url.
- The exclamatory buttons on the bottom right will give users up to three tips for each flag.
Source: https://github.com/B3nac/