Introduction to Idle/Zombie Scanning
In the penetration testing, information collection is the most important stage, accounting for about 60% of the penetration test. Based on the collected information, we can effectively improve the success rate of our penetration testing. It shows how important efficient information collection is to us. Zombie scanning is the port scanning phase of information gathering. However, the common port scanning process is often found at the network layer, causing the hidden purpose not to be achieved. Zombie scanning can effectively hide its own tracks.
To implement a zombie scan, you must have the following two requirements
- First, there is a qualified zombie machine, a so-called zombie machine, that is free enough and does not host any network communication with any machine other than us, depending largely on the continuity of his IPID (often the mainstream operation System IPID are randomly generated or all 0), will be mentioned later.
- Second: The source IP address can be forged. In some network devices, the firewall limits the forged source address, which leads to the failure of scanning.
Zombie scanning process
First, an SYN/ACK packet is sent from the local scanner to the zombie. Because the packet sent is not a SYN packet, zombie would find it strange that someone would send me an SYN/ACK packet, so zombie Will be the original return of an RST package to interrupt the connection, this time in the RST package will be with zombie’s IPID, assuming IPID = x at this time.
Second, the source IP is then faked by the local scanner (the IP address of the zombie), specifying a port number and sending a SYN packet to the target. After receiving the SYN packet, if the target port is open, it will return an SYN/ACK packet to the source IP.SRC. At this time, the SYN / ACK packet is received by a zombie. At this time, it will return a RST Package, IPID = x + 1 at this time. If the port is not open, the target will directly return an RST package to a zombie, the zombie does not respond, IPID = x.
Finally, the local host (scanner) to send an SYN/ACK package to a zombie, the same steps as the first step, zombie returns an RST package, but this time the IPID and the first step is different, we pass IPID difference The value of the judge target port is open. If the IPID = x + 1 at this time the second step zombie did not send any packet, so we can see the target port is closed; if IPID = x + 2 the second step zombie sent a RST packet, we can see that the target port is open.
Zombie scanning Example
Before introducing nmap I have a question you want to explore is that since there nmap these invincible powerful scanning tools exist, then why do we have to write their own script? Here is just my personal understanding, do not like do not spray, I think the tool is actually just to make it easier for us to do something that you want to do, perhaps directly call a tool and then add one or two parameter options can exceed us dozens Hundreds of script, but also better to complete the task, but to understand the principle of tool work is more important too!
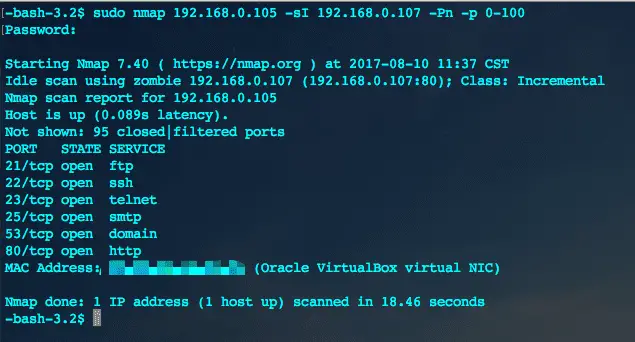
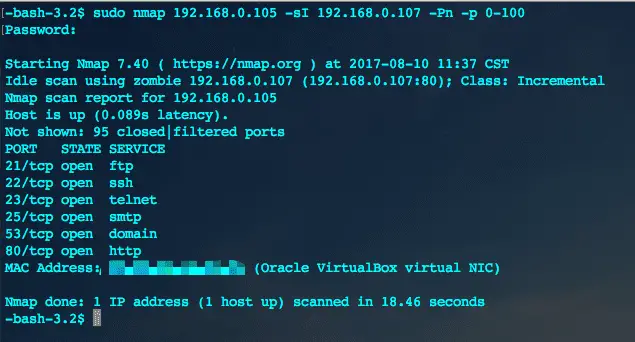
- Nmap found zombie machine
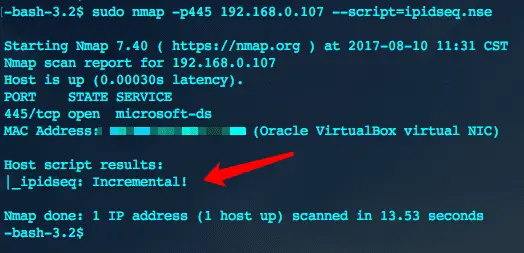
- Nmap uses zombie machine for port scanning