JVMXRay
JVMXRay is a technology for monitoring access to system resources within the Java Virtual Machine. It’s designed with application security emphasis but some will also find it beneficial for software quality processes and diagnostics.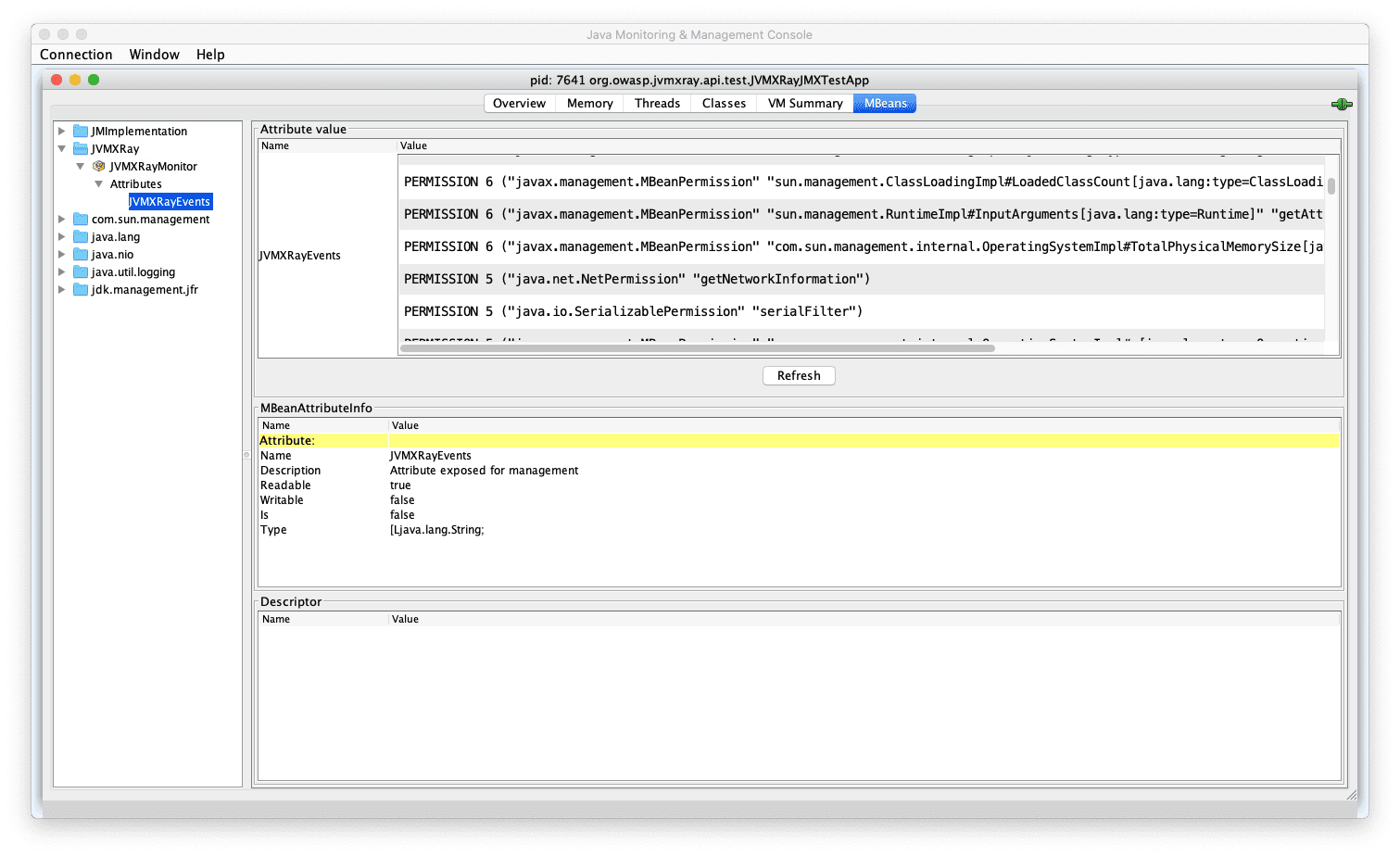
Benefits
Following is a quick list of some of the more important benefits.
Identify protected resources
Track different types of events of interest related to sockets, files, process execution, and more. When an event of interest occurs, process it as you wish. At the moment, adaptors for the system console (e.g., System.out), logback, and Java Logging are available with others in the process.
No code changes required
JVMXRay does not require any changes to your application source code to work. The code is pulled into the JVM by a command-line option. The solution is 100% Java code so it runs anywhere.
Supply chain insights
An ancillary benefit of not requiring source code is that JVMXRay provides insight into your application dependencies including 3rd party libraries (e.g. Jar files). Events provide the source of origin where your classes where loaded when the event is generated.
Extensible & Open
Don’t see an adapter or filter that works for you and know how to code? Roll up your sleeves and write one. It’s extensible. Fix a bug and submit a pull request. All the source code is available.
Audience
The anticipated audience for JVMXRay is two-fold,
Systems Administrators Individuals charged with system security and interested in new methods to gather security intelligence into Java applications.
Security Developers & Architects Individuals interested in improved security intelligence about their applications.
How it Works
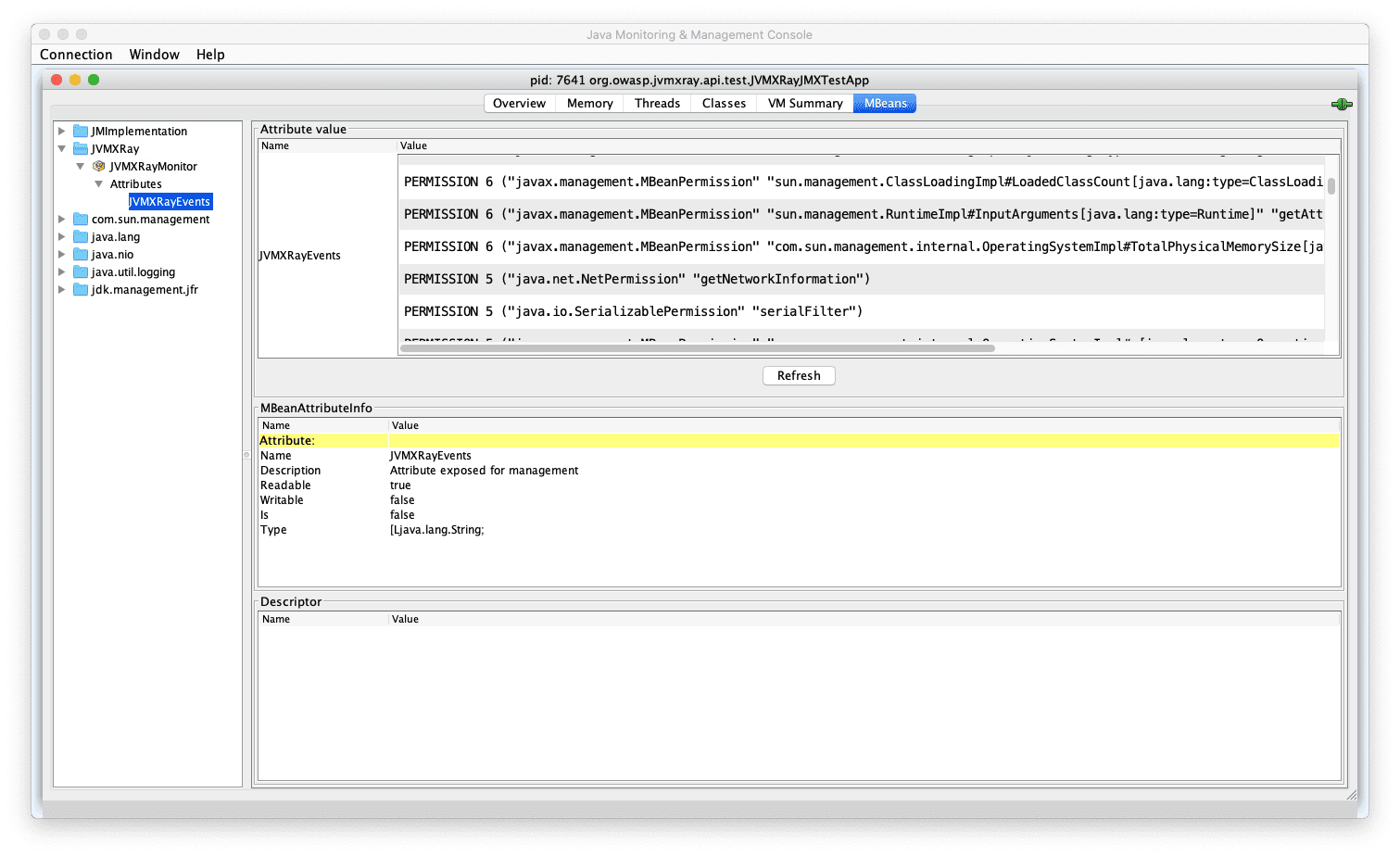
The Java Virtual Machine provides a robust security framework for controlling access to protected resources. JVMXRay provides an implementation of the java.lang.SecurityManager component, called NullSecurityManager. Ironically, the NullSecurityManager provides no policy enforcement but instead monitors activities to protected resources. It’s expected other cloud log processing tools, big data tools, or cloud security tools will process these events into meaningful contextual information.
Changelog v0.0.6
- Establish architecture baseline for old code.
Download
Demo
Copyright (C) 2020 Milton Smith & John Melton