k0otkit: universal post-penetration technique in penetrations against Kubernetes clusters
k0otkit – Manipulate K8s in a K8s way
k0otkit is a universal post-penetration technique which could be used in penetrations against Kubernetes clusters.
With k0otkit, you can manipulate all the nodes in the target Kubernetes cluster in a rapid, covert, and continuous way (reverse shell).
k0otkit is the combination of Kubernetes and rootkit.
Prerequisite:
k0otkit is a post-penetration tool, so you have to first conquer a cluster, somehow manage to escape from the container, and get the root privilege of the master node (to be exact, you should get the admin privilege of the target Kubernetes).
Scenario:
- After Web penetration, you get a shell of the target.
- If necessary, you manage to escalate the privilege and make it.
- You find the target environment is a container (Pod) in a Kubernetes cluster.
- You manage to escape from the container and make it (with CVE-2016-5195, CVE-2019-5736, docker.sock or other techniques).
- You get a root shell of the master node and are able to instruct the cluster with kubectl on the master node as admin.
- Now you want to control all the nodes in the cluster as quickly as possible. Here comes k0otkit!
Features
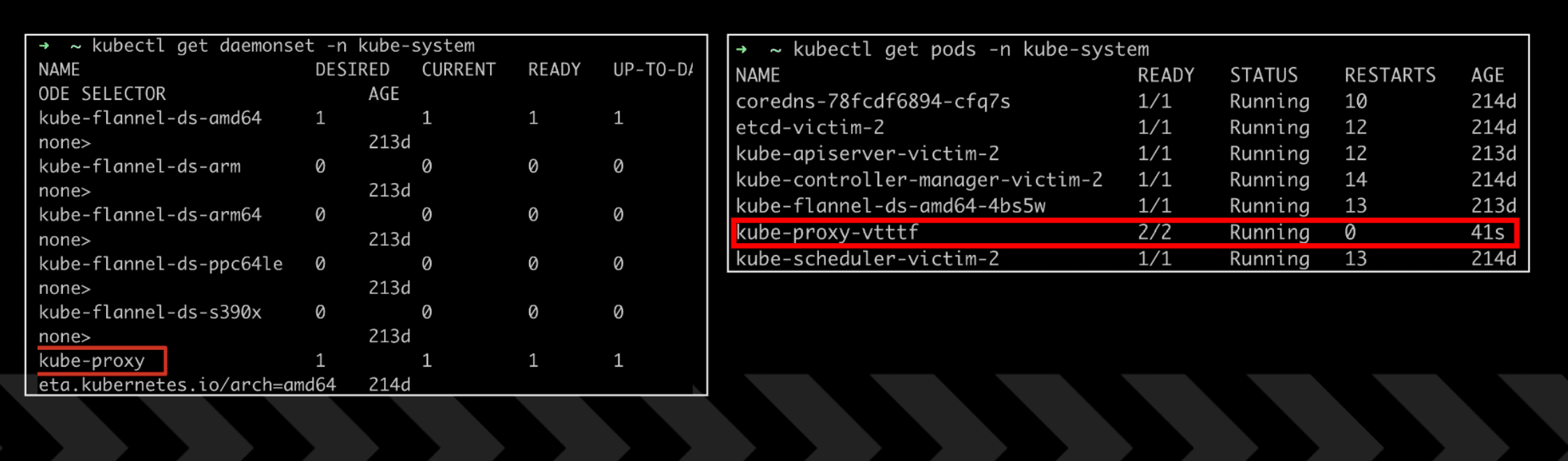
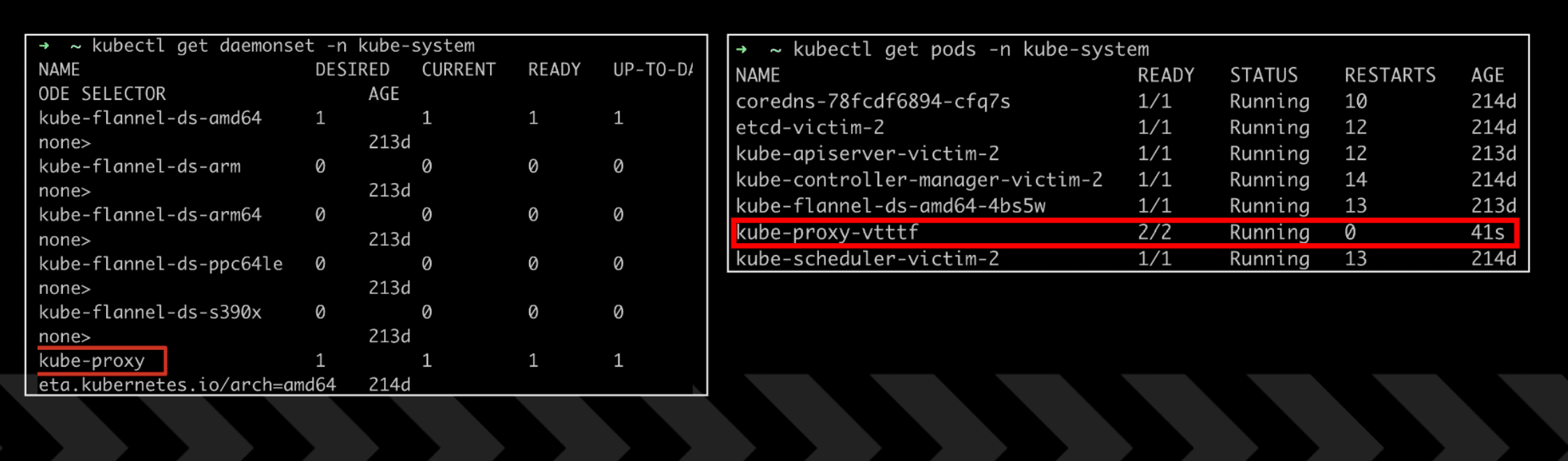
- utilize K8s resources and features (hack K8s in a K8s way)
- dynamic container injection
- communication encryption (thanks to Meterpreter)
- fileless





