Loki v0.51 released – Simple IOC and Incident Response Scanner
Loki – Simple IOC Scanner
Scanner for Simple Indicators of Compromise
Detection is based on four detection methods:
- File Name IOC
Regex match on full file path/name - Yara Rule Check
Yara signature match on file data and process memory - Hash check
Compares known malicious hashes (MD5, SHA1, SHA256) with scanned files - C2 Back Connect Check
Compares process connection endpoints with C2 IOCs (new since version v.10)
Additional Checks:
- Regin filesystem check (via –reginfs)
- Process anomaly check (based on Sysforensics)
- SWF decompressed scan (new since version v0.8)
- SAM dump check
- DoublePulsar check – tries to detect DoublePulsar backdoor on port 445/tcp and 3389/tcp
- PE-Sieve process check
The Windows binary is compiled with PyInstaller 2.1 and should run as an x86 application on both x86 and x64 based systems.
Changelog v0.51
- PE-Sieve upgraded to fixed version 0.3.6
How-To Run LOKI and Analyse the Reports
Run
- Download the latest LOKI version from the releases section
- Run it once to retrieve the latest signature base repository
- Provide the folder to a target system that should be scanned: removable media, network share, folder on target system
- Right-click on loki.exe and select “Run as Administrator” or open a command line “cmd.exe” as Administrator and run it from there (you can also run LOKI without administrative privileges but some checks will be disabled and relevant objects on disk will not be accessible)
Reports
- The resulting report will show a GREEN, YELLOW or RED result line.
- Please analyze the findings yourself by:
- uploading non-confidential samples to Virustotal.com
- Search the web for the filename
- Search the web for keywords from the rule name (e.g. EQUATIONGroupMalware_1 > search for “Equation Group”)
- Search the web for the MD5 hash of the sample
- Search in my customer APT search engine for file names or identifiers
- Please report back false positives via the Issues section (mention the false positive indicator like a hash and/or filename and the rule name that triggered)
Update
Since version 0.21.0 LOKI includes a separate updater tool named loki-upgrader.exe or loki-upgrader.py.
It allows updating the compiled loki.exe for Windows and the signature-based sources.
When running loki.exe –update it will create a new upgrade process and exits LOKI in order to replace the loki.exe with the newer one, which would be locked otherwise.
Usage
Scan
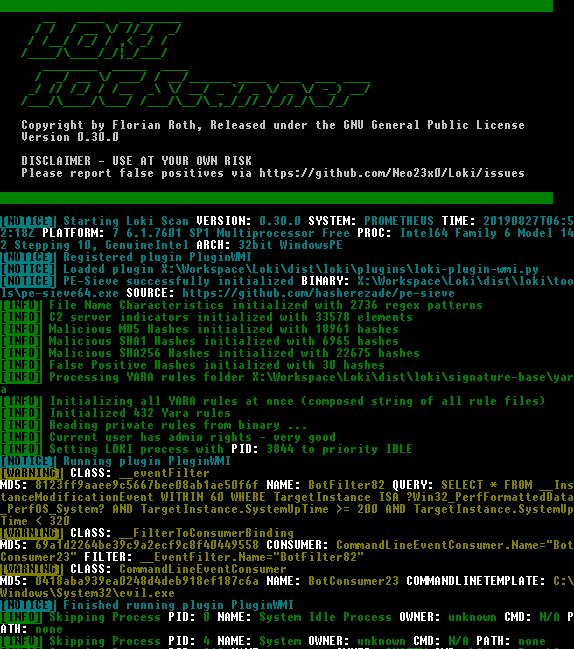
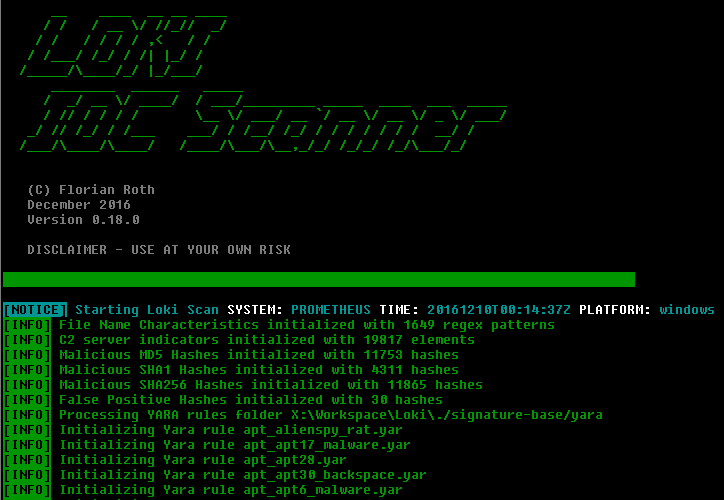
Command Line Scan Output
Hash-based IOCs
File Name based IOCs
Generated log file
Copyright (c) 2015 Florian Roth
Source: https://github.com/Neo23x0/