Macro Pack v2.2 releases: automatize obfuscation & generation of MS Office documents
Macro Pack
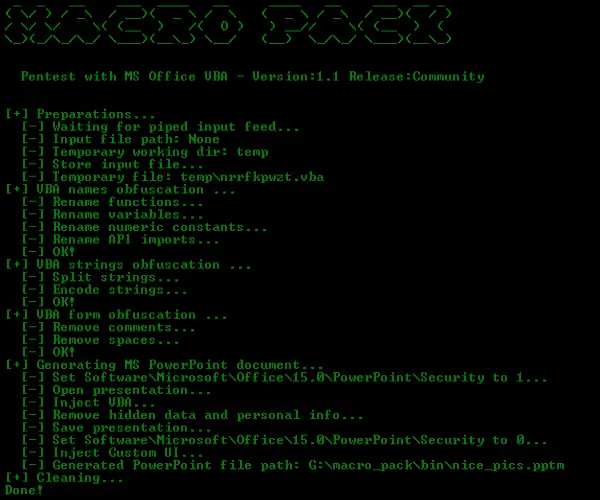
The macro_pack is a tool used to automatize obfuscation and generation of MS Office documents for pentest, demo, and social engineering assessments. The goal of macro_pack is to simplify antimalware solutions bypass and automatize the process from vba generation to final Office document generation.
It is very simple to use:
- No configuration
- Everything can be done using a single line of code
- Generation of Word, Excel, and PowerPoint documents
- Advanced VBA macro attacks as well as DDE attacks
The tool is compatible with payloads generated by popular pentest tools (Metasploit, Empire, …). It is also easy to combine with other tools as it is possible to read input from stdin and have a quiet output to another tool. This tool is written in Python3 and works on both Linux and Windows platform.
Note: Windows platform with genuine MS Office installed is required for Office documents automatic generation or trojan features.

Obfuscation
The tool will use various obfuscation techniques, all automatic. Basic obfuscation (-o option) includes:
- Renaming functions
- Renaming variables
- Removing spaces
- Removing comments
- Encoding Strings
Note that the main goal of macro_pack obfuscation is not to prevent reverse engineering, it is to prevent antivirus detection.
Generation
Macro Pack can generate several kinds of MS office documents and txt formats. The format will be automatically guessed depending on the given file extension. File generation is done using the option –generate or -G.
Supported formats are:
- MS Word 97 (.doc)
- MS Word (.docm, .docx)
- MS Excel 97 (.xls)
- MS Excel (.xlsm)
- MS PowerPoint (.pptm)
- VBA text file (.vba)
Ethical use
The macro pack tool shall only be used by pentester, security researchers, or other people with learning purpose. I condemn all use of security tools for unethical actions (whether these are legal or illegal). I know this will not prevent usage by malicious people and that is why all features are not publicly released.
About pro mode…
You may notice that not all part of macro_pack is available. Only the community version is available online. I fear the features in the pro version are really too much “weaponizing” the process and I do not want it available to all script kiddies out there. The pro mode includes features such as:
- Advance antimalware bypass
- VBOM security bypass
- Self-decoding VBA
- MS Office persistence
- Trojan existing MS Office documents
- Anti-debug using http://seclists.org/fulldisclosure/2017/Mar/90
Changelog v2.2
- Several bug corrections and improvements.
- Mainly concerning obfuscation.
Run/Install
Run Windows binary
- Get the latest binary from https://github.com/sevagas/macro_pack/releases/
- Download binary on PC with genuine Microsoft Office installed.
- Open a console, CD to binary dir and call the binary, simple as that!
macro_pack.exe –help
Install from sources
Download and install dependencies:
git clone https://github.com/sevagas/macro_pack.git
cd macro_pack
pip3 install -r requirements.txt
Note: For windows, you also need to download manually pywin32 from https://sourceforge.net/projects/pywin32/files/pywin32/
The tool is in python 3 so just start with your python3 install. ex:
python3 macro_pack.py –help
# or
python macro_pack.py –help # if python3 is default install
If you want to produce a standalone exe using pyinstaller, double-click on the “build.bat” script on a Windows machine. The resulted macro_pack.exe will be inside the bin directory.
Tutorial
Copyright 2017,2018 Emeric “Sio” Nasi (blog.sevagas.com)
Source: https://github.com/sevagas/





