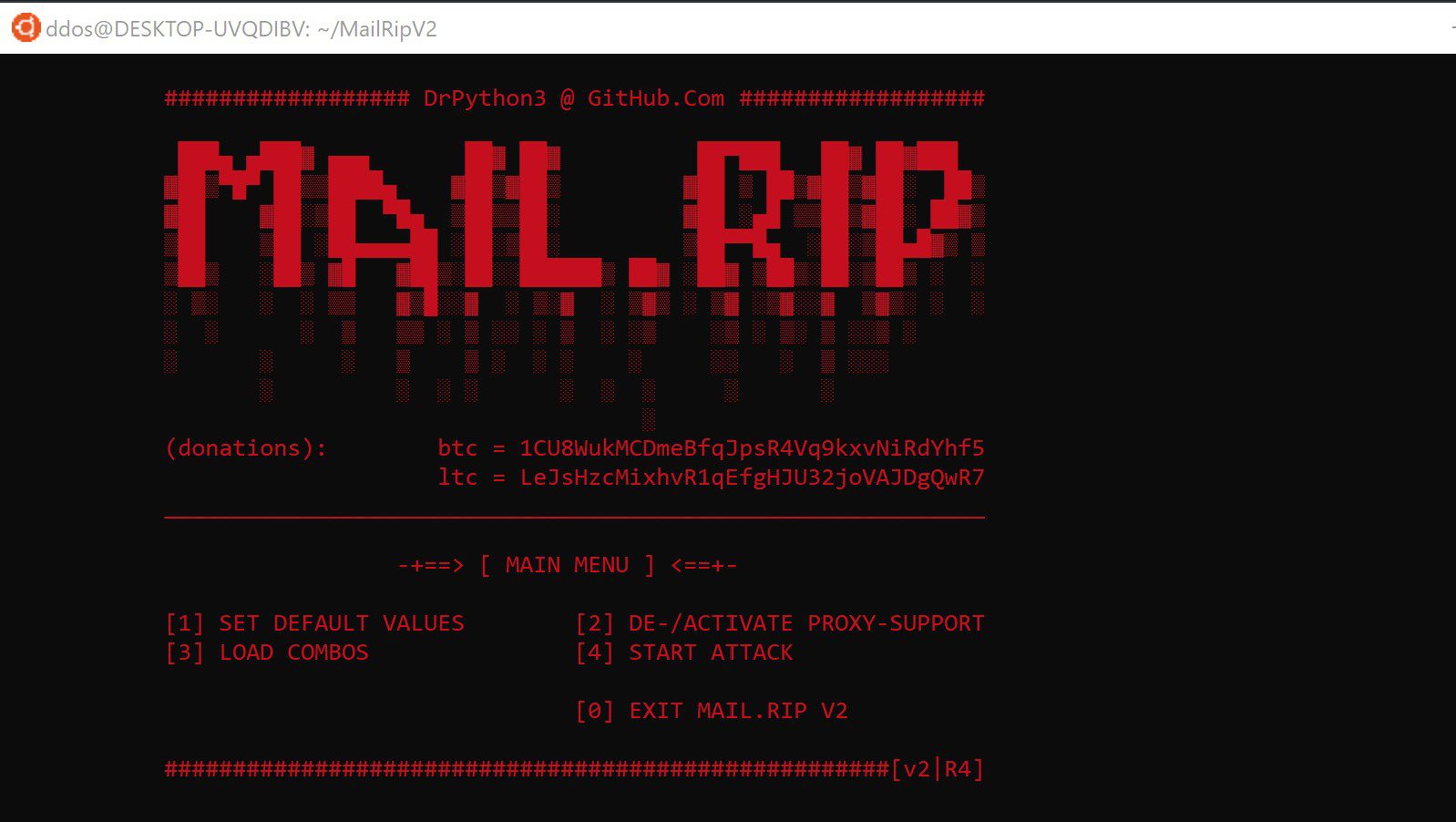
MailRipV2: SMTP checker / SMTP cracker

Mail.Rip v2
Your SMTP checker / SMTP cracker for mailpass combolists including features like proxy-support (SOCKS4 / SOCKS5) with automatic proxy-scraper, e-mail delivery test for valid combos (inbox check), and DNS lookup for unknown SMTP-hosts.
Features
Mail.Rip v2 is an SMTP checker / SMTP cracker written in Python 3.8. Using the “smtplib”, allows you to check common mailpass combolists for valid SMTP logins. It has included dictionaries and lists containing server details of common e-mail providers as well as most common subdomains and ports used for SMTP servers. Besides that, “dnspython” is used to lookup unknown SMTP hosts in MX records. In case it fails, the cracker/checker will try to find the target-server by using the most common subdomains and ports in a connection-test by trial and error.
Moreover, Mail.Rip v2 comes with SOCKS-proxy support and a proxy-scraper function. If the proxy-support is activated, the checker/cracker scrapes SOCKS4 or SOCKS5 proxies from common online sources. The scraped proxies will be used randomly. And you can add new sources by editing the library.json.
Last but not least, Mail.Rip v2 includes an e-mail delivery test for found SMTP logins. For every valid combo, it tries to send a plain text e-mail with the found SMTP login. All text messages are sent to your user-defined receiving address. This way, the cracker/checker provides easy verification of so-called “hits” together with an inbox test.
SMTP cracking / SMTP checking process
Mail.Rip v2 uses the smtplib for the checking / cracking process. The “magic” is done this way:
- The SMTP cracker / SMTP checker reads the next combo from the list loaded before.
- It looks up the e-mail domain in the “smtphost” dictionary for the SMTP-host to attack.
- For unknown hosts, it will try to get from the MX records of the e-mail domain.
- If still no host is found, it trys to establish a connection to guessed hosts using most common subdomains one by one.
- Same for the connection port.
- Afterwards it establishes a connection to the SMTP host (trying SSL first and non-SSL on errors as well as TLS)
- and sends the login data using the target e-mail address and the given password the combo contained.
- If the login is denied, the cracker / checker will try to login with the user-ID (e-mail without @…) and the password.
- In case the login data is valid, the so-called “hit” will be saved to a txt-file.
- In the end Mail.Rip v2 will try to send a test message using the found SMTP.
For best results, every user should edit the host information in the library.json before starting Mail.Rip v2 for the first time. Adding the data of the most common e-mail providers in a combolist will always speed up the checking / cracking process. And it will raise fewer security flags on the server-side.
Install
git clone https://github.com/DrPython3/MailRipV2.git
cd MailRipV2
pip3 install -r requirements.txt