manticore v0.3.7 releases: Dynamic binary analysis tool
Manticore is a prototyping tool for dynamic binary analysis, with support for symbolic execution, taint analysis, and binary instrumentation.
Features
- Input Generation: automatically generates inputs that trigger unique code paths
- Crash Discovery: discovers inputs that crash programs via memory safety violations
- Execution Tracing: records an instruction-level trace of execution for each generated input
- Programmatic Interface: exposes programmatic access to its analysis engine via a Python API
Manticore supports binaries of the following formats, operating systems, and architectures. It has been primarily used on binaries compiled from C and C++. Examples of practical manticore usage are also on github.
- OS/Formats: Linux ELF, Windows Minidump
- Architectures: x86, x86_64, ARMv7 (partial)
Changelog
v0.3.7
Ethereum
- Use
crytic-compile0.2.2 #2530- Multi-transaction analysis now uses fixed attacker and owner contracts #2464
Native
- [Added API] Retrieve list of unimplemented syscalls #2491
- Add
FXSAVE/FXRSTORconcrete support on x86 #2511- Add
last_executed_pcproperty to CPU #2475- Support LD_LIBRARY_PATH #2476
- Optional
will/did_read_memoryevents #2488- Fixed base address handling on Linux #2500
- Add
ENDBR-style NOPs #2533- Support
epoll-related syscalls #2529Other
- [Added API] Add fork policy for providing explicit values #2514
- Fixed Constant Folding #2524
- Add simplifications for subtraction #2504
- Parent state ID, last PC now available in state descriptors #2479, #2471
- States now contain a reference to the current manticore instance #2486
fast_failconfig to exit after first state exception #2487- Scaling bugfix for large solver queries #2502
- Don’t fork when only one solution is found for
Concretize#2527
Installation
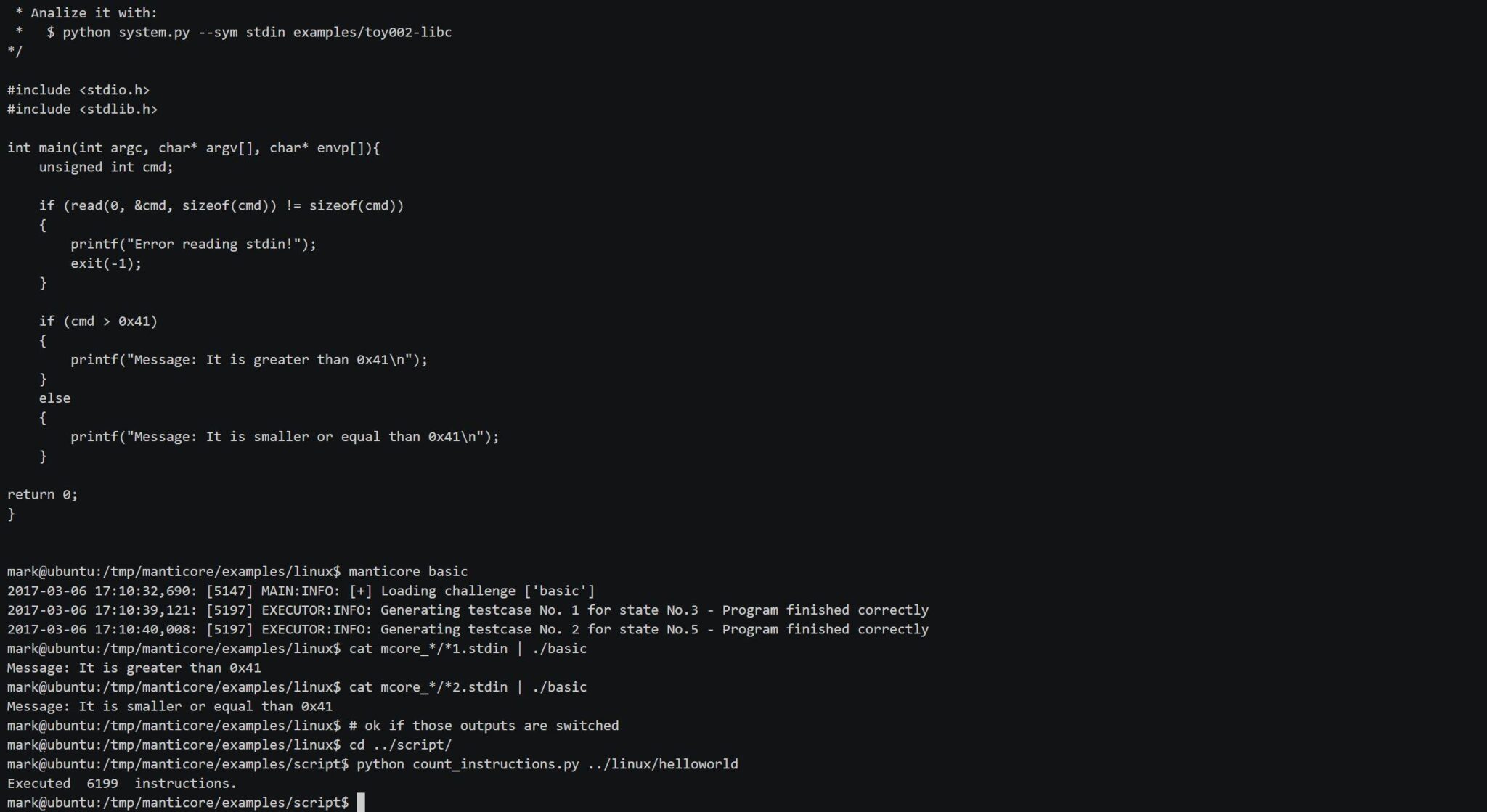
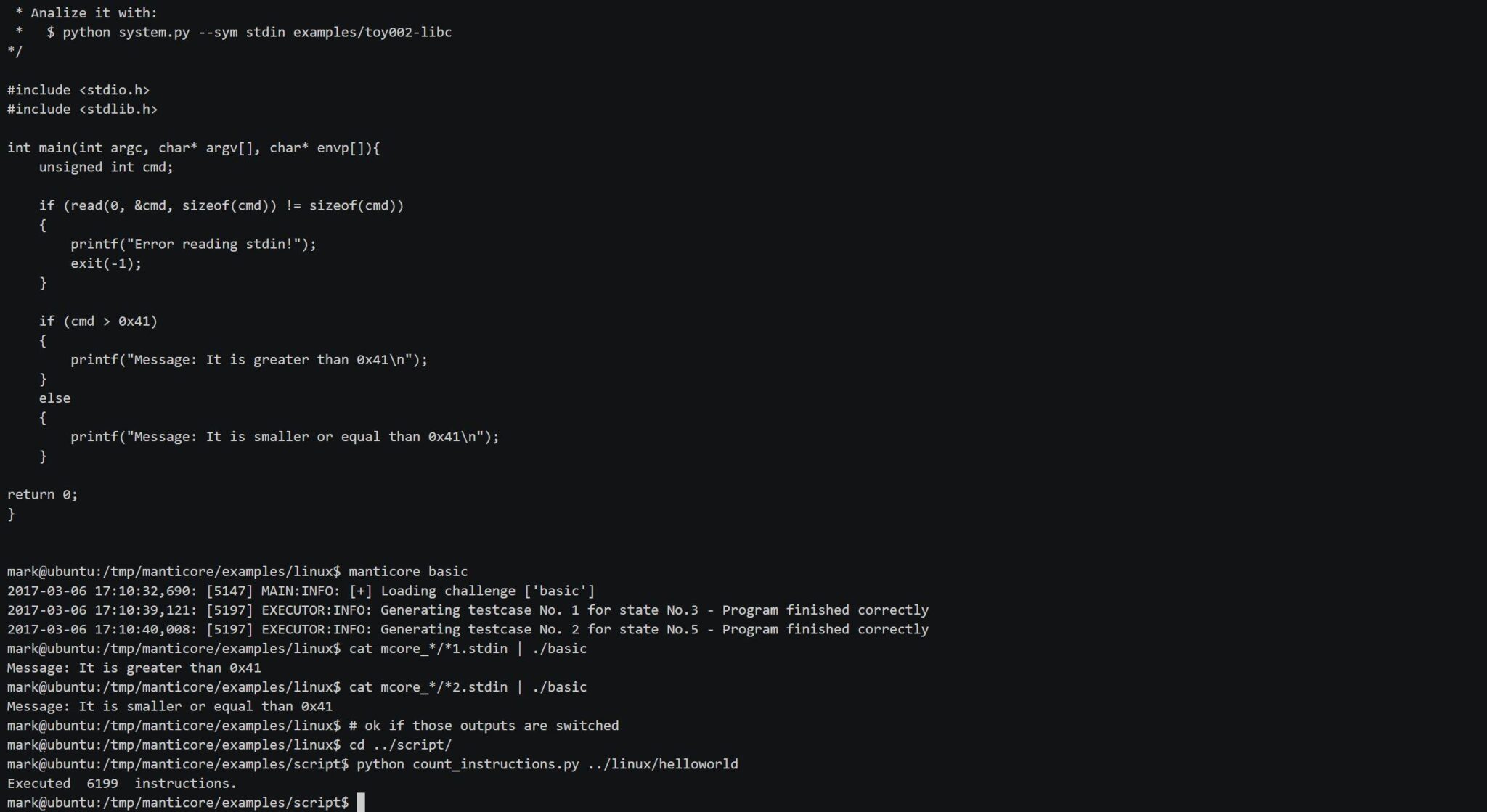
# Install system dependencies
sudo apt-get update && sudo apt-get install z3 python-pip -y
python -m pip install -U pip
# Install manticore and its dependencies
git clone https://github.com/trailofbits/manticore.git && cd manticore sudo pip install .
# Build the examples
cd examples/linux
make
# Use the Manticore CLI
manticore basic
cat mcore_*/*1.stdin | ./basic
cat mcore_*/*2.stdin | ./basic
# Use the Manticore API
cd ../script
python count_instructions.py ../linux/helloworld
Usage
$ manticore ./path/to/binary # runs, and creates a mcore_* directory with analysis results
Tutorial
Demo
Copyright (C) 2018 trailofbits
Source: https://github.com/trailofbits/







