mimikatz v2.2.0-20220919 releases: A little tool to play with Windows security

Mimikatz is an open-source gadget written in C, launched in April 2014. It is very powerful, support from the Windows system memory to extract clear text password, hash, PIN code, and Kerberos credentials, and pass-the-hash, pass-the-ticket, build Golden tickets, and other hacking technology. It comes in two flavors: x64 or Win32, depending on your windows version (32/64 bits).
The Win32 flavor cannot access 64 bits of process memory (like lsass) but can open 32 bits minidump under Windows 64 bits.
Some operations need administrator privileges or SYSTEM token, so be aware of UAC from Vista version.
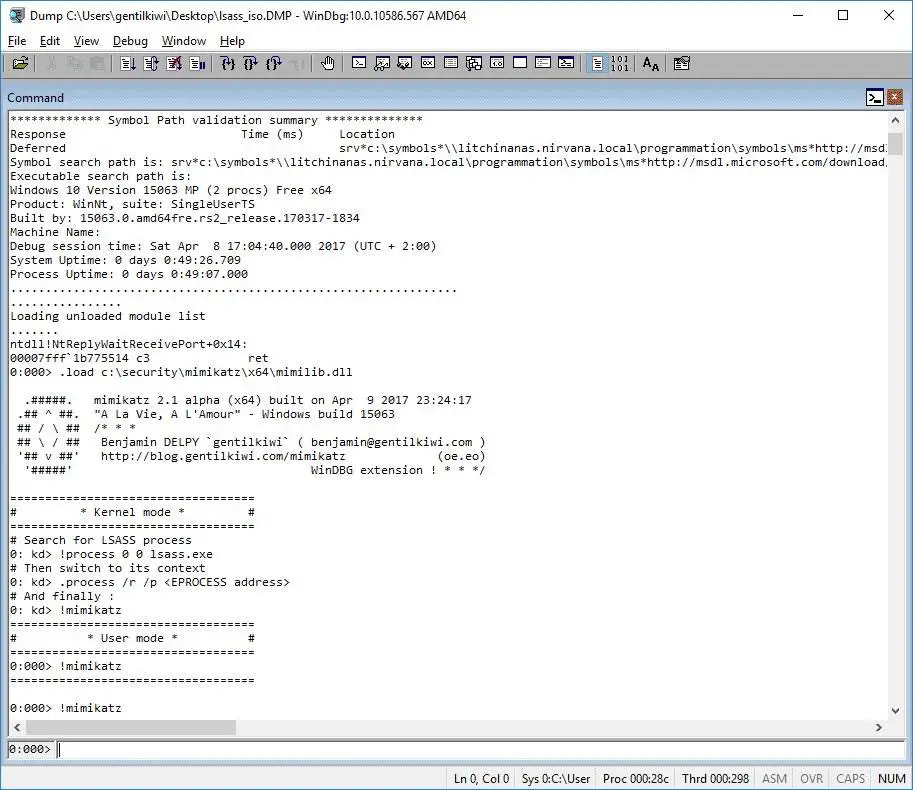
And windbg together, it can even read the virtual machine system password credentials.
Modules
- standard
- privilege
- crypto
- sekurlsa
- kerberos
- lsadump
- vault
- token
- event
- ts
- process
- service
- net
- misc
- library mimilib
- driver mimidrv
Changelog v2.2.0-20220919 Windows 365 Web passwords fix
-
[legacy] Backport djoin parser & citrix SSO password extractor
Should read
Preventing Mimikatz steal Windows system password
[Tips] Using mimikataz on penetration testing






