mitmproxy v10.1.4 releases: An interactive TLS-capable intercepting HTTP proxy
mitmproxy
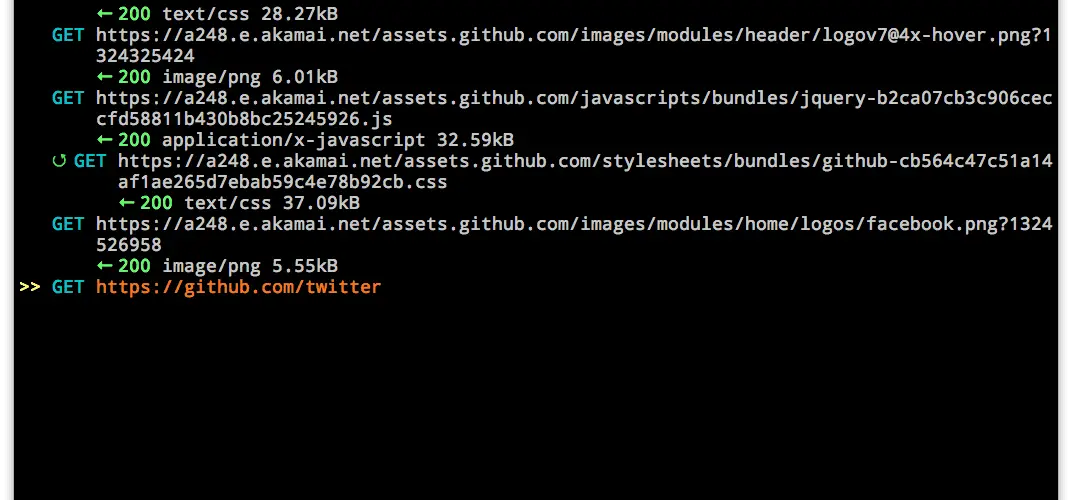
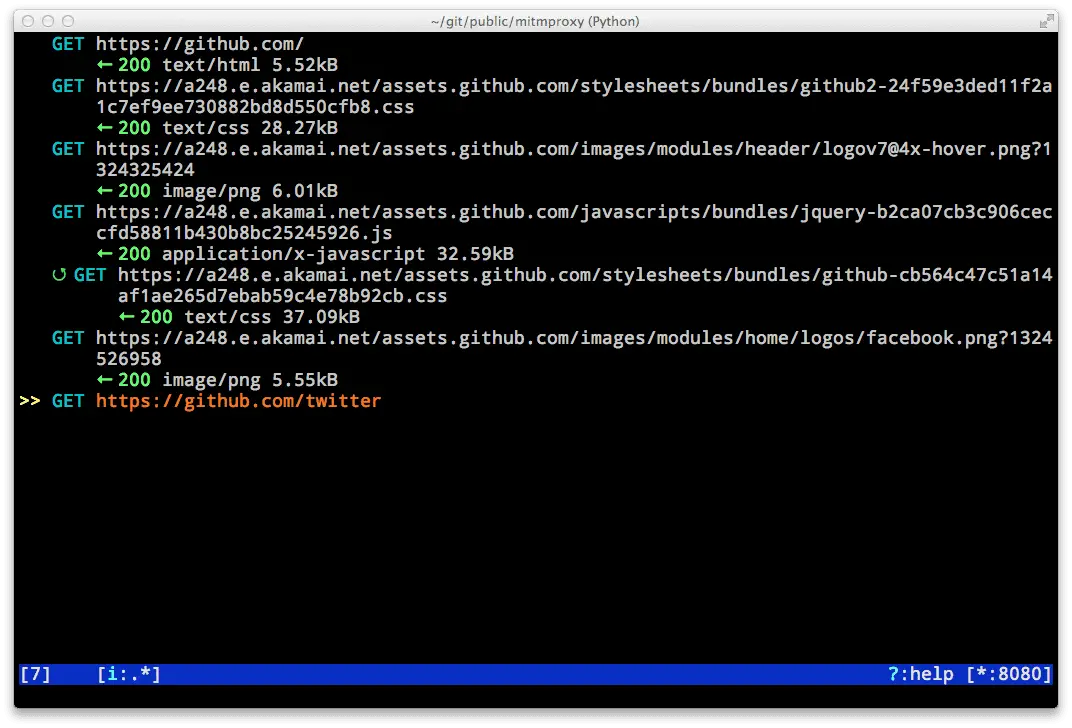
mitmproxy is an interactive, SSL-capable intercepting proxy with a console interface.
mitmdump is the command-line version of mitmproxy. Think tcpdump for HTTP.
mitmweb is a web-based interface for mitmproxy.
pathoc and pathod are perverse HTTP client and server applications designed to let you craft almost any conceivable HTTP request, including ones that creatively violate the standards.
Features
- Intercept HTTP & HTTPS requests and responses and modify them on the fly
- Save complete HTTP conversations for later replay and analysis
- Replay the client-side of an HTTP conversations
- Replay HTTP responses of a previously recorded server
- Reverse proxy mode to forward traffic to a specified server
- Transparent proxy mode on OSX and Linux
- Make scripted changes to HTTP traffic using Python
- SSL/TLS certificates for interception are generated on the fly
- And much, much more…
Changelog v10.1.4
- Fix a hang/freeze in the macOS distributions when doing TLS negotiation. (#6480, @mhils)
- Update savehar addon to fix creating corrupt har files caused by empty response content (#6459, @lain3d)
- Update savehar addon to handle scenarios where “path” key in cookie attrs dict is missing. (#6458, @pogzyb)
- Add
server_replay_extraoption to serverplayback to define behaviour when replayable response is missing. (#6465, @dkarandikar)
Download & Tutorial
Copyright (c) 2013, Aldo Cortesi. All rights reserved.






