Offensive Software Exploitation (OSE) Course
Offensive Software Exploitation (OSE) Course
This repository is for the Offensive Software Exploitation Course I am teaching at Champlain College and currently doing it for free online (check the YouTube channel for the recordings). Most of the slide notes I used are already shared on HTID Course, but the labs were fully created by myself. I used publically available resources and software to explain each of the weaknesses covered, so there is nothing here that you cannot find online.
Vulnerable Software
The vulnerable software I used is also online and can be found at Exploit-db. I also used Stephen Bradshaw’s VulnServer, plus maybe some other simple code that I prepared. Please check each lab for the software used in that specific lab and from where to download it.
Tool(s) Required
All of the tools used are free and could be downloaded from the URLs below.
- Immunity Debugger: download
- Kali Linux: download
- CFF Explorer: download
- PE-bear: download
- Ghidra: download
- IDA Pro: download
- x64dbg: download
- Microsoft SysInternals Suite: download
- CAPA by FireEye FLARE Team: download
- NetCat: download
- Others!
Target(s) Used
- Download a Windows 10 VM from Microsoft VMs (currently using Version 1809 Build 17763.1339) here. This will be used for most of the labs, except for the EggHunter lab, I used a Windows 7 VM, also from Microsoft VMs (currently offline so check archive.org).
- All the targeted software is Intel/AMD 32-bit unless otherwise instructed.
Table of Contents:
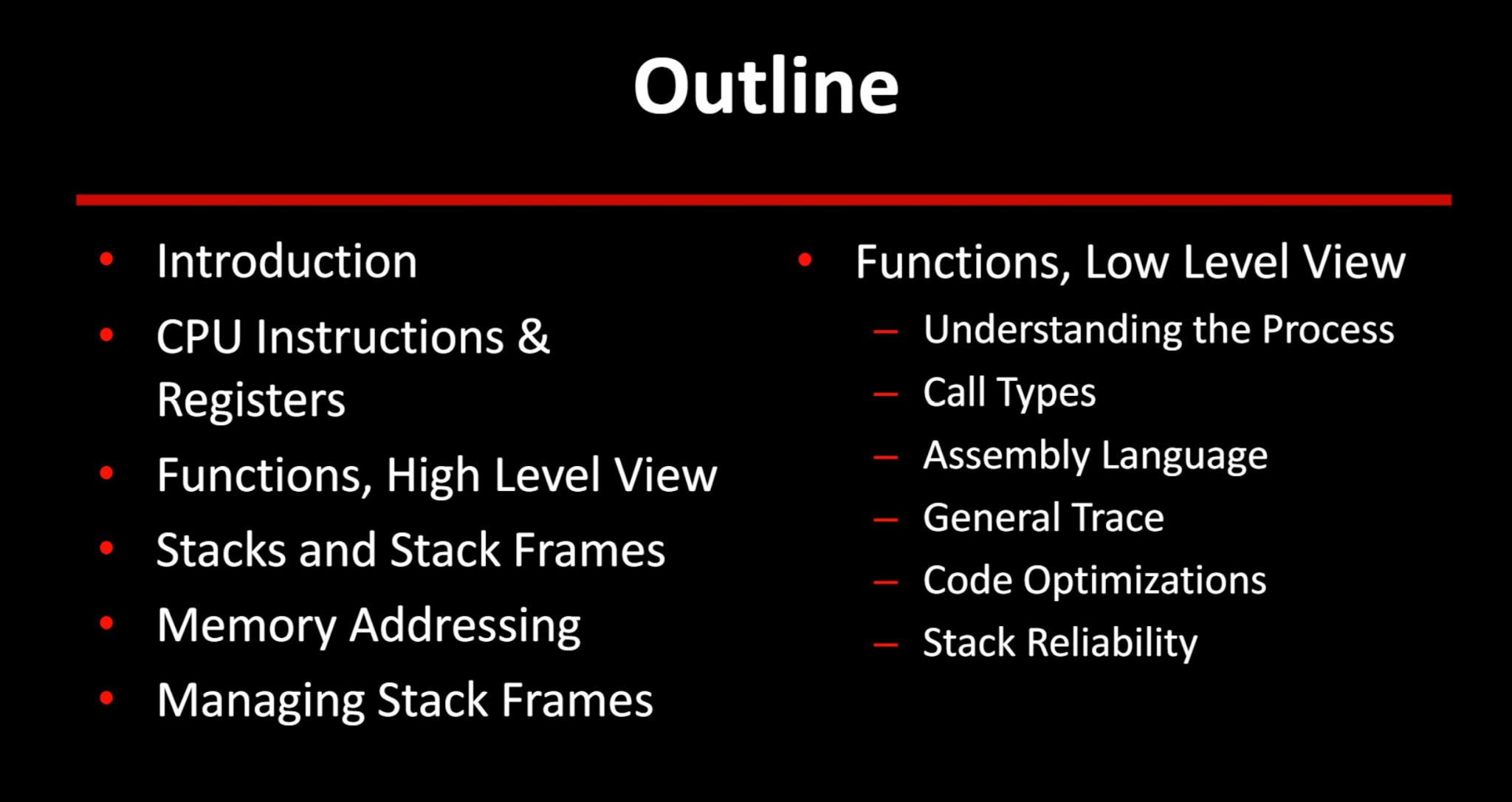
The topics that will be covered in this course are:
- The Basics (PE Format, DLLs, etc)
- Bug Hunting and Fuzzing
- Intro. to Memory Corruption and Buffer Overflows
- Metasploit
- Mitigation Techniques
- SEH and Jumping Strategies
- Egghunter
- Return Oriented Programming (ROP)
- Post Exploitation
- Manual Code Injection
- Intro. to Assembly x86 and x64 (please check-update #3 for this part)
- Reverse Engineering (please check-update #3 for this part)
Video Recordings:
Useful Resources:
- The number one resource is the Corelan Team’s blog, Corelan Team
- Introductory Intel x86, OpenSecurityTraining





