In the ever-evolving landscape of cybersecurity, staying ahead of threats requires more than just antivirus software and firewalls. It demands a comprehensive understanding of the tactics, techniques, and procedures (TTPs) employed by malicious actors. OpenCTI, an open-source platform designed to manage and analyze cyber threat intelligence (CTI), emerges as a powerful tool in this arena.
What is OpenCTI?
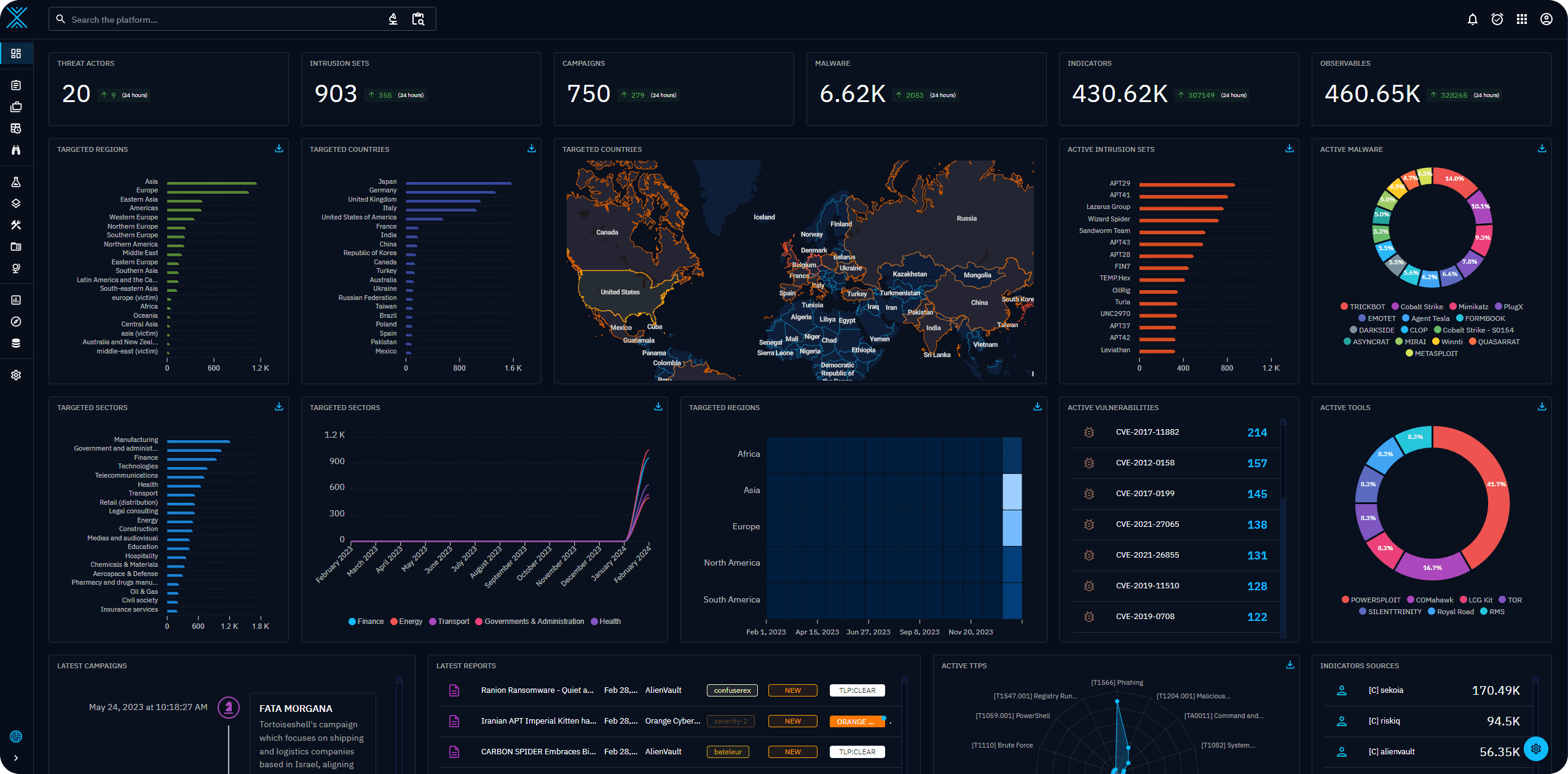
OpenCTI is a modern web application built to help organizations structure, store, and visualize both technical and non-technical information about cyber threats. It leverages the STIX2 standard for data organization and boasts a user-friendly interface coupled with a robust GraphQL API.
Key Features and Benefits
- STIX2 Compliance: OpenCTI’s adherence to the STIX2 standard ensures seamless integration with other CTI tools and platforms, fostering a collaborative approach to threat intelligence sharing.
- Knowledge Graph: The platform’s knowledge graph model enables analysts to visualize relationships between different pieces of information, uncovering hidden connections and patterns that might otherwise go unnoticed.
- MITRE ATT&CK Integration: OpenCTI seamlessly integrates with the MITRE ATT&CK framework, providing a structured approach to understanding and classifying adversary behavior.
- Customizable Datasets: Organizations can tailor OpenCTI to their specific needs by implementing their own datasets, ensuring the platform aligns with their unique threat landscape.
- Data Import and Export: OpenCTI facilitates both the import and export of data in various formats (CSV, STIX2 bundles), promoting interoperability and flexibility.
- Connector Ecosystem: A growing number of connectors are being developed to accelerate interactions between OpenCTI and other security tools like MISP, TheHive, and more.
- Inference Engine: OpenCTI’s inference engine can automatically infer new relationships from existing data, aiding analysts in their investigations and threat modeling.
- Open Source and Community-Driven: The platform’s open-source nature encourages transparency, collaboration, and community-driven development.
Who Should Use OpenCTI?
OpenCTI is a valuable asset for a wide range of organizations, including:
- Security Operations Centers (SOCs): SOC teams can leverage OpenCTI to centralize threat intelligence, streamline incident response, and enhance threat-hunting capabilities.
- Threat Intelligence Teams: Dedicated threat intelligence analysts can utilize the platform to collect, analyze, and disseminate actionable CTI to stakeholders.
- Incident Responders: OpenCTI can assist incident responders in understanding the TTPs of an attack, aiding in containment, eradication, and recovery efforts.
- Researchers and Academics: The open-source nature of OpenCTI makes it an ideal platform for research and academic studies in the field of cybersecurity.
Getting Started with OpenCTI
OpenCTI provides extensive documentation and a demo instance to help users get acquainted with the platform. The releases are available on GitHub, and a rolling release package is generated from the master branch.
Support Our Threat Intelligence
If you find our CVE report and cybersecurity news helpful, consider supporting our work.
 Buy Me a Coffee
Buy Me a Coffee
