otseca: Open source security auditing tool

Open-source security auditing tool to search and dump system configuration.
Otseca is an open-source security auditing tool to search and dump system configuration. It allows you to generate reports in HTML or RAW-HTML formats.
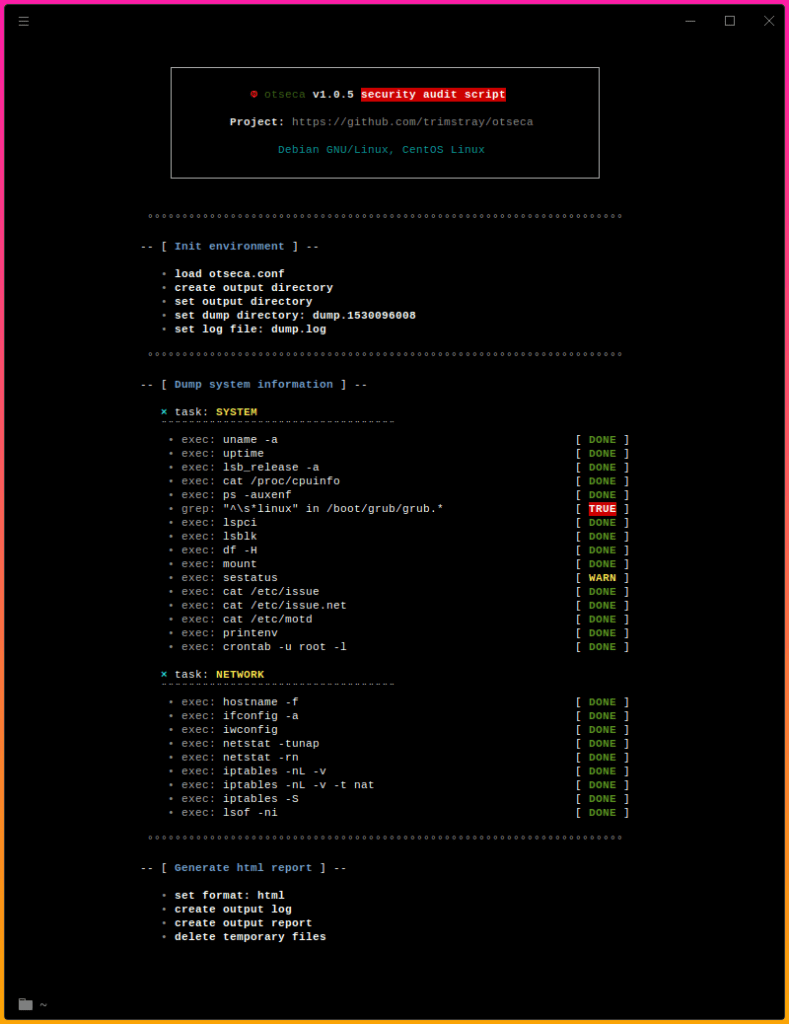
The basic goal is to get as much information about the scanned system as possible for later analysis. Otseca contains many predefined commands, however, nothing prevents you from creating your own according to your needs. In addition, it automates the entire information-gathering process.
After the scan finishes, a report is generated to examine specific nooks of the system.
The main goal
The main assumption of creating this tool was easier and faster delivery of commands sets to be performed on customer environments. As a result of such a scan, I wanted to get the most useful information about system components that will be subjected to penetration tests and audits at a later time.
For Whom
Otseca facilitates the collection of much important information about a given system.
It is useful for:
☑️ system administrators
☑️ security researchers
☑️ security professionals
☑️ pentesters
☑️ hackers
How it works
Tasks
Otseca divides his work into tasks. Each set of tasks perform defined commands (eg. from the file etc/otseca.conf). By default, six tasks are available: system, kernel, permissions, services, network, distro and external.
By default, all tasks are performed but you can specify them with the –tasks parameter giving one or many tasks as an argument. For example:
otseca --ignore-failed --tasks system,kernel
Commands
They are actual commands executed from the configuration file grouped into tasks.
Here is an example of a network task containing several built-in commands:
Submodules
Submodules are built-in functions that perform the commands described above. Here is submodules list:
- _exec – init standard commands, eg. _exec ls -l /etc/rsyslog.conf
- _grep – is responsible for searching for strings in files, eg. _grep max_log_file /etc/audit/auditd.conf
- _stat – collects information about files, eg. _stat /etc/ssh/sshd_config
- _sysctl – compares the values of the kernel parameters, eg. _sysctl fs.suid_dumpable 1
- _systemctl – checks the operation of services, eg. _systemctl httpd
Install
Use
Copyright (C) 2018 trimstray
Source: https://github.com/trimstray/






