PacBot v2.0 releases: compliance monitoring, compliance reporting and security automation for the cloud

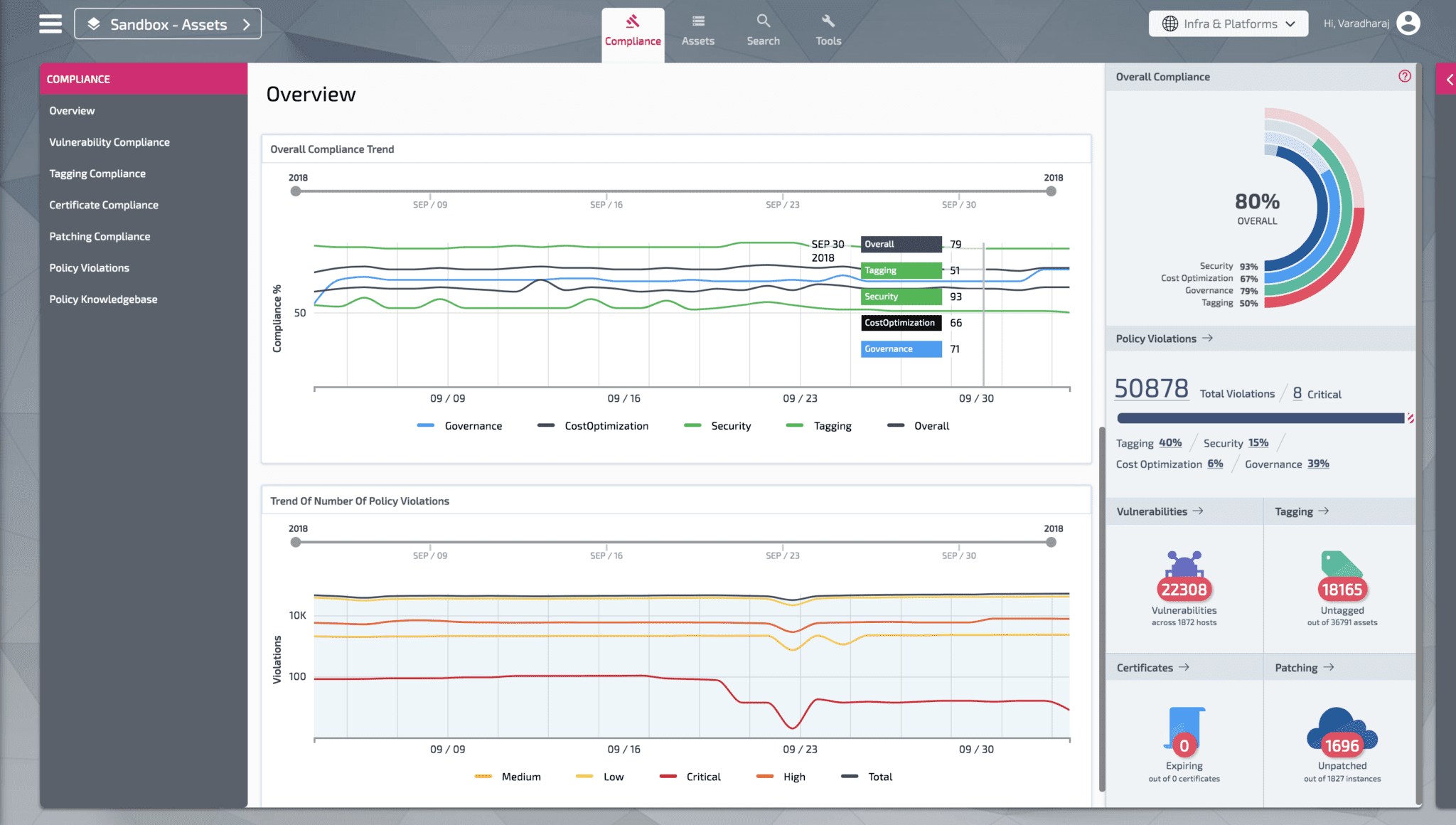
Policy as Code Bot (PacBot) is a platform for continuous compliance monitoring, compliance reporting and security automation for the cloud. In PacBot, security and compliance policies are implemented as code. All resources discovered by PacBot are evaluated against these policies to gauge policy conformance. PacBot auto-fix framework provides the ability to automatically respond to policy violations by taking predefined actions. PacBot packs in powerful visualization features, it gives a simplified view of compliance and makes it easy to analyze and remediate policy violations. PacBot is more than a tool to manage cloud misconfiguration, it is a generic platform that can be used to do continuous compliance monitoring and reporting for any domain.

PacBot’s plugin-based data ingestion architecture allows ingesting data from multiple sources. We have built plugins to pull data from Qualys Vulnerability Assessment Platform, Bitbucket, TrendMicro Deep Security, Tripwire, Venafi Certificate Management, Redhat Satellite, Spacewalk, Active Directory, and few other customs built internal solutions. We are working to open source these plugins and other tools as well. You could write rules based on data collected by these plugins to get a complete picture of your ecosystem and not just cloud misconfigurations. For example, within T-Mobile, we have implemented a policy to mark all EC2 instances with one or more severity 5 (CVSS score > 7) vulnerabilities as non-compliant.
How Does It Work?
Assess -> Report -> Remediate -> Repeat
Assess -> Report -> Remediate -> Repeat is PacBot’s philosophy. PacBot discovers resources and assesses these resources against the policies implemented as code. All policy violations are recorded as an issue. Whenever an Auto-Fix hook is available with the policies, those auto-fixes are executed when the resources fail the evaluation. Policy violations cannot be closed manually, the issue has to be fixed at the source and PacBot will mark it closed in the next scan. Exceptions can be added to policy violations. Sticky exceptions (Exception based on resource attribute matching criteria) can be added to exempt similar resources that may be created in future.
PacBot’s Asset Groups are a powerful way to visualize compliance. Asset Groups are created by defining one or more target resource’s attribute matching criteria. For example, you could create an Asset Group of all running assets by defining criteria to match all EC2 instances with attribute instancestate.name=running. Any new EC2 instance launched after the creation of the Asset Group will be automatically included in the group. In PacBot UI you can select the scope of the portal to a specific asset group. All the data points shown in the PacBot portal will be confined to the selected Asset Group. Team’s using cloud can set the scope of the portal to their application or org and focus only on their policy violations. This reduces noise and provides a clear picture to our cloud users. At T-Mobile, we create Asset Group per stakeholder, per application, per AWS account, per Environment etc.
Asset groups are not for just setting the scope of the data shown in the UI. It can be used to scope the rule executions as well. PacBot policies are implemented as one or more rules. These rules can be configured to run against all resources or a specific Asset Group. The rules will evaluate all resources in the asset group configured as the scope for the rule. This provides an opportunity to write policies which are very specific to an application or org. A good example is, some of the teams would like to enforce additional tagging standards apart from the global ones set for all of the cloud. They implement this policy with their custom rules and configure that to run only on their assets.
PacBot Key Capabilities
- Continuous compliance assessment.
- Detailed compliance reporting.
- Auto-Fix for policy violations.
- Omni Search – Ability to search all discovered resources.
- Simplified policy violation tracking.
- Self-Service portal.
- Custom policies and custom auto-fix actions.
- Dynamic asset grouping to view compliance.
- Ability to create multiple compliance domains.
- Exception management.
- Email Digests.
- Supports multiple AWS accounts.
- Completely automated installer.
- Customizable dashboards.
- OAuth Support.
- Azure AD integration for login.
- Role-based access control.
- Asset 360 degrees.
Changelog v2.0
What is released as a part of 2.0:
Starting with Release 2.0, PacBot supports Multi Cloud Compliance (AWS & Azure). This enables us to see AWS & Azure Compliance in single place.
PacBot still runs on AWS Infrastructure, but now has the capability to collect data from AWS & Azure.
Users can see security-center/policy-compliance and custom polices in PacBot.PacBot collects data for 25+ Azure Services, including computing, storage, databases, networking and Security Center services.
PacBot supports the following dashboards for visualizing Azure data
- Azure Compliance Overview
- Asset Overview
- Asset Listing
- Asset 360 view
- Tagging
- Policy Knowledgebase
- Compliance Details
- Omni Search
Azure Policies
50+ Azure policies are now included with PacBot. Details of these policies can be found here.
Installation Steps
PacBot utilizes Service Principals to enable Azure data collection. A Service Principal must be provisioned in each tenant to have read access to the services in subscriptions to be monitored.
To enable Azure Compliance in PacBot, configure the client ID and secret ID of the service principal in each tenant as follows:
- Step1: Set ENABLE_AZURE = True in local.py
- Sep2: Add Azure tenants as shown below
AZURE_TENANTS = [
{
‘tenantId’: “t111”,
‘clientId’: “c111”,
‘secretId’: “s111”
},
{
‘tenantId’: “t222”,
‘clientId’: “c222”,
‘secretId’: “s222”
},
]Additional Features
- Upgraded to latest Terraform version(0.12) for PacBot installer.
- Silent option to install PacBot without interactive input.
- User can now omit reading input from console by preconfiguring inputs in the local.py script.
- During install/destroy/redeploy, give optional parameter –silent to install silently.
Issues Closed:






