Polaris v8.5.1 releases: open source policy engine for Kubernetes
Polaris
Securing workloads in Kubernetes is an important part of overall cluster security. The overall goal should be to ensure that containers are running with as minimal privileges as possible. This includes avoiding privilege escalation, not running containers with a root user, not giving excessive access to the host network, and using read-only file systems wherever possible.
A pod running with the hostNetwork attribute enabled will have access to the loopback device, services listening on localhost, and could be used to snoop on the network activity of other pods on the same node. There are certain examples where setting hostNetwork to true is required, such as deploying a networking plugin like Flannel.
Setting the hostPort attribute on a container will ensure that it is accessible on that specific port on each node it is deployed to. Unfortunately, when this is specified, it limits where a pod can actually be scheduled in a cluster.
Much of this configuration can be found in the securityContext attribute for both Kubernetes pods and containers. Where configuration is available at both a pod and container level, Polaris validates both.
Polaris is an open-source policy engine for Kubernetes that validates and remediates resource configuration. It includes 30+ built-in configuration policies, as well as the ability to build custom policies with JSON Schema. When run on the command line or as a mutating webhook, Polaris can automatically remediate issues based on policy criteria.
Polaris can be run in three different modes:
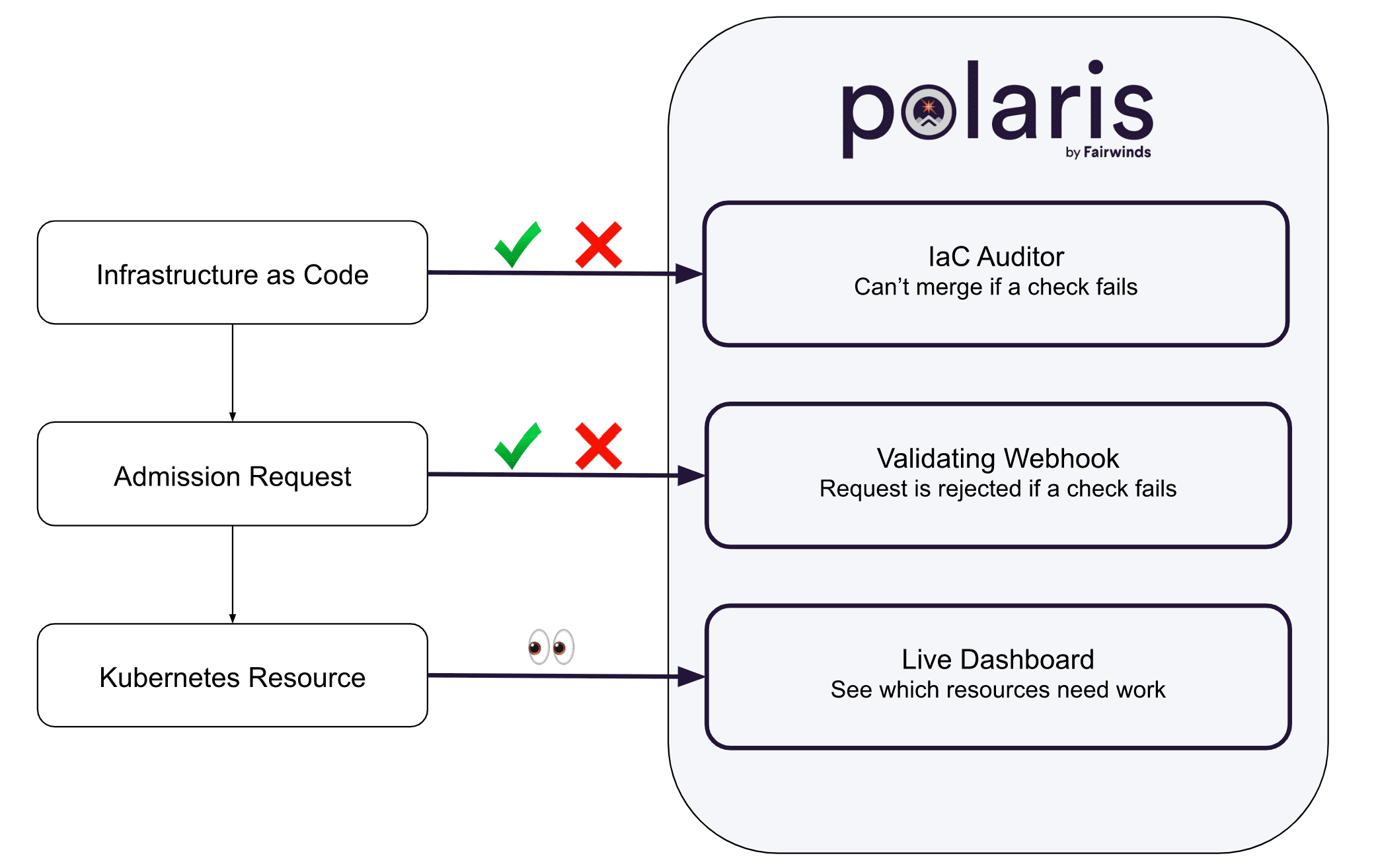
- As a dashboard – Validate Kubernetes resources against policy-as-code.
- As an admission controller – Automatically reject or modify workloads that don’t adhere to your organization’s policies.
- As a command-line tool – Incorporate policy-as-code into the CI/CD process to test local YAML files.
Changelog v8.5.1
Install & Use
Copyright 2019 FairwindsOps Inc






