PowerHuntShares
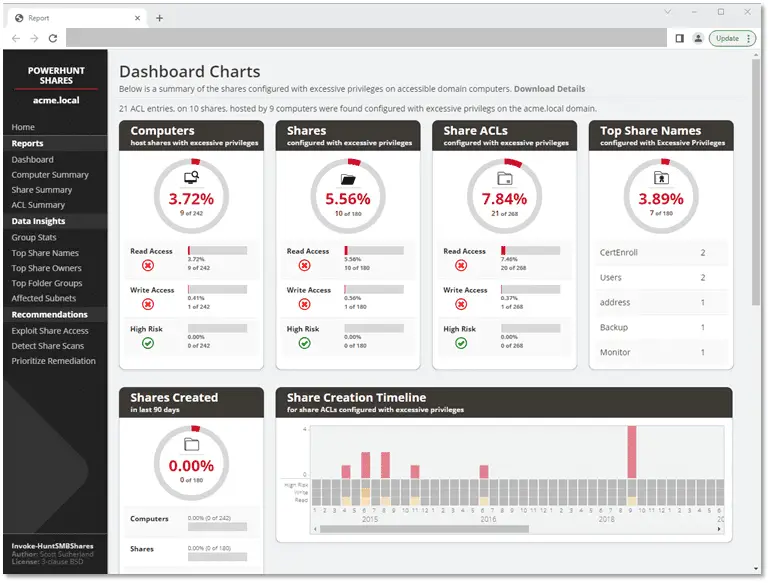
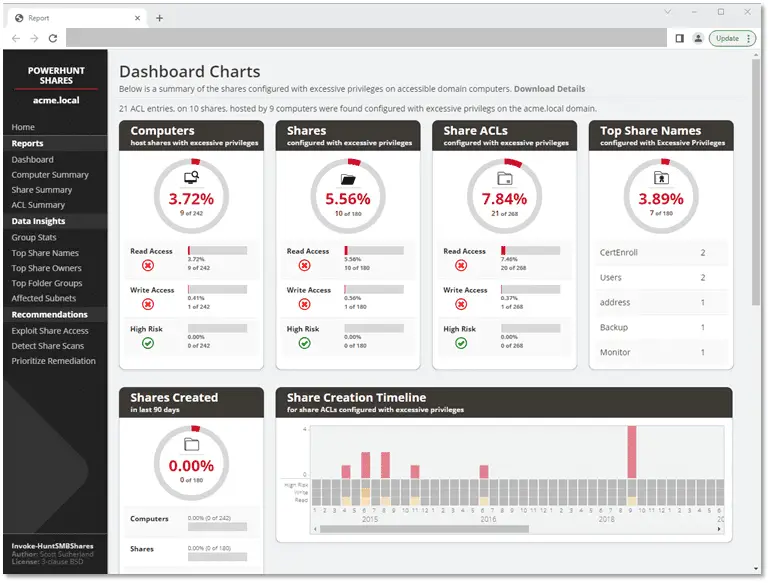
PowerHuntShares is designed to automatically inventory, analyze, and report excessive privilege assigned to SMB shares on Active Directory domain joined computers.
It is intended to help IAM and other blue teams gain a better understanding of their SMB Share attack surface and provide data insights to help naturally group-related share to help streamline remediation efforts at scale.
It supports functionality to:
- Authenticate using the current user context, a credential, or clear text user/password.
- Discover accessible systems associated with an Active Directory domain automatically. It will also filter Active Directory computers based on available open ports.
- Target a single computer, list of computers, or discovered Active Directory computers (default).
- Collect SMB share ACL information from target computers using PowerShell.
- Analyze collected Share ACL data.
- Report summary reports and excessive privilege details in HTML and CSV file formats.
Excessive SMB share ACLs are a systemic problem and an attack surface that all organizations struggle with. The goal of this project is to provide a proof concept that will work towards building a better share collection and data insight engine that can help inform and prioritize remediation efforts.
Bonus Features:
- Generate directory listing dump for configurable depth
- Search for file types across discovered shares
PowerHuntShares will inventory SMB share ACLs configured with “excessive privileges” and highlight “high risk” ACLs. Below is how those are defined in this context.
Excessive Privileges
Excessive read and write share permissions have been defined as any network share ACL containing an explicit ACE (Access Control Entry) for the “Everyone”, “Authenticated Users”, “BUILTIN\Users”, “Domain Users”, or “Domain Computers” groups. All provide domain users access to the affected shares due to privilege inheritance issues. Note there is a parameter that allow operators to add their own target groups.
Below is some additional background:
- Everyone is a direct reference that applies to both unauthenticated and authenticated users. Typically only a null session is required to access those resources.
- BUILTIN\Users contains Authenticated Users
- Authenticated Users contains Domain Users on domain-joined systems. That’s why Domain Users can access a share when the share permissions have been assigned to “BUILTIN\Users”.
- Domain Users is a direct reference
- Domain Users can also create up to 10 computer accounts by default that get placed in the Domain Computers group
- Domain Users that have local administrative access to a domain-joined computer can also impersonate the computer account.
Download & Use
Copyright (c) 2022, NetSPI All rights reserved.