In a recent cybersecurity incident, Qilin ransomware affiliates successfully compromised a Managed Service Provider (MSP) by exploiting a vulnerability in their ScreenConnect Remote Monitoring and Management (RMM) tool. This breach enabled the attackers to launch ransomware attacks on the MSP’s customers, highlighting the severe consequences of supply chain attacks.
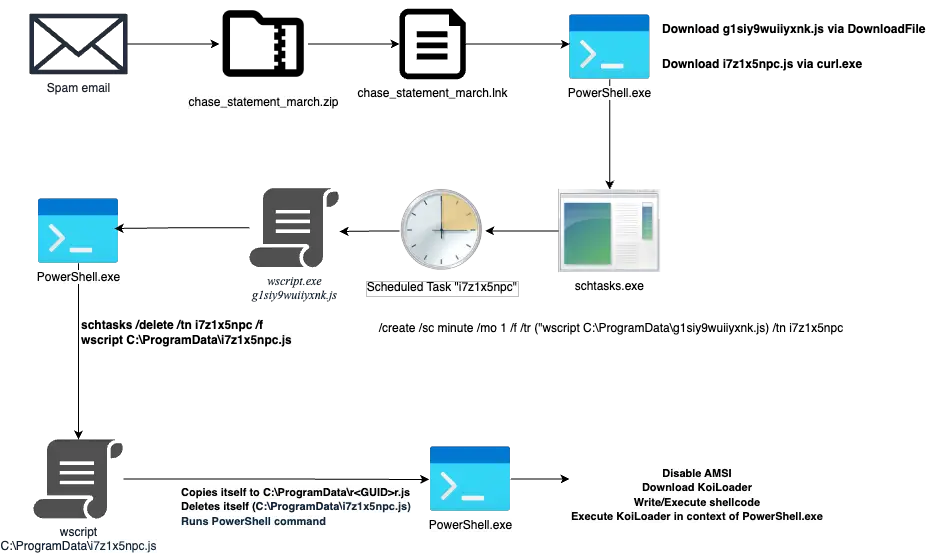
The Sophos MDR’s threat Intelligence team has attributed this incident with high confidence to a ransomware affiliate tracked as STAC4365. The attack, which occurred in late January 2025, leveraged a sophisticated phishing campaign. The initial point of entry was a carefully crafted phishing email disguised as an authentication alert for the MSP’s ScreenConnect RMM tool.
The attackers employed a spear-phishing technique to target an MSP administrator. “That email resulted in Qilin ransomware actors gaining access to the administrator’s credentials-and launching ransomware attacks on the MSP’s customers,” the report states. The phishing campaign used tactics consistent with those observed in previous attacks dating back to late 2022. These tactics included the use of phishing sites built with the evilginx open-source adversary-in-the-middle attack framework, designed to steal credentials and session cookies and bypass multi-factor authentication (MFA).

The phishing email received by the targeted administrator | Image: Sophos
In this particular incident, the attackers utilized fake ScreenConnect domains to proxy the legitimate login process. The report elaborates on the attack chain: “Once the administrator clicked on the login link on the email to review the authentication, they were redirected to a malicious phishing site, cloud.screenconnect[.]com.ms, that masqueraded as the legitimate ScreenConnect login page.” By intercepting the administrator’s credentials entered into the fake site, “the attackers were able to intercept those inputs,” gaining unauthorized access to the legitimate ScreenConnect Cloud portal with super administrator privileges.
This access granted the attackers extensive control, enabling them to deploy Qilin ransomware across multiple of the MSP’s managed customers.
Qilin, a Ransomware-as-a-Service program in operation since 2022 (previously known as “Agenda”), is known for recruiting affiliates on Russian-language cybercrime forums. The Qilin group uses a Tor-hosted data-leak site and, more recently, an open internet site named “WikiLeaksV2” to pressure victims into paying ransoms. The WikiLeaksV2 site, linked in the ransom notes, is hosted on an IP address with a history of malicious activity.
The attack involved several stages, including initial access via phishing, persistence through the deployment of a malicious ScreenConnect instance, lateral movement using legitimate tools, data collection, exfiltration, defense evasion, and ultimately, the deployment of Qilin ransomware.
The attackers employed various defense evasion techniques, such as using Incognito mode in Chrome to hinder forensic analysis and removing tools post-execution. They also targeted backups to impede recovery efforts and modified boot options to facilitate Safe Mode with Networking.
The attackers’ sophisticated use of phishing techniques and the exploitation of legitimate tools for malicious purposes highlight the need for robust cybersecurity measures, including:
- Enhanced email security to prevent phishing attacks
- Multi-factor authentication (MFA) to protect against credential compromise
- Network segmentation to limit lateral movement
- Regular security audits and vulnerability management
- Endpoint detection and response (EDR) solutions to detect and respond to malicious activity
- Robust backup and recovery plans